This is the first in a series of blogs about advanced malware
Behavioral Indicators Morph Over Time
A large part of Threat Grid’s efficacy in determining the nature of a submitted file is through the use of over 675 indicators to identify malware. The initial indicators created for AMP Threat Grid sought to identify strictly the behavioral elements of a submission. Over the years however, these indicators morphed beyond identifying simple behaviors, to include static forensic attributes, and finally to include the positive identification of malicious families and variants. The latter achievement leads directly to an increase in the contextual data provided to customers, and also making a significant difference when addressing a specific threat.
In an effort to combat the growing threat of ransomware while providing this context-rich analysis, AMP Threat Grid has positively identified over 39 different ransomware families and 15 variants to-date. With the ever-increasing amount of ransomware being seen on a weekly basis however, merely creating indicators or signatures in a purely reactive state is not enough. AMP Threat Grid has therefore created several indicators that generically identify malicious behaviors related to ransomware. This helps our customers detect a potential new ransomware variant even if we don’t yet have a name for it.
One of the oldest behavioral indicators identifies the deletion of shadow copies. The deletion of shadow copies was first implemented in Cryptowall after a write up identified the fact that recovery could be made without paying the ransom. As a result, many authors moved to include this [behavior] through a variety of means to gain the use of Windows native utilities and Windows scripting host. When the results for this indicator were reviewed for efficacy, we discovered that 100% of the samples exhibiting the behaviors cause by this indicator were malicious. Having reviewed the data, we concluded the threat of this behavior warranted an increase in threat score. Threat scores provide a quantitative measure on a scale of 1 to 100 of how confident we are of a sample’s maliciousness based on the behaviors it exhibits when executed in Threat Grid.
Ransomware Indicators
Generic Ransomware Notes Detected
Several recent additions have contributed to an increase in detections of ransomware variants in AMP Threat Grid. These include a behavioral indicator titled “Generic Ransomware Notes Detected,” which detects the presence of ransomware notes identified by common characteristics of the instructions left by ransomware.
Generic Ransomware Detected
These Generic indicators work separately or in tandem to convict emerging ransomware threats. This multifaceted approach provides greater detection than one of these functioning on its own. These Generic Ransomware indicators allow us to convict ransomware first, then focus on identifying the specific ransomware family.
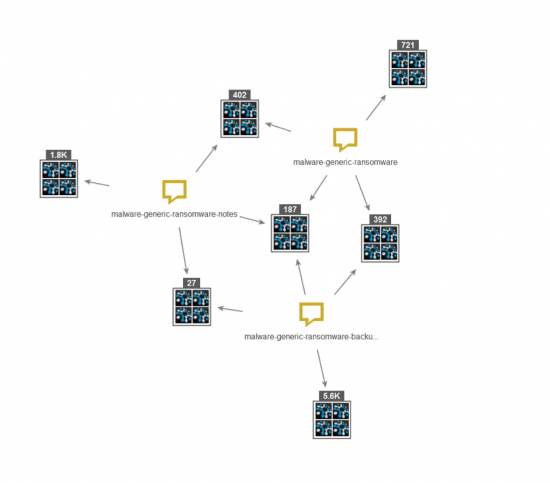
Generic Ransomware Backup Deletion
Since ransomware began deleting system backup files as discussed above we created an indicator to detect this behavior. We see below this indicator works well with our other generic indicators to confirm overlapping behaviors and identify other samples.
Overlapping Triggers
By taking any of these indicators in isolation and graphing search results in Malformity Labs Maltego using the AMP Threat Grid API transform pack, we begin to see there is some overlap in triggers. In this case we search for a single indicator: “generic ransomware”. We pivot on the sample IDs, then pivot again on the indicators for each sample. The results start to show overlap with each other but not every instance triggers on the same sets.
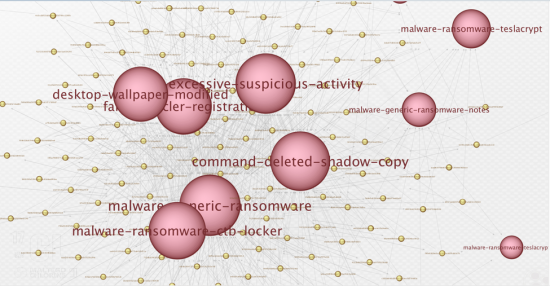
The overlap allows us to group indicators together and to create indicators we’ve labeled as compound. That is, several actions combined indicate malice with a higher degree of confidence. Absent the overlap, the results also allow us to identify new families of ransomware as well as new behaviors from existing variants.
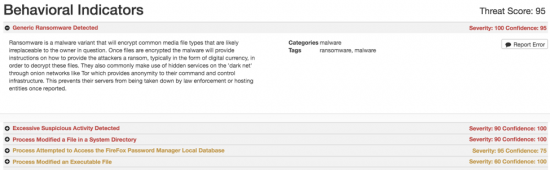
Excessive Suspicious Activity Detected
Another recently added behavioral indicator is “Excessive Suspicious Activity Detected”. With this Behavioral Indicator, AMP Threat Grid is observing several traits over a set of files. If we observe these behaviors / traits, then there is a high level of confidence the sample is malicious and returns a higher threat score. In this way, AMP Threat Grid is able to identify new ransomware families, and shifts in existing variants.
