For more than two decades, malicious actors have been evolving their Phishing techniques to effectively achieve their goals. From poorly crafted scams to extremely well crafted documents, Phishing attacks keep being a very effective technique in the attackers toolbox. Anyone can be a target. While more sophisticated phishing attacks are constantly changing, some other type of attacks remain under the radar for long periods of time.
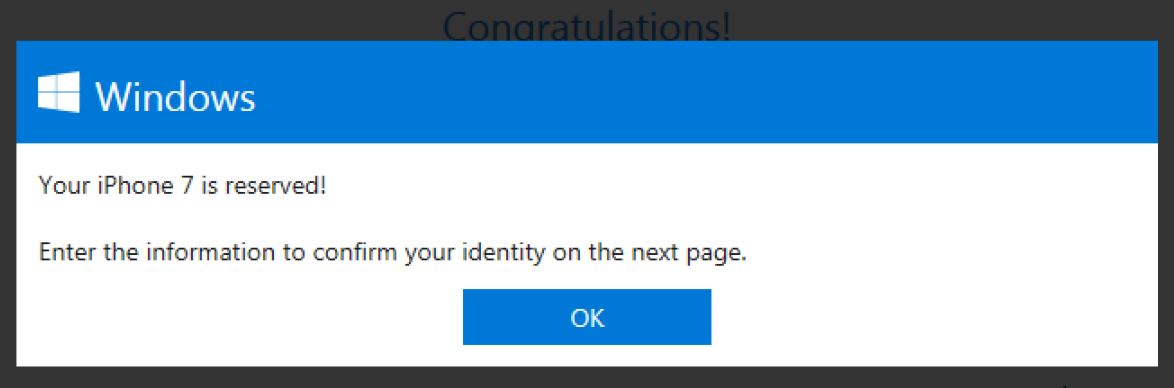
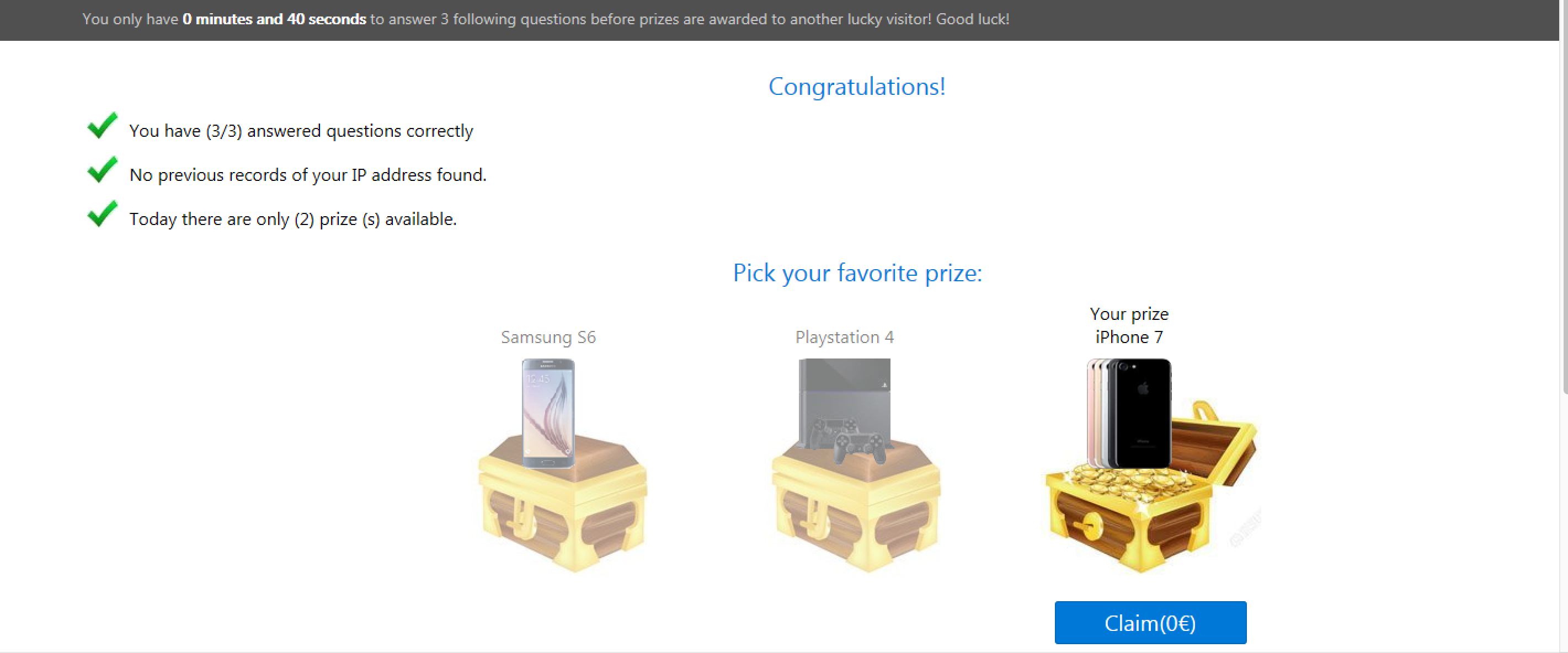
Figure 1: Lucky Winner phishing campaign impersonates top companies to lure users to provide personal information.
