Black Hat 2024: SOC in the NOC
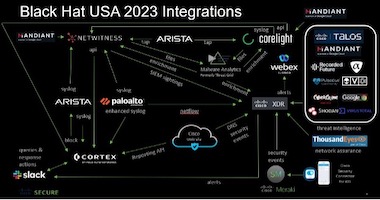
The Black Hat Network Operations Center (NOC) provides a high-security, high-availability network in one of the most demanding environments in the world: the Black Hat event. The NOC partners are selected by Black Hat, with Arista, Cisco, Corelight