Cloud computing has reached a tipping point as many organizations have either adopted, or are planning to adopt, some form of cloud computing technology – whether IT knows and manages it or not. “Speed to capability” is one of the primary reasons that individuals, business units and departments are using cloud technology and service providers with increasing frequency. Yet, despite the rapidly increasing use of cloud services, many IT executives remain hesitant to endorse a “cloud-first” approach.
What’s worse is that there are some organizations that are not convinced they should adopt cloud-based services, citing security and privacy concerns, operational challenges or inability to control information. Unfortunately, the reluctance to migrate to the cloud can increase an organization’s risk rather than mitigating it.
Cloud Consumption – A World of Many Clouds
However, in the 2014 KPMG Cloud Security Report, more than 80 technology industry leaders ranked cloud as the technology that will have the greatest impact in driving business transformation for enterprises.
McKinsey & Company’s report, Disruptive Technologies: Advances that will transform life, business, and the global economy, projects that the total economic impact of cloud technology could be $1.7 trillion to $6.2 trillion annually in 2025. Of this total, $1.2 trillion to $5.5 trillion could be in the form of surplus from use of cloud-enabled Internet services, while $500 billion to $700 billion could come through productivity improvements for enterprise IT.
Over the past five years Cisco’s growth in cloud adoption has been at a rate of 30% year over year. Currently about 500 reviewed/approved cloud providers are in use at Cisco. Approximately 50% of all cloud providers we assess consume Cisco’s highly confidential or restricted data, which is the highest classification at Cisco.

The world of many clouds is here to stay: private, public, hybrid infrastructure or Platform-as-a-Service and Software-as-a-Service applications. Over the last decade, Cisco has enabled all forms of clouds through our leading DC and network products and our partners. We are now focused on providing you with workload portability solutions that make it easier for you to manage and migrate workloads seamlessly in the world of many clouds. Our focus is to make it easier for IT to become a broker for all cloud services based on your business imperatives.
Building Secure Cloud Services
Ultimately, the customer must ensure that the cloud security vendor can offer a cloud security lifecycle that protects data at every part of the process. When data and brand are in the hands of a third-party cloud service provider, we want to make sure there are adequate controls to ensure security and fiscal responsibility.
Cisco IT has established a global governance process to oversee policy and processes for risk assessment and remediation and coordinate the framework for IT service owners and business partners to work closely together in the selection of cloud service providers. This process, called Cloud/Application Service Provider Remediation (CASPR), is how Cisco ensures cloud service providers are properly assessed, and the appropriate visibility is available to critical stakeholders around Cloud Service Provider usage.
As part of the CASPR process, IT teams (via IT service owners) partner with business stakeholders to find approved cloud service capabilities whenever they are required. The Cisco InfoSec is a strategic partner in helping to protect Cisco’s information and brand by setting data security standards, conducting security risk assessments and establishing remediation plans when necessary. It is a co-dependent relationship between IT, InfoSec, procurement and the business to ensure relevant oversight of our CSP suppliers.
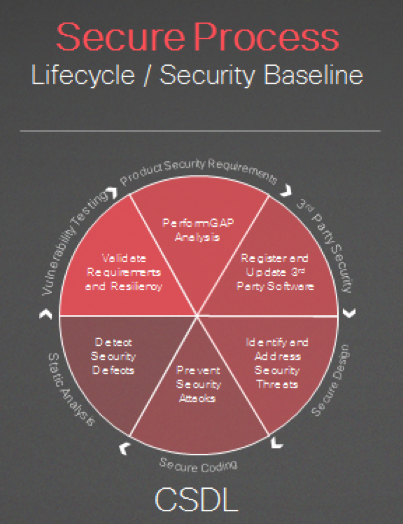
The Cisco Secure Development Lifecycle
The cloud security market continues to grow at a 14 percent CAGR, according to industry analysts, as security is a top concern with regard to hosting the cloud. It has become vast and complex and it must have a seamless ecosystem. Security automation and transparency are key to building & operating clouds securely. The Cloud requires security to be built-in and continuous throughout the lifecycle. Let’s take a closer look at what that means.
Before adopting any cloud offering, ask two important questions.
- Given the sensitivity of the data I’m putting into the cloud, does the cloud operator have the proper controls – and do I have the right visibility – to adequately protect my data?
- Will I be able to respond to incidents when they happen?
Cisco’s Secure Development Lifecycle process sets a high bar for security expectations that customers can place on Cisco-based cloud offerings. The lifecycle ensures that not only are the offerings built to high standards, but they also ensure consistency, resilience and data protection through security operations and monitoring. We follow a three-pronged approach:
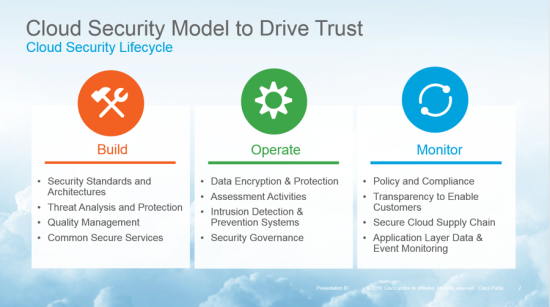
- Build Secure Cloud: We use the Secure Development Lifecycle to ensure standards and quality expectations are clearly defined across all cloud offerings. We use Cisco’s security baseline and common security modules and services to help enable DevOps teams to build and operate secure offerings in the Cloud. The security baseline standards take input from Cisco’s mature internal security development standards as well as established security best practices, such as CSA, FedRAMP, etc.
- Operate Secure Cloud: To run secure cloud offerings, we use an ongoing security operations and governance model which consists of 24X7 vulnerability scans, network and application layer protections, aggressive penetration/attack testing and driving accountability to stated goals and SLAs.
- Monitor Secure Cloud: We monitor our cloud offerings by using Cisco’s monitoring and incident response process and telemetry from the industry. Our offerings, processes and sites are audited by third parties to ensure we are accountable to the expectations we set for ourselves and our customers. For example, our WebEx offerings are ISO 27001 and SSAE-16 SOC/2 certified.
A Reputation Built on Trust
As the Cloud continues to drive disruption in the business world across the globe, organizations are increasingly placing their trust in third-party cloud service providers (CSPs). A holistic approach to building security into the cloud enables trust throughout the lifecycle. At Cisco, we believe that transparency also leads to trust. Transparency to our customers includes rapid and open communications and is critical in earning and maintaining a trusted relationship. By offering a level of threat research and intelligence beyond that available from most companies, Cisco provides an unmatched security ecosystem. It’s another example of how we remain firmly committed to maintaining leadership in cloud security.