In the last three months, Cisco Cognitive Threat Analytics observed a sudden increase in the number of users accessing a specific type of phishing campaign that we refer simply as “Lucky Winner”. This campaign lure users to answer some questions in order to win some special prize, typically the latest model of an iPhone or Samsung phone. For more than two years the Lucky Winner campaign has been impersonating top companies such as Google, Facebook, Microsoft and Apple in order to steal personal information or infect users with unwanted applications or malware. In this blog post we will cover how the ‘Lucky Winner’ campaign works and how to stay safe from this type of threat.
Congratulations, You Are A Lucky Winner!
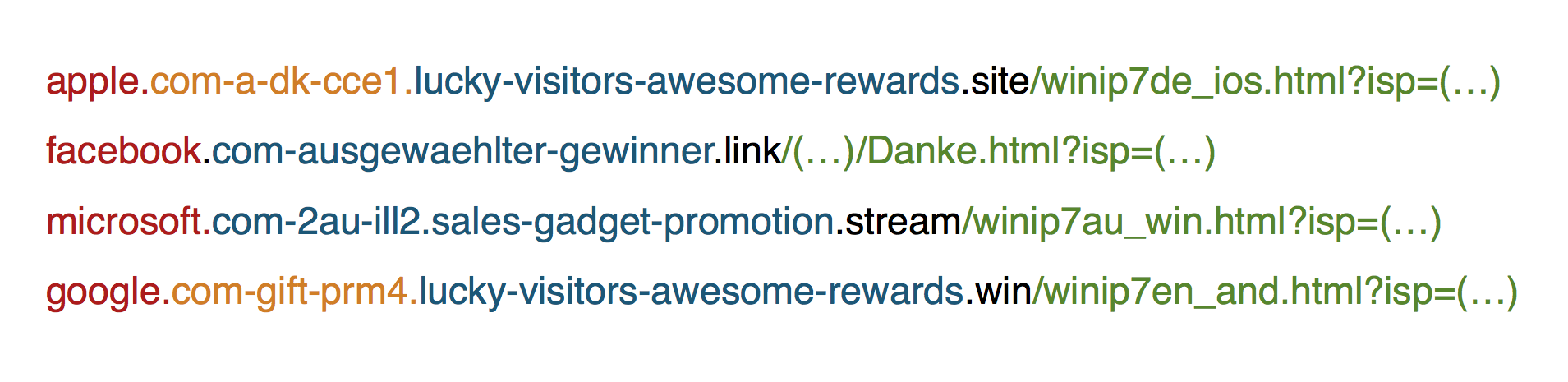
The Lucky Winner campaign uses well crafted domains (See Figure 2) that impersonate well known dot com companies and relies on the fact that nowadays mobile browser address bars are really small and users