I entered the United States Marine Corps as a communications radio repair guy, which sounds pretty easy, right? But once you get in country, none of that really matters and during three tours in support of Operation Iraqi Freedom I saw combat each time. Life has a way of always changing regardless of the plan you had set for it, and after 11 years with the military and an injury my plan of entering law enforcement had to be realigned.
At 30 years old, I decided to go back to school for Cyber Security & Information Systems – something many might write off just due to age alone. Most of my classmates had dreams of working for Cisco, and I was no different. So I set my eyes on the target, and went for it. Almost a year after graduation, after five interviews in six months, I finally began living the Cisco Life. I knew this is where I wanted to be because of their great culture, and an extremely supportive veteran community.
Eventually I was asked to speak at veteran events, and recently have been doing engagements with NC4ME (North Carolina 4 Military Employment) where I encourage employers (like Cisco!) and veterans to come together and showcase the unique skill-sets our military men and women have that benefit the workforce. Most people today have a stereotype in mind when they hear the word “veteran” – but I’m not Rambo, I look just like everyone else – so take a good look, because I am what a veteran looks like.
The military world is much different than the commercial world, it’s true, and this is why I do my best to translate the world of military life to that of the Cisco life. Veterans are trained to have an unshakable sense of determination and to work well under pressure – some of these brave men and women are very young, but they’ve commanded their peers through life threatening situations! This is a unique skill-set you’re not going to find from a college graduate.
Cisco is always looking for the best and the brightest, and the folks coming out of the military are just that. They have to be. Cisco is great at looking at veterans and breaking down those stereotypes. When I was hired, my team lead expressed to me that what impressed them most about my background and throughout my interviews was my attitude and confidence – two traits I learned in the military. I was confident in who I was and where I wanted to go in life. I was confident that, while I didn’t know everything, what I did know I knew well. Sit up straight, look people in the eyes, don’t be afraid to talk to people – that was just everyday life for us in the Marine Corps. Immediately, I felt at home with Cisco.
Two of my team members were also veterans, and there’s even a veteran’s mailer that has hundreds of us on it — Cisco is brimming with ex-military! Not to mention, there are get-togethers, luncheons, and lots of other opportunities to connect with your fellow veterans working at Cisco. The Veteran Mentor Program allows veterans to shadow their mentor as well to see if that particular position is something that interests them at Cisco and it’s been quite successful.
Many ask how I could overcome all that I have, or are maybe struggling to see the light in the tunnel for themselves. I speak to much of this when I meet with other veterans, and find the advice applies to everyone from time to time as life changes us all and we all go through moments of struggle.
1. Somewhere deep down within you is a fire, and if you feed it everything it will serve you well. Determination inside can get you what you need, be willing to do the work. Sometimes that’s not easy, but it’s worth it. Hard work always pays off, so it will eventually come to you. What drives you? What are you passionate about? Find that fire and fuel it – learn everything you can, surround yourself with positive people, and don’t stop until you’re exactly where you want to be!
2. If I can do it, you can do it. I’m a skinny, one-legged veteran that came from a poverty stricken family and worked my way up to where I am today – I’m successful because I never gave up. Sometimes the light at the end of the tunnel is far away, but you can get there. Just remembered what you’ve been trained to do – that will get you very far in life and in your career. The goals are not unattainable although you sometimes feel as if they are.
The things the military has trained us to do can get veterans through just about anything. Never been in the military? This still applies to you! What have you been TRAINED to do – everyone has a foundation to their training. What is that and how can you apply it to get to your next step? Just do the work, and use the advice of mentors, parents and friends to help guide you.
3. It’s never too late to start. I went back to school when I was 30 for my four year degree. Sometimes you have to rebuild your entire plan when life throws you a curve-ball. You just need to adjust. Re-evaluate, develop a new plan, and then go for it. Many people get stuck on how it’s supposed to be or how they envisioned their life being vs. being able to realign their course of action – take what you can from the experience, both positive and negative, and grow from there.
Your plan should be ever-evolving as life is evolving around you so be ready to change at any point. If you don’t change and progress, you get left behind.
Are you ready to step into the future? Join us!
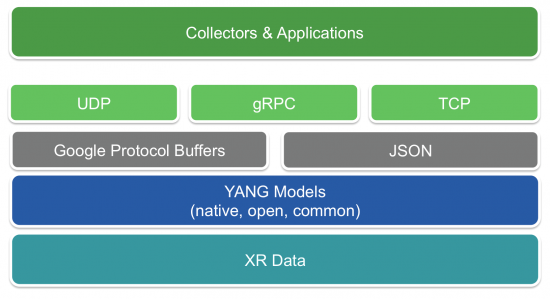
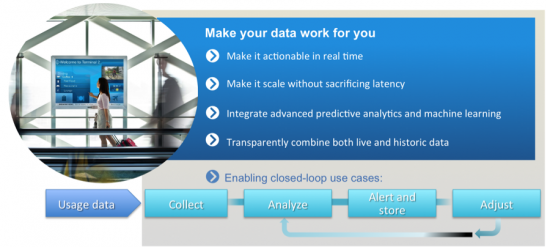 Connected Data Analytics
Connected Data Analytics


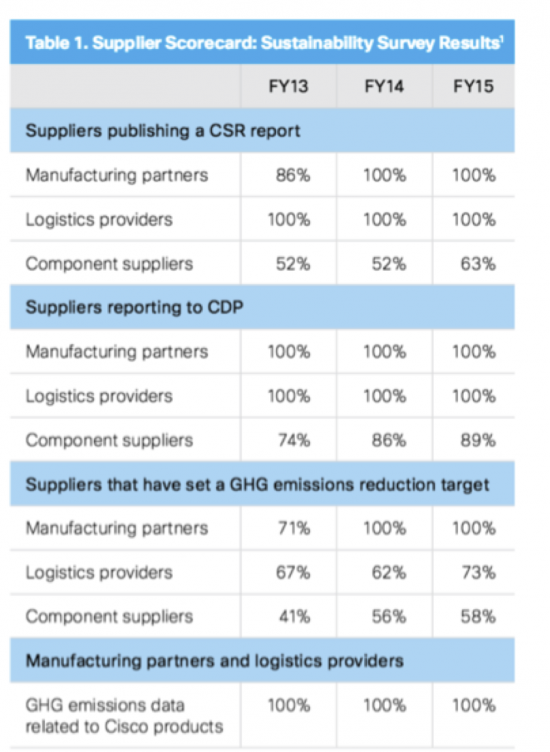
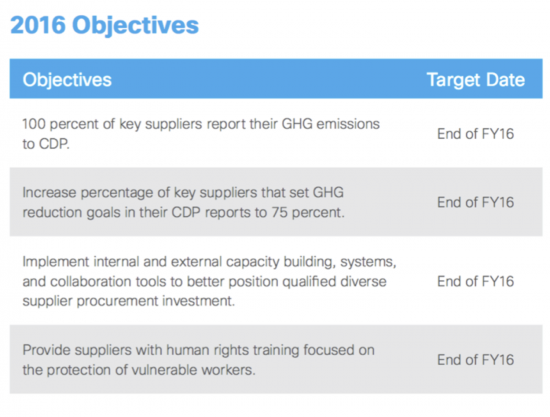 We feel that sustainability is a bigger priority than ever before. As our CEO Chuck Robbins put it:
We feel that sustainability is a bigger priority than ever before. As our CEO Chuck Robbins put it: