Cloud Scale Networking software innovations are the outcome of a partnership with some leading innovators to utilize data center ‘DevOps’ principles and techniques to offer new levels of agility, efficiency, and simplicity. Key benefits include:
- Large-scale automation for provisioning and network changes in minutes vs. hours
- Real-time visibility and control through streaming telemetry along with Segment Routing
- Software extensibility, e.g. Application Hosting, to turn the network into an innovation platform
I’m currently witnessing an adoption of these innovations by major Telecom Service Providers and one noteworthy use case is Central Office transformation.
As a quick reminder, Central Offices play a major role in delivering the last mile connectivity to Service Providers’ end users. Every Service Provider has thousands of them and has been investing for many years in maintaining/upgrading these assets.
One more time, Central Offices require a major overhaul to support the new wave of IoT services and be Service Providers’ growth engine of the future.
Let’s see how Cloud Scale Networking innovations are enabling Telecom Service Providers to transform their network infrastructure from Central Offices up to Data Centers.
Service Providers’ networks are composed of multiple domains – Access, Metro, Core and Data Center. Most of the time, these domains have their own architecture roadmap, are operated by different teams and are using different underlay and overlay protocols. As an example, you may find MPLS and L3VPN respectively for underlay and overlay in the Core domain whereas you may find IP and VXLAN in the Data Center domain. As a consequence, cross-domain orchestration is cumbersome and limited.
To deliver new services, Services Providers have heavily invested over years into purpose-built HardWare (HW) appliances, that were rolled out in Central Offices. But, they quickly found out this mode of operation was not sustainable for some obvious reasons:
- Each new HW appliance requires truck-roll and onsite installation resulting in OpEx increase
- Every HW appliance comes with its own management system that most of the time does not offer standard APIs leading to complex and costly integration. The impact for Service Providers is long certification cycles and slow Time-To-Market. Moreover, each of these HW appliances have their own lifecycle making the upgrade of the overall Central Office a tedious planning exercise.
To overcome these limitations, Service Providers have started to deliver new services from centralized Data Centers, leveraging compute infrastructure and VNFs. This way, they could speed up service innovation and deliver On-demand service instantiation.
But delivering services from centralized Data Centers comes with its own set of challenges. This new mode of operation requires to construct E2E connectivity across the network – from Central Offices up to Data Centers. Unfortunately, this is a lengthy and complex task:
- As underlay and overlay protocols are different across network domains, protocol translations have to take place across all domains. This brings complexity and sometimes requires network devices to maintain states hindering cloud scale scalability.
- These “stitching” operations are still largely manual and require coordination between operations teams.
By and large, you end up having a dichotomy between the on-demand service instantiation in Data Centers and the lengthy procedures required to update the network infrastructure to support those new services.
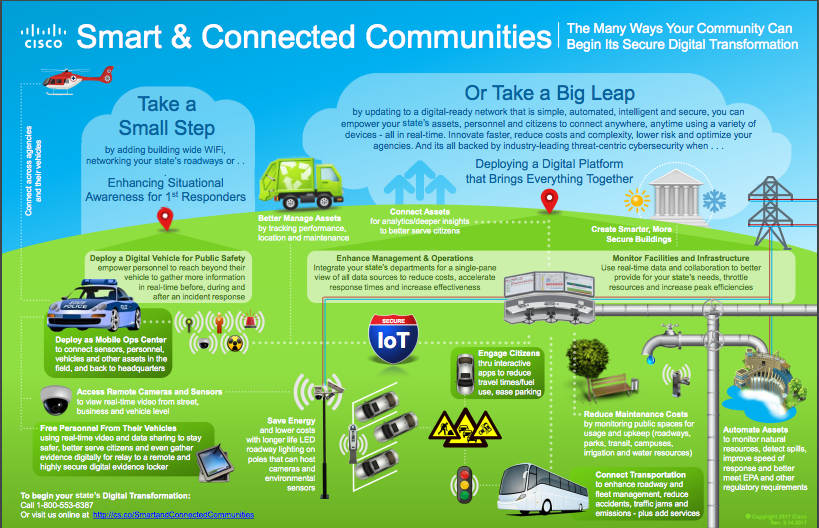
What Service Providers clearly need is a solution where the network infrastructure facilitates the implementation of new services. This new architecture must be logically centralized, for ease of management, with End-to-End network service orchestration capabilities and must be distributed for scalability. The distribution contributes to alleviate the traffic load and this is where VNFs come into play. This architecture strikes the right balance between centralized and distributed approaches.
This is where Cloud Scale Networking solution kicks in. It’s a three-pronged approach:
Simplification
Having multiple different underlay and overlay protocols is simply the result of 20 years of networking evolution. At the time you deployed them, that was probably the right decision though. But you don’t have to be entrenched into that complexity.
Two major innovations, EVPN (Ethernet VPN) and Segment Routing, are game-changers here and can make your network infrastructure more simple and agile.
Segment Routing is increasingly adopted by customer. This unified underlay forwarding plane paradigm brings simplicity – by reducing the protocol stack and leveraging routing protocols’ agility- and consistency across network domains but also comes with network services inherent to Segment Routing – 50ms protection (TI-LFA), low-latency path, disjoint path …
Ethernet VPN (EVPN) enables integrated Layer 2 and Layer 3 services over Ethernet with multi-homing in a scalable and simplified fashion. EVPN provides separation between the data plane and the control plane – allowing for the use of different encapsulation mechanisms in the data plane while maintaining the same control plane. It provides a Unified Overlay Control Plane.
“BGP MPLS-based EVPN enables us to reuse our existing MPLS architecture without adding anything else. It is an obvious choice for Service Providers who already have an MPLS forwarding plane, to start collapsing network islands and be able to launch next generation internet services faster, such as vCE” says Daniel Voyer, Technical Fellow, Bell Canada.
Automation
As networks are getting bigger because of relentless Internet growth, Service Providers are trying to automate their Operations. Two important cloud scale networking software innovations contribute to ruthless automation.
First, streaming telemetry provides fine-grained visibility into what’s happening in your network infrastructure. Don’t forget you can only control what you understand!
Second, model-driven programmability helps you move away from manual operations (CLI) to programmatic interfaces (APIs). Our commitment here is to provide the most comprehensive set of data models (IETF, OpenConfig, Native YANG models) along with model-driven APIs and tools to accelerate the adoption of software automation.
Virtualization
By augmenting Central Offices capabilities with compute resources to increasingly deliver virtualized services, you simply turn your Central Offices into distributed Data Centers. These aging Central Offices suddenly become a competitive edge to instantiate services that benefit from being localized closer to End-Users. (latency, delay – sensitive services)
With this last step, the network clearly becomes a fabric connecting Central Offices to Centralized Data Centers enabling Service Providers to instantiate services wherever that makes the most sense.
We call it Unified “Network as a Fabric” and it is powered by IOS XR.
If you want to learn more about Central Office transformation, listen to Dan Voyer’s presentation at MPLS World Congress 2017.




 This post was written by guest blogger Yuji Suzuki, Manager of Japan Manufacturing Operations.
This post was written by guest blogger Yuji Suzuki, Manager of Japan Manufacturing Operations.