We are quickly moving into an era of accelerated digitization. Where technology connects everything –people, processes, data, and things. These connections will create a sustainable impact for every aspect of society.
It’s predicted there will be over 50 billion connected things by 2020. In order for countries to embrace the opportunities this digital transformation can bring, they need people with the right technology skills.
By embracing digitization, Latin America can become a leader in the next generation of jobs, social inclusiveness, research, and education.
The digital era is now. But is Latin America ready?
A new study from market intelligence firm International Data Corporation (IDC), supported by Cisco, shows that when it comes to the skills needed for digitization, many countries are not.
IDC recently repeated their 2007 and 2012 studies of the IT industry skills gap in Latin America. They used a rigorous proprietary research model which includes data from many sources, including interviews with 760 employers in 10 Latin American countries. IDC tracked essential as well as emerging networking skills in a variety of industries to present an accurate picture of Latin America’s IT employment situation.
The news was fairly good – the gap is shrinking slightly – but the numbers still remain daunting. By 2019, Latin America will lack 449,152 IT professionals. This is bad news for a future where billions of things will be connected in less than 5 years.
The Skills that Drive Digitization
So what are the missing skills that drive digitization? The study focused on three types of skills:
- Essential networking technology skills
- Emerging networking technology skills
- Non-technical skills
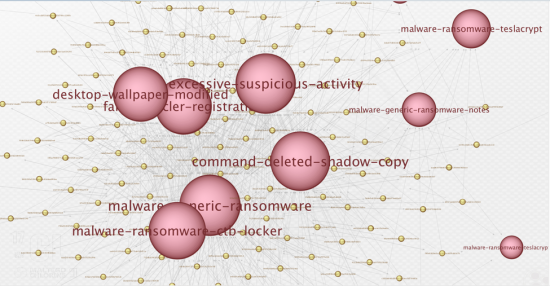
The largest gap (55% of total Full Time Employees skills gap in 2015, growing to 64% in 2019) was in emerging networking technology skills: video, cloud, mobility, datacenter & virtualization, big data, cybersecurity, IoT, and software development. Essential networking skills, representing 45% of the skills gap in 2015 and 36% in 2019, are basic router and switching skills, network security, wireless networking and VoIP and unified communications. The IDC study also showed that networking professionals need non-technical skills to succeed as well. Proficiency in English, team work, problem solving, creativity and innovation, and communication skills are all important.
So what’s the risk of not filling this gap? The International Labour Organization tells us that 21 million individuals in Latin American countries will be unemployed by the end of this year. Delaying digitization risks stifling social and economic development throughout Latin America. Without skilled employees, technological progress does not translate into productivity or growth. According to the World Economic Forum’s 2016 Global Information Technology Report, which measures the capacity of countries to leverage information and communication technologies (ICTs) for increased competitiveness and well-being, Latin America is struggling in the areas of networked readiness and the impact of ICTS on government efficiency and basic services. The region continues to move up in ranking, but more work needs to be done.
Filling the Gap – Not as Simple as it Sounds
What’s the solution? On the surface, it seems simple: train more people with the right IT skills. But it’s more complicated than that. There are not enough teachers with the right training. Internet access (which could provide the training remotely) is limited in the region. And, most fundamentally, there is a lack of students who are interested in learning these tech skills.
It’s going to take everyone working together — schools, corporations, government agencies and local communities — to solve these problems and fill the skills gap from the bottom up. This effort has recently gained momentum though, with the announcement of two collaborations.
The first collaboration’s goal is to connect all classrooms to the Internet and transform the quality of digital education in Latin America. Comprised of a diverse group of organizations (CAF, the Development Bank of Latin America, the Economic Commission for Latin America (CEPAL), and Cisco), one of their primary objectives is to gain support from national lawmakers to prioritize internet access. Mario Castillo, New Technologies and Innovation Chief, CEPAL, reiterates the importance of this effort: “IT adoption is crucial for social and economic development. To reach it, policies that promote access to internet and use in high impact areas such as education are required.” He’s right. According to the Inter-American Development Bank (IDB), countries that increase their broadband penetration by 10% enjoy, on average, a 3.19% increase in GDP, a 2.61% increase in productivity, and 67,016 new jobs.
The Organization of American States (OAS) is leading another regional effort, which is dedicated to ending poverty in the region through the use of information and communication technologies. This initiative, which is part of the 2030 ICT Alliance for the Americas, looks to expand connectivity in Latin America and provide training for active participation in the digital economy. Together with the OAS, information and communications technologies companies, universities, and the Economic Commission for Latin America and the Caribbean (ECLAC) have committed to join and support efforts to connect the next 1.5 billion people and every public school in the region to the internet. They will also promote digital training, improve the quality of education, and develop talents for the new digital economy, preparing students for entry-level ICT jobs.
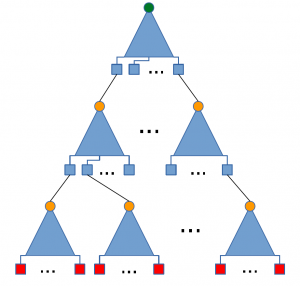
Cisco is also contributing to this effort through Cisco’s Networking Academy. The Cisco Networking Academy partners with learning institutions, community centers and governments to offer technical training and professional skills development training. The curriculum, which adapts and changes with technology trends, is currently focused on networking, security, and Internet of Things (IoT) technologies. One million of the six million people who have taken courses since 1997 are in Latin America.
Generating Interest in IT Careers
It’s encouraging to see organizations working together to bring internet access and technical training to Latin Americans. But Latin America needs a lot more people to get interested in and enroll in these programs if it is going to fill that skills gap.
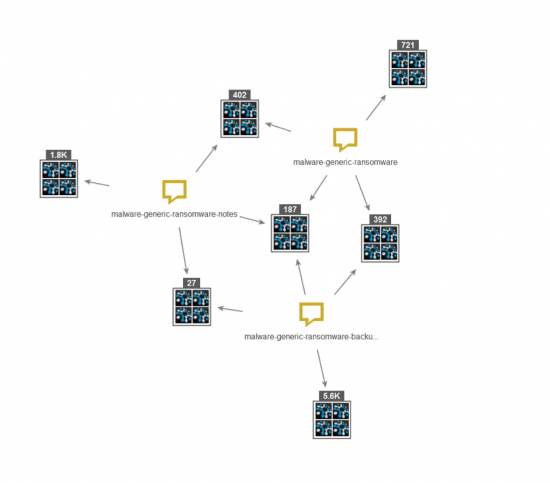
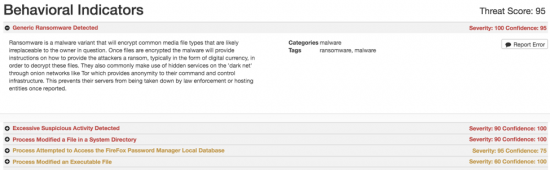
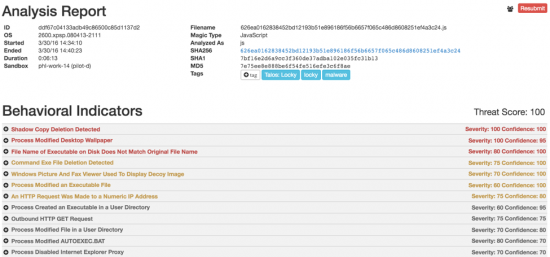
Cybersecurity is one of those emerging networking technologies that is becoming more and more critical. An understanding of cybersecurity – knowing how to keep information and operational technology secure — is one of the most sought-after skills in the digital world right now. Amanda Cumberland, Head of Strategic Research for Corporate Affairs at Cisco, explains: “Cybersecurity strategies are an integral part of digitization and are critical to its success. The latest IDC study found that 86% of companies in Latin America have a cybersecurity strategy. Security is central to digitization.” But a predicted global shortage of two million cybersecurity professionals by 2019 limits the ability to adopt technology, accelerate economic growth, improve productivity, and create new jobs. We need to get more people interested cybersecurity. But how?
One solution is to reach out to new audiences, and offer them incentives. Cisco is investing $10 million in a two-year Global Cybersecurity Scholarship program to grow interest in cybersecurity careers. The program is looking for participants in some unconventional places: community centers in Costa Rica and Mexico, and other diversity organizations. To recruit scholarship recipients from a relatively untapped audience, Cisco is partnering with events like “International Girls in ICT Day,” which empowers and encourages girls and young women to consider careers in the information and communication technologies.
According to the IDC study, women comprise one of the most promising new markets for networking skills training. Currently women represent only 13.3% of networking employees in Latin American companies. And 15.7% of Latin American companies have no women on their networking teams. However, 31% of Computer Science and Engineering majors in the region are women, and 23% of Cisco’s Networking Academy students are female. The future looks bright for female networking programmers.
It looks bright for Latin America as well, as digitization continues to transform Latin American countries, cities, businesses, education, and job markets. The way forward is clear, and we are all working to prepare for a digital future. Together, we can close the gap.
 Highlights:
Highlights: