Written By Christian Schmutzer, Principal Engineer at Cisco
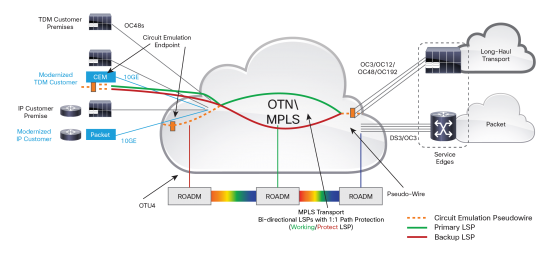
The idea behind Cisco’s Transport Network Modernization solution is simple: allow a single, packet-oriented network to support both connectionless and connection-oriented services concurrently. A number of technology innovations were required to make the solution work, including a bi-directional, co-routed MPLS-TE Control Plane (NCS 4200); DWDM integration and unlimited bandwidth (NCS 4000 and NCS 2000); high-density Circuit Emulation (NCS 4200); and fully programmable management with EPN Manager (EPN-M). Together, these technology innovations enable service providers to migrate at their own pace from TDM and SONET/SDH to packet services and replace aging DCS and ADM hardware while still maintaining legacy TDM services.
Let’s take a closer look at how the Cisco’s Transport Network Modernization works, with a deep dive into the technology innovations that underpin the solution.
A Bi-directional, Co-routed MPLS-TE Control Plane
The NCS 4200 platform uses FlexLSP to provide bi-directional tunnels, 50ms protection and OAM for protection and network monitoring. Packet-based QoS and call admission control is used to guarantee the service bandwidth and latency, and at the same time allows the Service Provider to benefit from the synergies of running classical data services on the same network. Additional attributes supported include non-revertive switching and persistent LSP paths.
Path protection, a requirement for connection-oriented services, creates a challenge – even if mechanisms like BFD (offloaded into HW) allow for quick failure detection within <10msec for each path, there are times when a lot of paths need to be switched. In TDM systems, this is done by an optimized low-level uCode on the line cards, or in a fabric card directly – but in a packet system, this is not possible.
Wrap protection technology addresses the challenge by moving the function to the nodes local to the failure when a single fault is detected, triggering a single message inside the system which then switches any number of paths to their pre-programmed protect entity. Traffic is then sent back on the working path in the reverse direction to the Head/Tail node, where it gets redirected to the protect end-to-end path.
This immediate reaction ensures <50msec traffic restoration for any number of LSPs and also ensures that traffic flows along the configured working or protect path across the network. Once the Head/Tail nodes detect the failure, traffic will be directly sent to the protect entity and the “traffic wrap” will get removed.
DWDM Integration and Unlimited Bandwidth
The NCS 4000 platform provides unprecedented DWDM integration (same capacity whether it is DWDM or grey optics). A single 400G packet/OTN/DWDM card tightly integrates the packet processor and fabric interface ASIC, OTN processing and encryption ASIC, 400G coherent DSP chip, pluggable 100G QSFP-28 modules, 40G QSFP+ modules and 10G with breakout support – and finally, a pluggable analog coherent optics module supporting 200G. In the past, incorporating all this functionality required three dedicated cards.
This hardware innovation results in significant savings (66% space, 50% power, and 65% cost) and enables customers to simplify their spares strategy by deploying a single card versus three dedicated cards and slots for those cards. Unlimited bandwidth scale is provided, supporting by NCS 4000 Multi-Chassis configurations which are avoiding costly inter-chassis links. And inter-office connectivity is delivered in a very flexible, highly scalable way using the NCS 2000 photonics platform, which provides Flex Spectrum DWDM capability.
High-Density Circuit Emulation (CEM) Technology
With circuit emulation, TDM services can be migrated across an asynchronous IP/Multiprotocol Label Switching (MPLS) network with no compromise on errors or delay. CEM provides the ability to terminate TDM traffic over SONET/SDH as an interface, continuing fault propagation between SONET/SDH and the IP/MPLS network using pseudowires running over dynamic label-switched paths (LSPs). LSPs are paths through MPLS networks are set up by a signaling protocol. The CEM solution is supported by multiple industry standards for both SONET/SDH and IP/MPLS.
CEM uses different methods based on TDM service type to transport the different types of TDM traffic over the packet network:
- Structured agnostic TDM over packet (SAToP) uses a pseudowire to transport T1, E1, T3, and E3 circuits.
- Circuit emulation service over a packet-switched network (CESoP) uses a pseudowire to transport structured (NxDS0) TDM signals.
- Circuit emulation over packet (CEP) uses a pseudowire to transport SONET/SDH containers (including path overhead).
All TDM functions and packetization (SAToP, CEP, CESoP) are integrated into a single FPGA, improving the overall density by an order of magnitude. In the past, a router slot could deliver 4xOC3 CEM ports, which meant a platform such as the Cisco 7600 router could provide 36xOC3 ports (~5Gbps) of TDM/CEM capacity while requiring a 21RU rack space. With the NCS 4200 platform 10G or 5G worth of SONET capacity per interface module is provided, which equals 70Gbps of SONET interface capacity in a 14RU platform. A scale that is unmatched in the industry.
The solution also supports low-density use cases, using the identical technology and feature sets, allowing both SONET and PDH interfaces to be combined into a small 3Gbps CEM interface module supported in a 3RU chassis or 1RU pizza box platform.
SONET / SDH / Card Protection Technology Adoption for Packet Platforms
Traditionally, UPSR/APS/Card protection technology is implemented using a centralized TDM
backplane/fabric. Since the NCS 4200 platform does not have a centralized TDM Fabric, software and hardware were designed to replicate these functions including:
- Circuit Emulation, VCAT and multi-service traffic to protection circuits, to meet the transport standards.
- Alarm processing in an optimized manner so that APS and UPSR Protection could be achieved in the <50ms time interval in the packet product.
Mechanical and Thermal Challenges providing high-density CEM
The high-density CEM configurations create some unique challenges in cooling the system and in routing the vast quantity of cables, and ensuring ease of maintenance. A special cable management bar allows a failed card to be replaced without affecting cables connected to the adjacent card.
The same level of focus was needed for low-density use cases as well. For example, a minimal touch bracket for the 3RU NCS 4200 provides cable routing options in an entry level/low-density system, enabling the cabling of this small platform to comply with the carrier’s central office standards while maintaining a minimal platform footprint.
EPN Manager (EPN-M): A Fully Programmable Solution
EPN Manager helps service providers to modernize circuit transport and private line networks by addressing the combination of CEM over packet, OTN, and DWDM/ROADM networks with comprehensive end-to-end network management support. This all-in-one, next-generation product provides device management, network provisioning, and network assurance across converged packet-optical networks.
With EPN Manager’s integrated lifecycle management and standards-based northbound interfaces, you can easily integrate with your existing OSS/BSS applications. Cisco EPN Manager provides the required comprehensive TDM and IP service lifecycle management, including fault, configuration, performance monitoring, and provisioning. Cisco EPN Manager is also easy to use, incorporating simplified workflows and operations-based tasks that align with existing user roles, so no new hires or skillsets are required.
A Roadmap for Transport Network Modernization
In our E-Book, A Roadmap for Transport Network Modernization, we explain to you how our next-generation approach provides a cost-effective network modernization path, while still supporting ongoing TDM services requirements.
If you are ready to modernize your network, Download a copy of our E-Book today.


 Here are the top nine proof points that demonstrate how the Catalyst 9000 delivers:
Here are the top nine proof points that demonstrate how the Catalyst 9000 delivers: