No business is an island. With apologies to John Donne, it’s a sentiment even truer today than in his 17th-century writings. We all rely on others for survival. The ability to connect for a quick chat was much simpler in Donne’s era. Or was it?
Even if most of your employees are one place, it’s unlikely that all your partners, suppliers, and customers are within walking distance of your office. The ability to connect and collaborate, across town or across time zones, is becoming a standard business need.
The best online meetings mean you can meet with anyone, anywhere, anytime. Success depends on connections. But it’s not enough just to have the ability to connect. The right connections matter.

When it’s your business success is on the line, “good enough” tech isn’t enough. And let’s face it, all conferencing tools are not created equal. But does it really matter? Aren’t they close enough? Consider some of the most basic risks of choosing the wrong tool – reduced productivity, security risks, limited scalability, user dissatisfaction, complex management, your organization’s reputation…
So who do you trust? Rely on secure, scalable meetings with Cisco WebEx — the trusted industry leader in video and web conferencing. See the Gartner Magic Quadrant for Meeting Solutions.
But we’re not sitting still. Just like you need to innovate to stay ahead of your competitors, so do we. Our engineering teams are like sharks – they never stop moving. They’re constantly innovating with a central focus on simplifying the meeting experience while augmenting and improving it.
7 Reasons to Trust Your Meetings to Cisco WebEx
#1 113 million professionals aren’t wrong
There are a lot of collaboration solutions from which to choose. But there’s only one proven leader. Cisco has twice the share of any competitor in video and web conferencing. And 95% of Fortune 500 companies are using video-enabled Cisco Collaboration solutions.1
Consider a single month in the life of WebEx:
- 27+ million meetings hosted per month
- 5+ billion global meeting minutes per month
- 113+ million meeting attendees per month

Numbers tell a good story (a really good one), but there are more dimensions to the whole story. Here’s another one: Gartner has positioned Cisco as a leader in the latest Gartner Magic Quadrant for Meeting Solutions, released last week. Gartner evaluated a variety of criteria for each of the 14 vendors in the report, positioning Cisco highest and furthest for “Ability to Execute” and “Completeness of Vision” for meeting solutions. Download the full report.
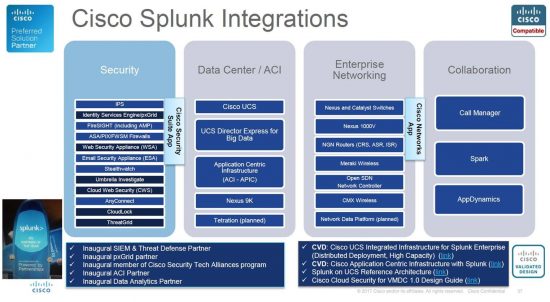
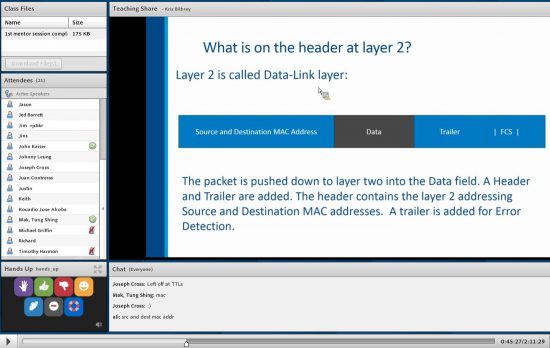
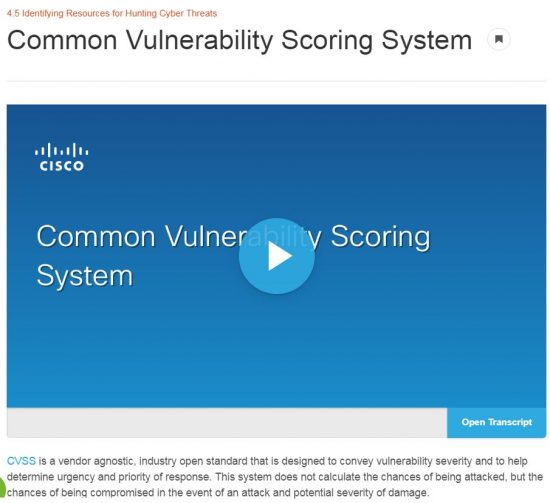
#2 No one knows security better than Cisco
 No matter your industry, no matter the size of your business, security has to be a top technology priority. Conferencing services are no different. In fact, they must provide multiple layers of security—from scheduling to participant authentication to content sharing.
No matter your industry, no matter the size of your business, security has to be a top technology priority. Conferencing services are no different. In fact, they must provide multiple layers of security—from scheduling to participant authentication to content sharing.
This is another big advantage of Cisco products – we know the network, at every layer and in every aspect. We don’t rely on someone else to figure out security for us. As a leader in both collaboration services and network security, we don’t take this lightly anywhere – including for your meetings. It’s a huge part of our business and our commitment to our customers.
WebEx meetings happen in the Cisco Collaboration Cloud, a global, enterprise-scale network designed specifically for highly secure delivery of on-demand applications. It offers a scalable architecture, consistent availability, and multilayer tenant security validated by rigorous independent audits.
#3 WebEx doesn’t limit you
Not all conferencing providers offer a global, full-service meeting experience. Some support only certain countries or regions—leading to patchwork solutions that don’t always integrate well.
Cisco WebEx offers online meetings with high-definition, reliable video, plus:
- 17 languages for connections worldwide
- Enterprise-grade availability, speed, and performance
- Support of global data centers
- Bandwidth-management settings
- A consistent, high-quality experience across devices
- Deployment and solution flexibility

