Late last year, I compared Cisco’s S3260 Storage Server to Amazon’s S3 service. The results shocked a lot of people and spurred a lot comments on the blog.
On Friday, April 14, the actor group identifying itself as the Shadow Brokers released new information containing exploits for vulnerabilities that affect various versions of Microsoft Windows as well as applications such as Lotus Domino. Additionally, the release included previously unknown tools, including an exploitation framework identified as “FUZZBUNCH.” Preliminary analysis of the information suggested several of the released exploits were targeting zero-day vulnerabilities. Microsoft has released a statement regarding the newly released exploits targeting Windows and notes that most of them have been previously patched. Talos is aware of this new information disclosure and has responded to ensure our customers are protected from these threats.
Coverage for the exploits and tools disclosed by the Shadow Brokers is available through Cisco’s security products, services, and open source technologies. In some cases, coverage for specific tools or vulnerabilities was already available prior to today’s information release. In the cases of the exploits dubbed ETERNALCHAMPION and ETERNALBLUE, Talos had pre-existing coverage that detects attempts to exploit these vulnerabilities.
As more and more businesses make the shift to digital, questions of cybersecurity continue to arise. This is especially true in industries that have a lot at stake — industries like financial services. As digital transformation rapidly takes hold, how can financial services companies keep up? What can they do to continue supporting customers with the cloud-based and mobile solutions they demand while maintaining airtight security? Where is the industry today and what do financial services organizations need to do now to stay competitive in the future?
Join us on April 18th at 10 am PT (1 pm ET) to discuss these questions and more in our upcoming #CiscoChat: Is your financial institution secure? During the chat, we’ll be joined by a host of Cisco experts and analysts dive into the importance of a secure network foundation for the financial services industry.
To participate in the chat:
- Make sure you’re logged into your Twitter account.
- Search for the #CiscoChat hashtag and click on the Live tab.
- The chat will be moderated by D’Auria Henry on the Cisco Financial Services Industry channel (@CiscoFSI) on Twitter. Be sure to follow the account to participate. They will begin welcoming guests at 10 am PT (1 pm ET) and posting questions for discussion.
- For @ replies to specific participants in the discussion, please use a “.” at the beginning of the tweet, so that your question or comment will appear in your public twitter feed.
- If you need multiple tweets to answer a question, please preface each tweet with “1A, 2A,” etc. in order to make it easier for others to follow along with the conversation.
- Be sure to use the #CiscoChat hashtag at the end of each tweet, so that others can find your contributions to the discussion.
Don’t forget to bring your own questions to the discussion as well! See you there!
Today, Talos is publishing a glimpse into the most prevalent threats we’ve observed between April 7 and April 14. As with previous round-ups, this post isn’t meant to be an in-depth analysis. Instead, this post will summarize the threats we’ve observed by highlighting key behavior characteristics, indicators of compromise, and how our customers are automatically protected from these threats.
As a reminder, the information provided for the following threats in this post is non-exhaustive and current as of date of publication. Detection and coverage for the following threats is subject to updates pending additional threat or vulnerability analysis. For the most current information, please refer to your FireSIGHT Management Center, Snort.org, or ClamAV.net.
Over the past week, information regarding a serious zero-day vulnerability (CVE-2017-0199) in Microsoft Office was publically disclosed. Since learning of this flaw, Talos has been actively investigating the issue. Preliminary reports indicated that this vulnerability was actively being exploited in the wild and used to compromise hosts with Dridex, a well-known banking trojan.
On Tuesday, April 11, Microsoft released a patch for CVE-2017-0199. CVE-2017-0199 is an arbitrary code execution vulnerability in Microsoft Office which manifests due to improper handling of Rich Text Format (RTF) files. Exploitation of this flaw has been observed in email-based attacks where adversaries bait users to open a specifically crafted document attached to the message. Given that this vulnerability continues to be actively being exploited, Talos strongly recommends all customers patch as soon as possible.
Read more »
Global analyst firm IDC recently named Cisco AMP for Endpoints a leader amongst endpoint security solutions in their report, “IDC Marketscape: Worldwide Endpoint Specialized Threat Analysis and Protection 2017 Vendor Assessment” (April 2017, IDC #US42385717). The IDC study examines market-leading endpoint security solutions from 11 different vendors, based on a variety of different parameters, including solution capabilities, features, business strategies, buyer perception, and more.
In naming Cisco AMP for Endpoints a leader, the IDC Marketscape cited the following:
- “Cisco Systems is a Leader in this IDC MarketScape for endpoint STAP for its tight integration with Cisco’s Advanced Malware Protection portfolio to provide comprehensive protection against targeted attacks.“
- “Cisco has created one of the most robust comprehensive management consoles to support organizations with the wherewithal to support dedicated incident responders and active threat hunters.”