won’t actually see the full URL that is being accessed, only the first part which is usually attempt to look a legitimate site (See Figure 3). This campaign relies on users seeing what they want to see, and not paying attention to what type of websites are they really accessing.
Figure 2: Examples of phishing URLs that try to impersonate big companies: Apple, Facebook, Microsoft, and Google.
Figure 3: Lucky Winner relies on the small size of the browser address bars to deceive the users and abuse their trust in the targeted company.
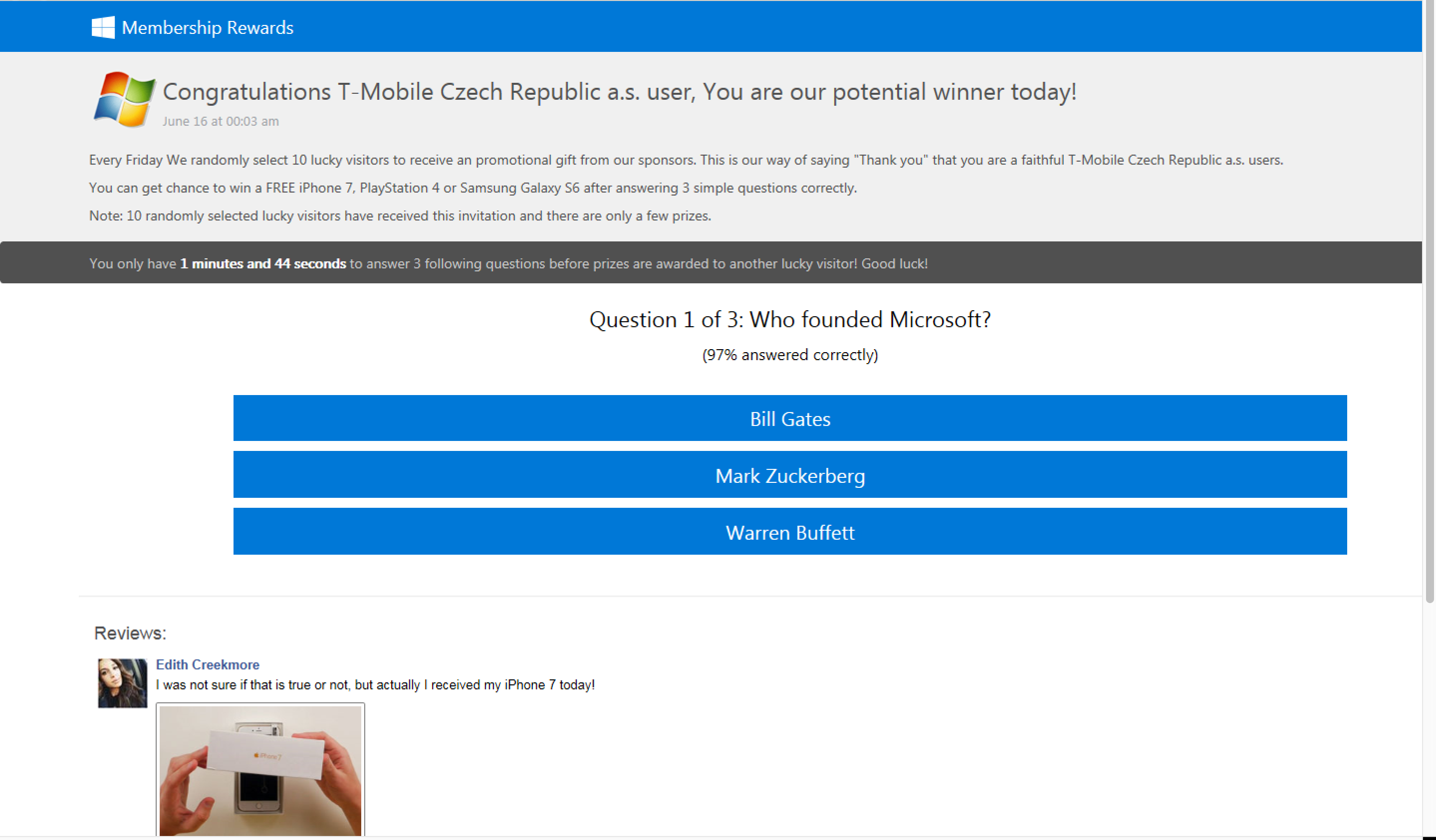
Once the user access the URL, a notification of winning a prize will pop up offering the user to participate in a small quiz for a chance to win a valuable gadget. The questions are very easy and the answers mostly obvious. The questions will change depending on the company they are trying to impersonate, for example (See Figure 4): “Who founded Facebook” (Mark Zuckerberg, Warren Buffet or Bill Gates), or “Who founded Apple” (Mark Zuckerberg, Bill Gates or Steve Jobs). Don’t worry, if you don’t know the answer you still win! As we found out during our research after deliberately choosing the wrong answers.
Figure 4: Lucky Winner campaign poses simple questions for users offered to answer to get a chance to win a prize.
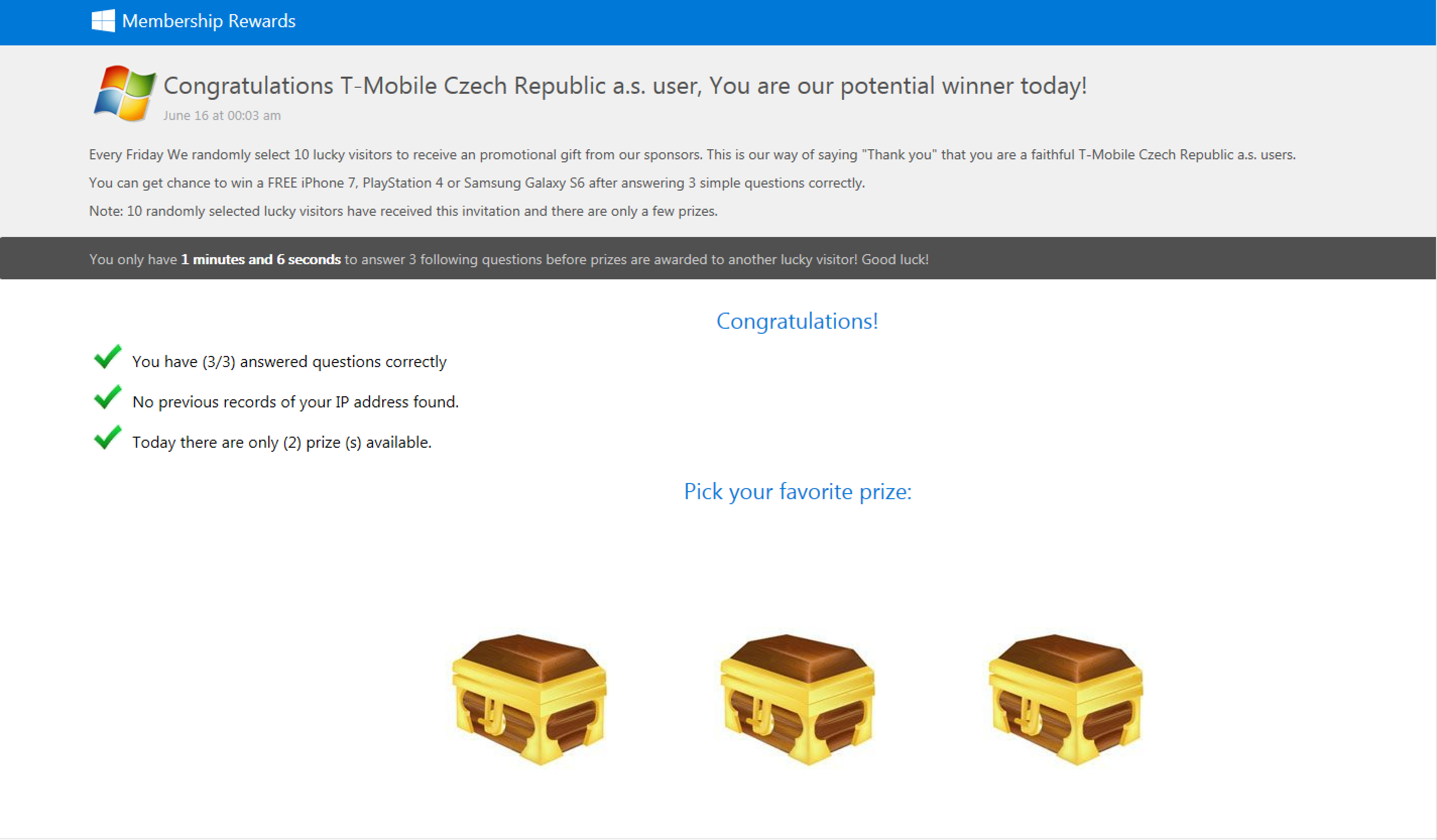
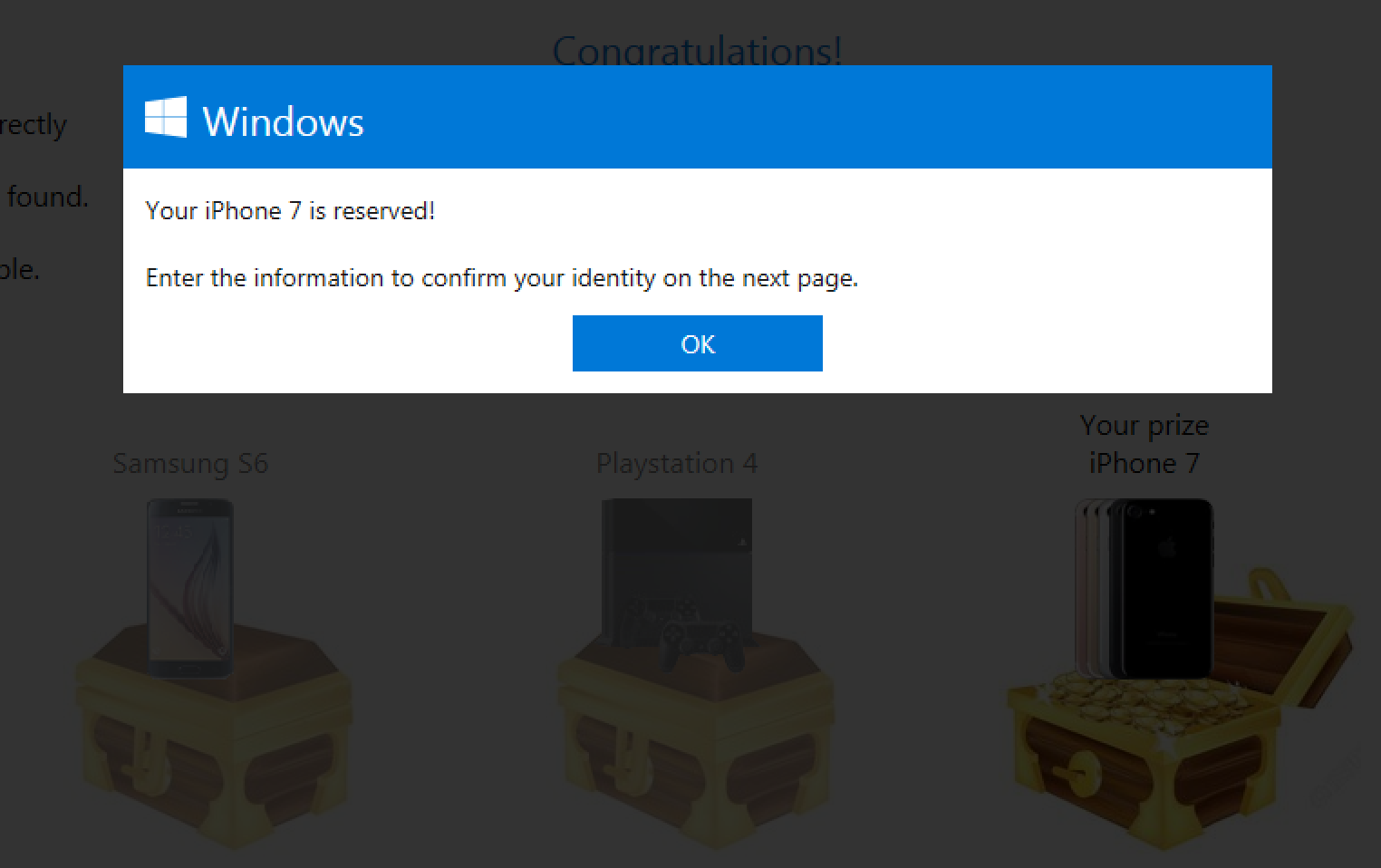
Once the user answer the three questions, three chests will appear containing “The Prize” from which the user should pick. Most of the time, the ‘hidden’ prize is the latest model of an iPhone or Samsung mobile phone, but other valuable electronic devices were offered as well (See Figure 5). Once the user pick its favorite chest, a dialog window pops up asking the user to claim the prize and to read the terms and conditions.
Figure 5: After answering all questions, the user is offered to choose a chest with a prize. In this case it is an iPhone 7.
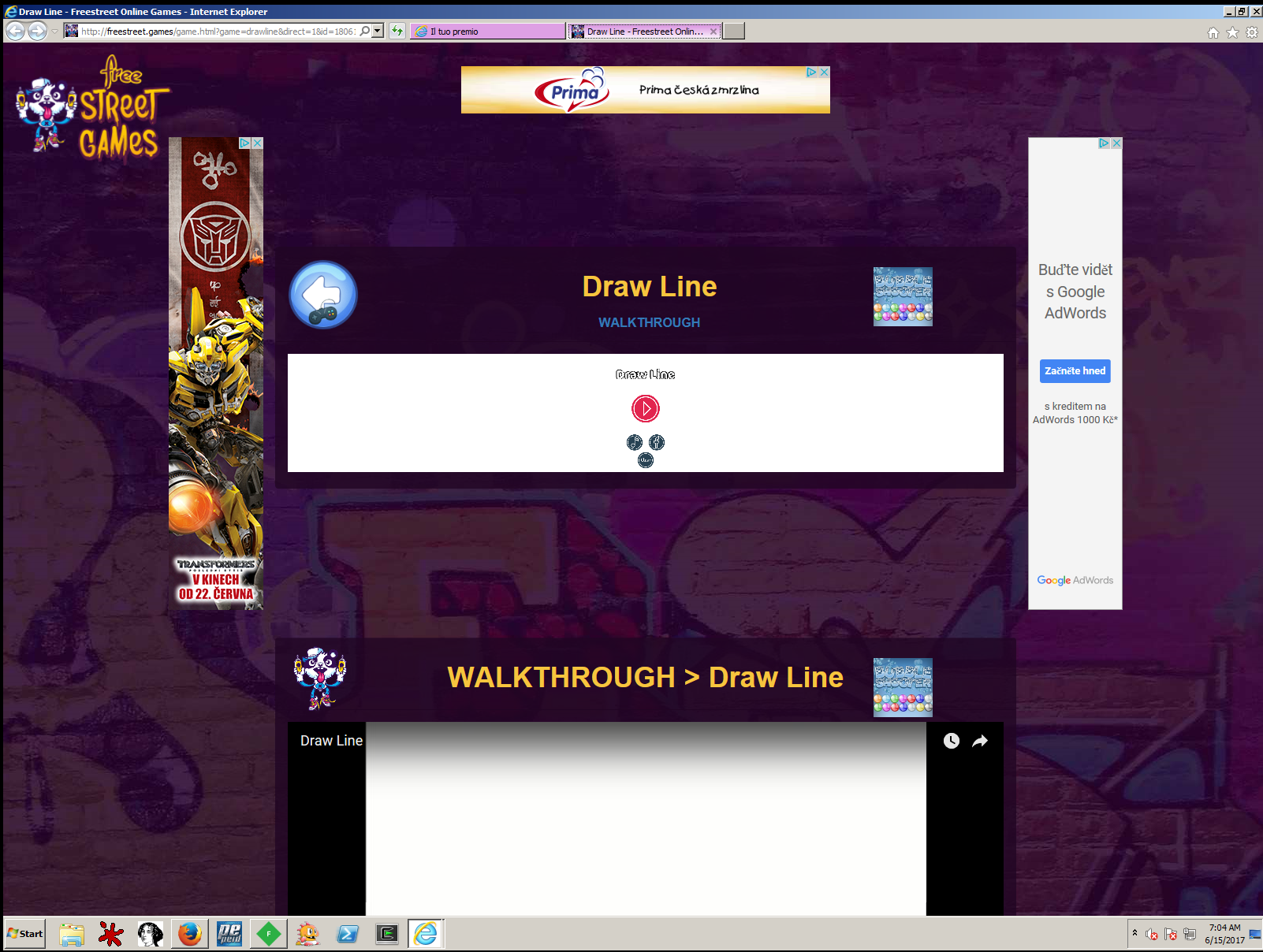
When the user clicks on the button to “Claim” the prize, it will be redirected to different web pages depending on the location or the type of user. The final destination may be a website full of advertisements, online gaming sites serving potential malvertising or to a different phishing scam such as the well-known Spinning Wheel scam [1] (See Figure 6).
Figure 6: A dialogue window to claim a prize will be shown to the victims after choosing their prize. After that stage, the user can be redirected to different locations, in this case an online gaming site full of advertising.
As already investigated by researchers from Malwarebytes [1], the Spinning Wheel campaign offers users to spin ‘a lucky wheel’ and ‘win’ an electronic gadget. Needless to say, there were no prizes but a lot of pop up windows, false promises, redirections to websites with questionable content, and even fake flash player update offers.
On Top Of Everything, Your Information Is Collected
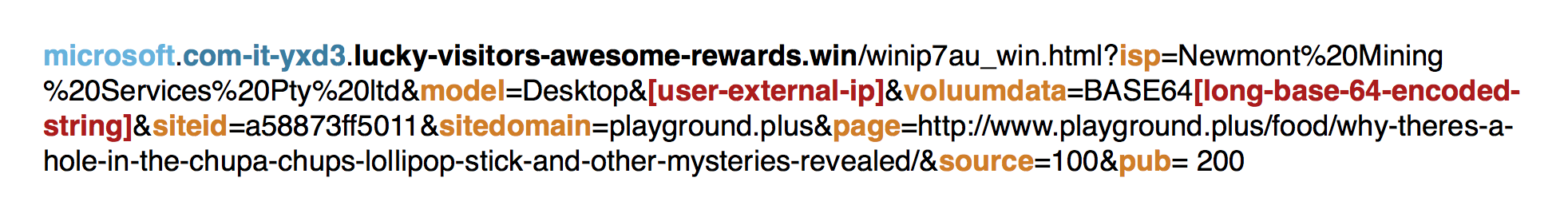
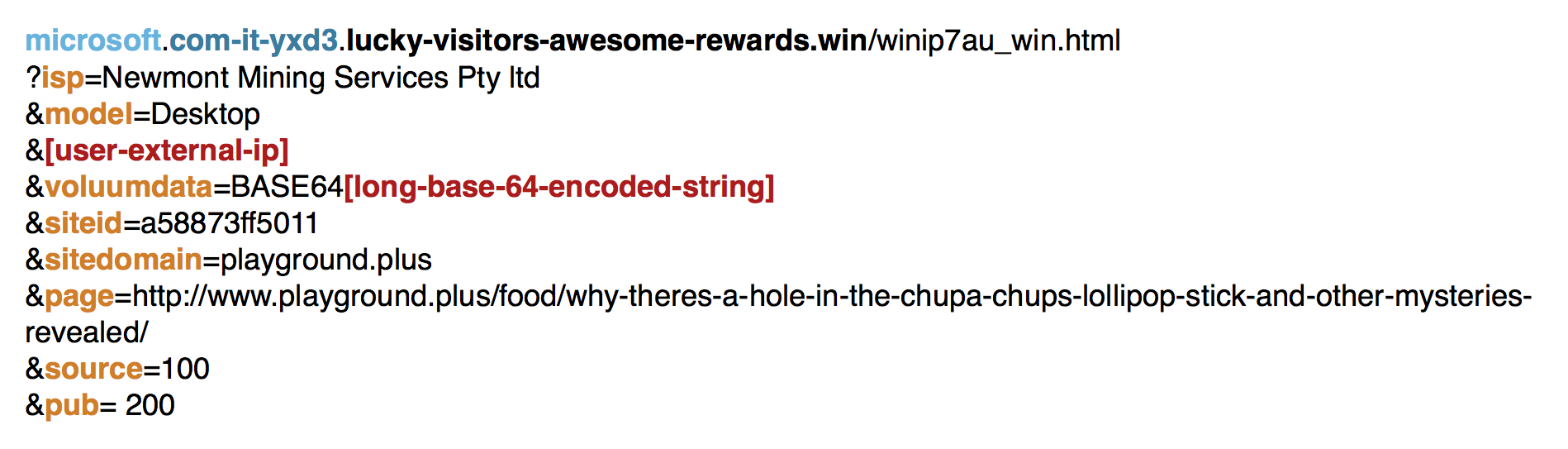
Once the user accesses these malicious websites, some interesting information is collected. Figure 7 shows an example of an URL associated to this campaign. The decoded example of the same URL, as shown in Figure 8, shows the information scammers are trying to collect: user’s ISP ( Internet Service Provider), platform (desktop or mobile), IP address, referer domain, referer page or URL, and referer page’s ID.
Figure 7: Lucky Winner encoded phishing URL.
Figure 8: Lucky Winner decoded phishing URL.
We observed the Lucky Winner campaign since early 2015, however, it might be around even longer. The URL patterns have barely changed since we first spot it. The only major change was the Base64 encoding of the ‘voluumdata’ parameter information. Our records show that the encoding was added around April 2016. The hostnames are using several levels of subdomains in order to trick the users and make them believe that they are accessing a legitimate website. Mobile users are at an even higher risk since mobile screens have a limited capability to display the whole content of the URL. Lucky Winner campaign is targeting all known platforms, including iOS, Android, Windows and probably (but not yet confirmed) Mac OS and Linux users. We observed Lucky Winner campaigns in the following most common languages: English, Dutch, German and Italian.
The Most Common Words That You Should Avoid Clicking On
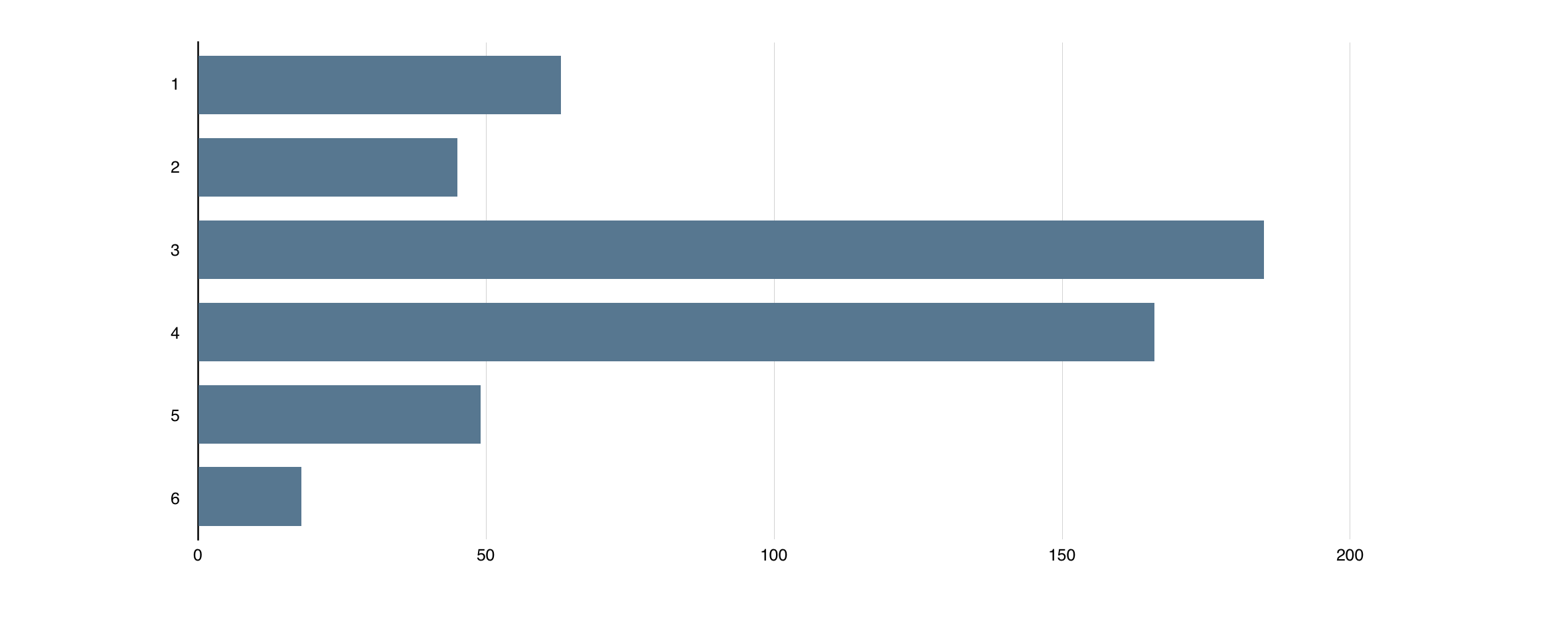
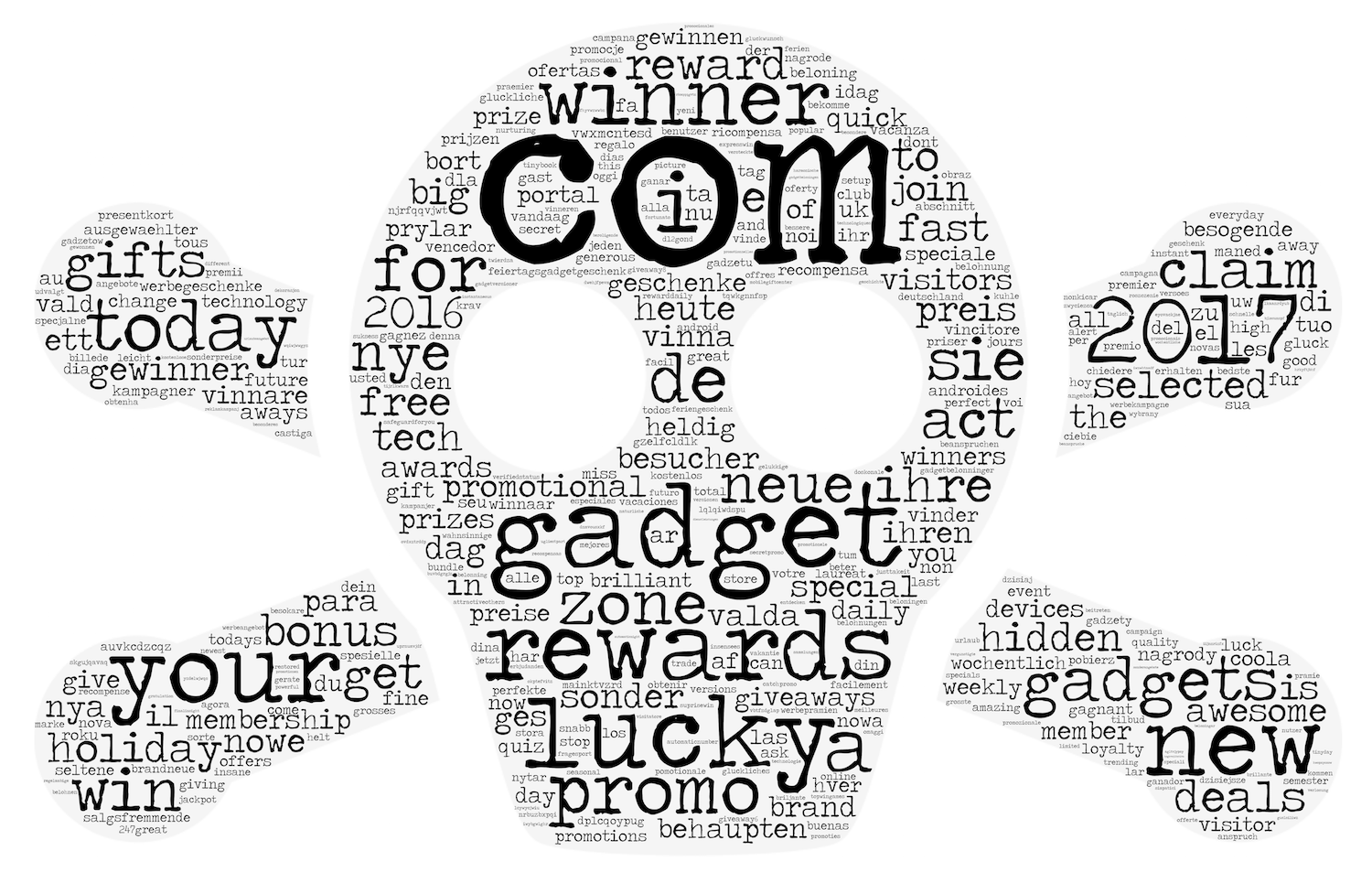
We performed a quick analysis of the typical words used to craft the Second Level Domains (SLD) used by Lucky Winner campaign. As observed in Figure 9, the typical SLD is composed by a combination of three to four words separated by figure dash (‘-’). A frequency analysis of these words shows that the most common word is ‘com’, which is due the fact that this campaign tries to impersonate very popular dot com domains such as facebook.com, google.com, apple.com and microsoft.com (See Figure 10).
Figure 9: Lucky Winner Second Level Domains are composed by a combination of words separated by a figure dash; typically three or four words are used.
Our analysis of the most frequent words used shows that users should be wary every time they access websites that include a combination of the words ‘com’, ‘gadget’, ‘reward’, ‘lucky’, ‘winner’, ‘promo’ and ‘gift’, or variations of them. Any combination of these words may lead to users to high risk websites and end in further infections or loss of information.
Figure 10: Typical words used by the Lucky Winner campaign as Second Level Domains.
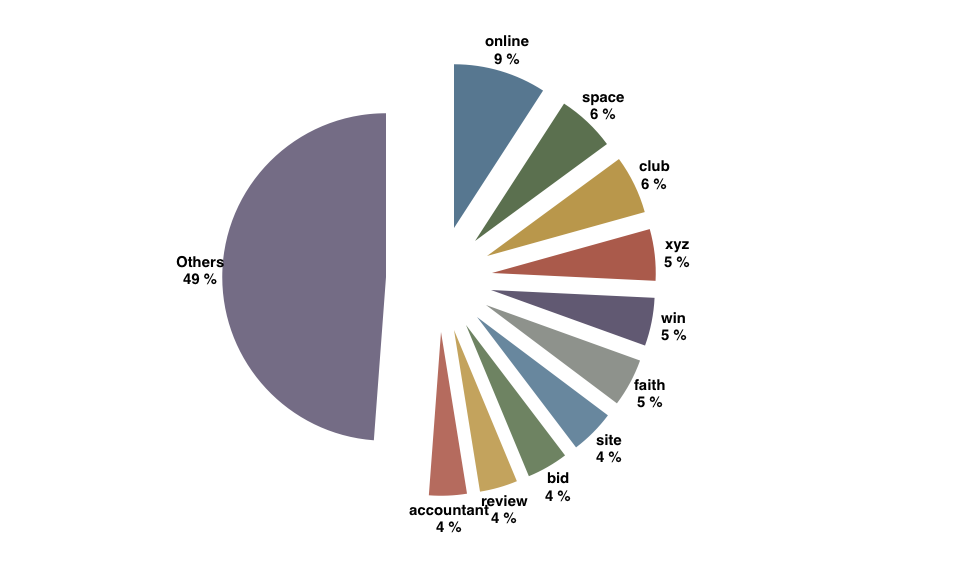
Additionally, we analyzed the most common Top Level Domains (TLD) used in the Lucky Winner campaign. Our analysis shows that 50% of the domains used by this campaign in the last two years were registered with the TLDs: .online, .space, .club, .xyz, .win, .faith, .site, .bid, .review and .accountant (See Figure 11).
Figure 11: Most common Top Level Domains used by the Lucky Winner campaign.
How To Stay Safe
As users, we need to accept the fact there are some individuals and groups trying to trick us to their own profit. After receiving a link or an attachment via email or SMS we need to stop and think for a moment, and ask your self “Why?” Well known companies rarely send their customers shady offers to win an unknown prize, they usually announce giveaways or other contests in advance via official communication channels. In order to be sure you are not being tricked, is always better to double check before clicking any link.
User education and awareness is a very important step in phishing prevention. However, there will always be people who for various reasons will still access those shady websites. Network monitoring tools help to fill the gap and detect successful phishing accesses. Cognitive Threat Analytics (CTA) discovers hundreds of phishing domains every week. Cisco CTA models the behavior of the network and through a refined process and pipeline of Machine Learning algorithms is able to discover previously unseen phishing domains and raise incidents facilitating the incident response.
Cisco CTA is integrated with AMP for Endpoints and StealthWatch!
References
[1] https://blog.malwarebytes.com/cybercrime/2015/07/dont-take-this-lucky-wheel-for-a-spin/
Where to go next
To request a free evaluation that will uncover adware, as well as command and control communications lurking in your environment visit: https://cognitive.cisco.com/
Read more about CTA threat detection in action:
- In plain sight: Credential and data stealing adware
- The light is green! But is it safe to go? Abusing users’ faith in HTTPS
Watch more about CTA as part of Cisco Security solutions:
- Encrypted Traffic Analytics with StealthWatch, ThreatGrid and Cognitive Analytics
- Cisco AMP for Endpoints Integration with Cognitive Threat Analytics Overview – YouTube
The full list of IOCs is available here.







Excellent example of a 101 crash course , in phishing techniques’ anatomy. Thank you for sharing your post’s insights.