You’re a rare bird if all your meetings are identical – with the same number of people attending from the same locations using the same devices each time. I’ve attended meetings from my laptop at the office, an MX Series system in a conference room, my dad’s PC, and via my mobile phone from the back seat of a motorcycle in Death Valley. (I don’t sit still very well.)
Cisco WebEx can meet all your conferencing needs, from simple meetings to big events and training sessions.
- Allow users to join with one touch from a browser, mobile device, or standards-based video system
- Host online events for up to 3,000 attendees or offer a webinar to 40,000 participants
- Train staff or partners with up to seven breakout rooms, and remotely support staff and customers
Think of it like this – instead of having to go to four stores to get the ingredients to make brownies, you can get everything in one place.
#4 People can focus on meetings – not the tech
 Complicated features or unreliable technology can get in the way of getting down to business. If the solution is hard to use or you have to learn a different process for every device you use, you’re wasting time. Not only your time but the time of your employees – and your customers and partners. It’s a productivity hit, but worse — when an experience leaves a bad impression on users, they’re not likely to use it again.
Complicated features or unreliable technology can get in the way of getting down to business. If the solution is hard to use or you have to learn a different process for every device you use, you’re wasting time. Not only your time but the time of your employees – and your customers and partners. It’s a productivity hit, but worse — when an experience leaves a bad impression on users, they’re not likely to use it again.
Usability features include:
- Easy scheduling directly from Microsoft Outlook
- Single-button join (a.k.a. “the green button”)
- Consistent user experience on any device and
- Easy to move from one device to another during a meeting
- Reliable meeting quality
Cisco WebEx’s user experience makes it simple to focus on the reason for the meeting and the people in it, not the technology.
#5 Get comprehensive, integrated solutions
If you’re like most organizations, you’ve felt the frustration of piecing together disparate technologies to solve a challenge. Another advantage of working with Cisco is that WebEx is part of the broad collaboration portfolio. Get a better video experience and stronger integration by using Cisco web conferencing and video endpoints together.
If you just need a basic meeting solution, WebEx has you covered. If you need more – today, or in the future, you’re covered. For example:
- Team collaboration tools like Cisco Spark provide workspaces where teams can centralize projects, conversations, and content. Cisco Spark also features group messaging, in-app calling, file sharing, and virtual whiteboarding.
- High-quality, innovative meeting room devices like Cisco Spark Board provide an all-in-one solution for wireless sharing, digital whiteboarding, and high-definition video conferencing.
- Our unified communications technology connects business communication systems and customer care solutions under one, integrated solution.
Cisco lets you define what you need based on your needs with flexible deployment models—on premises, cloud-based, or hybrid models—that you can shift as your needs shift.
#6 Attendee experience reflects your reputation
 The quality of your video conferencing experience makes an impression on attendees – clients, business partners, and even employees. You want to not only use the technology you choose to run the business but leverage it in your strategy to stay ahead of competitors. While lower-cost solutions look good on the shelf, there’s usually a reason for the reduced price tag. (Like tequila in a plastic bottle…)
The quality of your video conferencing experience makes an impression on attendees – clients, business partners, and even employees. You want to not only use the technology you choose to run the business but leverage it in your strategy to stay ahead of competitors. While lower-cost solutions look good on the shelf, there’s usually a reason for the reduced price tag. (Like tequila in a plastic bottle…)
Don’t risk the way others perceive your company in return for small, up-front cost savings. It could cost you far more in terms of clients and business limitations.
Best-in-class capabilities allow you to put your organization’s best foot (and face) forward. For example, WebEx offers:
- Dedicated, always-on personal meeting rooms
- Intelligent noise detection to reduce background noise
- Instant connect, whether for impromptu or scheduled meetings
- Host ability to automatically lock a meeting room, preview who is in the lobby, easily admit guests or choose an alternate host
- Meeting room options that let you brand or personalize rooms with avatars, images, and names at no extra cost
#7 Competitors can’t match WebEx
Don’t let the vendor checklists fool you. Anyone can create a checklist that makes their product look the best, whether for web conferencing or tequila. If you look at feature lists alone, you’ll see will miss the richness of the true product experience and capabilities. It’s not our checklists that are important – yours are. We can complete your checklist and actually deliver on it.
Learn more about Cisco WebEx.
Download the Gartner Magic Quadrant and Critical Capabilities for Meeting Solutions.
-
IDC MarketScape: Worldwide Enterprise Videoconferencing Equipment 2016 Vendor Assessment, Doc # US41304916, Jun 2016