- “It provides investigators with rich, contextual information and the ability to conduct ‘retrospection,’ a search through historical data to correlate previous activity that may be related to a newly detected threat.”
- “Cisco provides one of the most comprehensive and, more importantly, cohesive set of offerings to identify and block attacker activity and advanced malware across endpoint, web, messaging, and network-level avenues of attack… the solution should significantly improve a large enterprise’s security posture.”
- “Customers interviewed by IDC praised the endpoint security offering for its ease of deployment and ties to Cisco’s network security appliances.”
- “Users of the endpoint security solution gave its management console high marks.”
The IDC Marketscape also gave AMP for Endpoints high marks for its capabilities in attack prevention, detection, and response. The report specifically highlights AMP’s ability to detect and contain malicious threats before, during, and after an attack; increase endpoint visibility to see the full scope of an attack from beginning to end; enable rapid incident response; identify memory-only (or file-less) malware; provide automatic remediation based on cloud convictions; detect attacker tactics like manipulation of Windows PowerShell or privilege escalation; and built-in sandboxing capabilities to reverse analyze unknown files. The report also touts AMP for Endpoints’ broad coverage across platforms—including Mac, Windows, Linux, and Android—and the flexibility for customers to deploy the solution via the cloud or on-premises.
In the midst of an ever-evolving, increasingly sophisticated threat landscape, the Cisco Security Team will continue to innovate. We are committed to providing simple, open, and automated security solutions to help organizations protect their sensitive data, customers, employees, and brands. Cisco AMP for Endpoints embodies these principles, providing next-generation endpoint security capabilities to help our customers see more, protect better, and respond faster.
To learn more about why IDC namedCisco AMP for Endpoints a leader in the endpoint security space, download the report here. For more about AMP for Endpoints, visit cisco.com/go/ampendpoint.
I am pleased to share some exciting news! Cable industry leader George Kajos is joining our Cable Access Business Unit and my leadership team as Senior Director of Software Engineering.
 George comes to Cisco with over 20 years of experience leading state of the art Video, Conferencing, and Networking product development teams. He has managed development and quality assurance teams for a variety of companies ranging from VC funded startups to large multi-national public companies. Most recently, George was Senior VP of Engineering at SeaChange International. He managed the product life cycle for Back Office, Content Management, VOD Clients, and Advertising products. He coordinated multi-site, offshore, and outsourced Agile development teams.
George comes to Cisco with over 20 years of experience leading state of the art Video, Conferencing, and Networking product development teams. He has managed development and quality assurance teams for a variety of companies ranging from VC funded startups to large multi-national public companies. Most recently, George was Senior VP of Engineering at SeaChange International. He managed the product life cycle for Back Office, Content Management, VOD Clients, and Advertising products. He coordinated multi-site, offshore, and outsourced Agile development teams.
His standards activities include serving as editor of the H.341 standard for the ITU-T and participation in the ITU-T H.323, ANSI FDDI, and IETF working groups. He has presented at industry trade shows such as NTCA, SCTE, Telecom Next, Telecon and BCR Multimedia.
We are really excited to have George join us on our journey to usher in the next generation of cable access networking. We look forward to George’s leadership in transforming our business by harnessing the power of cloud-native infrastructure, automation and telemetry.
Please join me in welcoming George to Cisco!
Cybersecurity was a main topic at the recent IP Visions Conference and Expo in St. Louis, MO this week. Cisco hosted a pre-conference workshop on Monday and cybersecurity was referenced in all the topics; three out of the five session’s main discussion points focused around cybersecurity. CCI was honored to have been selected by Cisco as one of their partners to present security during a pre-conference session.
Following the Monday afternoon workshop in the “Show Me State”, many event attendees stopped in the CCI Systems booth for hands-on “Show Me Security” demos. There visitors could witness first-hand how Cisco security products tie together to build a complete security solution supported by CCI Systems and Cisco. Products such as Umbrella “OpenDNS”, NGFW Firepower, Identity Services Engine (ISE), and Stealthwatch were all available for customers to view.
 Feedback from customers and visitors that attended CCI’s presentation “Cybersecurity – Where do I start?” and the “Show Me Security” demos was positive. Folks were encouraged at how easy it is to start implementing a couple products in CCI’s “security castle” design, a multilayer approach, to start defending assets immediately.
Feedback from customers and visitors that attended CCI’s presentation “Cybersecurity – Where do I start?” and the “Show Me Security” demos was positive. Folks were encouraged at how easy it is to start implementing a couple products in CCI’s “security castle” design, a multilayer approach, to start defending assets immediately.