The Excessive Suspicious Activity indicator was added in early February of 2016, and at the time of this writing we’ve seen a total of 1,830,488 triggers in the field. To highlight the benefit of these generic indicators we turn to an article written by Lawrence Abrams, published on bleeping computer, April 20th [1] highlighting the discovery of TeslaCrypt 4.1b.
After reading the article and searching the AMP Threat Grid Elastic Search instance for key indicators, it was discovered that because of the excessive suspicious activity indicator, the first instance of TeslaCrypt 4.1b was observed in the AMP Threat Grid environment on March 30th, 2016. That first instance, as well as subsequent observations of the new TeslaCrypt variant, were all given a malicious rating throughout the AMP portfolio a full 3 weeks prior to the public observation of the new variant.
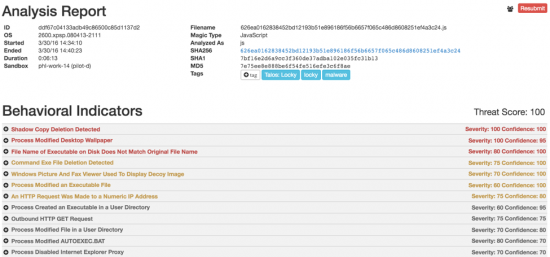
JavaScript Ransomware Downloaders
Finally, towards the end of March 2016 we started to see ransomware downloaders in the form of JavaScript files. Initially many sandboxes and even endpoint products did not support the analysis of this type of file, after all it’s rather difficult to identify and even Magic’s filetype identification shows it as Text more often than not. To address this delivery mechanism, AMP Threat Grid has added support for JavaScript file submissions. These files will execute in the sandbox environment just as other submission types.
Locky was one of the first families identified as using this technique. Finding one of the downloaders on Virus Total, we submitted it to AMP Threat Grid and once analysis is complete we get a full picture of everything the downloader – and subsequently the downloaded binaries – are doing.
As existing ransomware variants continue to morph and new families are introduced on nearly a weekly basis it becomes increasingly difficult to keep up with the task of identifying and writing specific signatures for each one. To that end, the indicators covered in this post have contributed heavily towards early detection of ransomware families and variant shifts as we see them. In the month of June alone, the indicators outlined in this post identified and proactively blocked over 1.1 million ransomware samples, protecting customers from having their data encrypted and disrupting business operations.
Check back here for a technical deep dive on the CryptXXX ransomware threat to learn how AMP Threat Grid can help protect your organization from malware. The next article will dive into CryptXXX to demonstrate how AMP Threat Grid engineers reverse malware to create targeted behavioral indicators we use in conjunction with our generic indicators to detect the ever evolving threats.
In the month of June alone, the indicators outlined in this post identified and proactively blocked over 1.1 million ransomware samples, protecting customers from having their data encrypted and disrupting business operations.
Cisco AMP Threat Grid is a malware analysis and threat intelligence platform, which is available as a cloud-based subscription service as well as on-premises appliances for those customers with stringent data privacy requirements. AMP Threat Grid is integrated with other Cisco products and third party solutions.
AMP Threat Grid performs static and dynamic malware analysis of unknown samples, which is combined with integrated threat intelligence into one unified solution. It provides the timely, in-depth information you need to protect your network from all types of malware threats. Threat Grid combines real-time behavioral analysis with up-to-the-minute threat intelligence feeds and existing security technologies, offering protection from both known and unknown malware attacks.
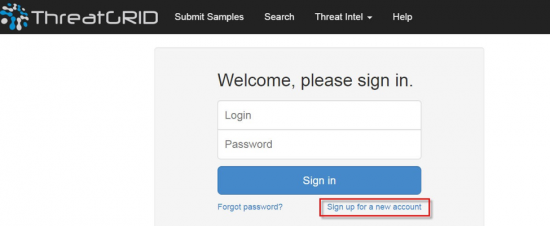
Sign Up for a Trial Account
If you would like a personalized AMP Threat Grid demonstration and trial account, you can go to https://panacea.threatgrid.com and click on Sign up for a new account.
[1] http://www.bleepingcomputer.com/news/security/teslacrypt-4-1b-released-with-few-modifications/]
Be sure to watch our webinar, The modern way of hunting – How three CTOs tackle incident response, hosted by SC Magazine featuring Dean De Beer, CTO at ThreatGRID, Dan Hubbard, CTO at OpenDNS, and TK Keanini, CTO at Lancope as they discuss what it takes to accelerate investigations, decrease incident response times, and uncover potential attacks before they are launched.








Love this, Eric! Great job!
…After reading this post, I can rename it to: “The General Behavior of Ransomware 101”. Very detailed and interesting indeed. Thanks for sharing it.