If your organization is ready to have a solid discussion on security tools, tactics or strategy, or would like to learn more about CCI’s “security castle” approach, reach out to me, and the CCI Security Team.
Guest post by Fan Yang & Tony Banuelos
Enterprises across all verticals are migrating their applications to public cloud (IaaS) services and taking advantage of the great cost savings on compute hosting. But the cost benefits shouldn’t affect security, scalability or customer experience. Enterprises require the same level of secure network access, control and visibility in the cloud as they do with on-premise networks. Cloud providers offer basic network functions like IPSEC VPN, BGP routing, NAT. It’s a good enough solution to build a simple site-to-site VPN network with some routing, but enterprises could quickly face these challenges:
- How can I build a hub spoke network with transit routing capability?
- How can I visualize my traffic across different locations?
- How can I select the best path for different applications if I have both Internet and AWS Direct Connect or Azure Express Route at the same time?
With the Cisco IWAN solution running on Cisco CSR1000v, a network admin can extend Cisco IWAN capabilities into a public cloud (AWS, Azure, Alibaba Cloud [coming soon]).
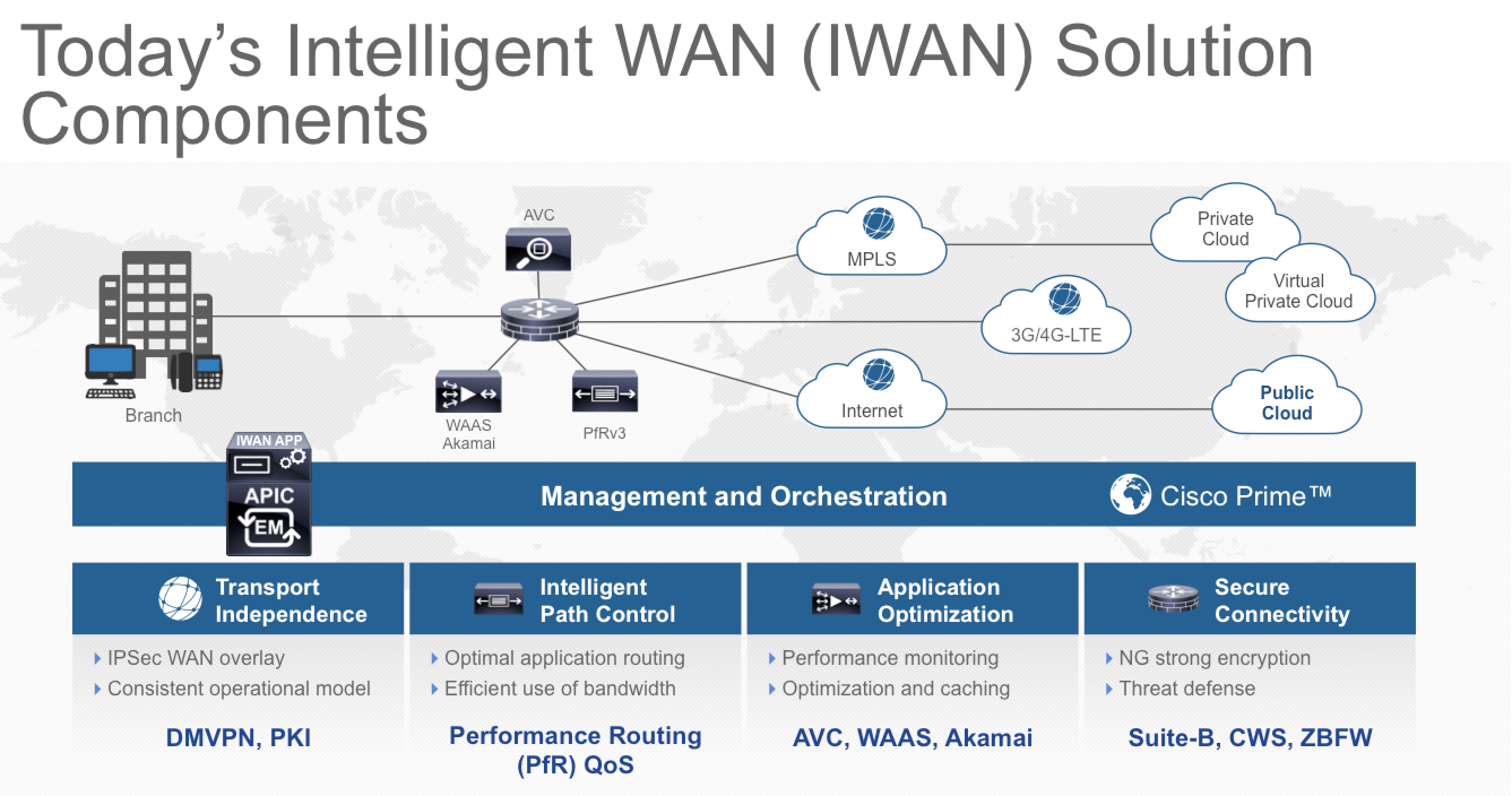
What is Cisco IWAN (Intelligent WAN)?
- Transport-independent design: you can choose whatever combination of providers and connectivity that works best for you.
- Intelligent path control: automatically route network traffic and load-balance based on the “best path” to make sure your applications perform well.
- Application optimization: add WAN optimization and caching to help applications run faster and efficiently using your current WAN bandwidth.
- Secure connectivity: block attacks with highly secure VPN overlay and strong encryption techniques.
How do I provision IWAN?
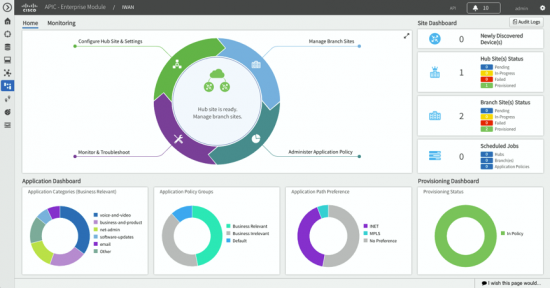
Cisco Application Policy Infrastructure Controller – Enterprise Module (APIC-EM) is the Cisco SD-WAN controller. The IWAN app on APIC-EM simplifies WAN deployments by providing a highly intuitive, policy-based interface that helps IT abstract network complexity and design for business intent. The IWAN Application is prescriptive of the Cisco Validated Design and provisioning of its core pillars for a large number of sites from a centralized location.
How do I use IWAN in public cloud?
The Cisco® Cloud Services Router 1000v (CSR 1000v) is a virtual form factor router that delivers comprehensive WAN gateway and network services functions into virtual and cloud environments. It’s offered in AWS and Azure marketplaces. You can easily deploy it like any virtual machine and manage it through Cisco APIC-EM.
Enterprise customers can have dual links into public clouds. One dedicated MPLS link like Amazon AWS Direct Connect or Microsoft Azure Express Route for fast and private connections, and the other link could be an Internet based VPN. Also, most enterprise customers may have multiple VPC (Virtual Private Cloud) or VNET (Virtual Network) connections across different regions, in addition to their on-premise network. By enabling IWAN capability on CSR1000v, it will help build an overlay network by interconnecting various resources in a scalable way, recognize your application traffic, and split them across multiple paths based on business priority.
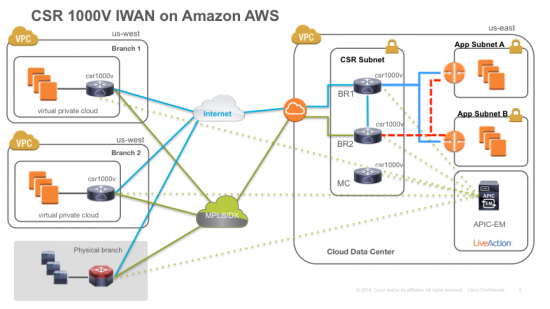
As shown in the network topology above, you may have multiple VPCs in AWS cloud and one physical branch. You can turn your AWS VPC network into an IWAN Hub and spoke by running CSR1000v as an IWAN BR (Broader Router). APIC-EM is hosted in your hub (Cloud Data Center) to provision IWAN services for the IWAN hub and branch, including virtual and physical.
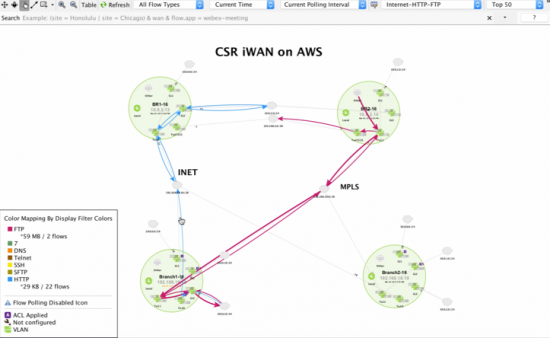
LiveAction is used to visualize traffic for PfR (Performance Routing) path selection. For example, the following diagram shows how “HTTP” traffic is routed through INET (Internet) while “FTP” traffic is routed through MPLS (Direct Connect) based on an application policy set in APIC-EM.
If you are interested in this solution and want to understand more details, please watch our demo video: