Let’s face it. Taking on a major technology migration can be a complete headache. There are so many risks involved—not the least your reputation and job security. If you are concerned about your vendor’s future, your headache may have turned into a migraine as you ponder migrating to a new collaboration platform sooner than you had planned.
As the saying goes, with every cloud, there’s a silver lining. What if you could migrate from your current platform with a proven, cost-effective deployment? Cisco can do that for you.
More than 74% of Fortune 100 customers trust Cisco Services to implement and optimize their enterprise solutions.
Let Cisco Advanced Services make you the hero and deliver the collaboration platform for the way you work today. Today, more than 74% of Fortune 100 customers trust Cisco Services to implement and optimize their enterprise solutions.
Our Advisory Services Strategy and Innovation Workshop can help you map out a migration plan aligned to your goals. Then, take a test drive in a pilot deployment as part of our remote expert hosted trial.
Our Implementation Services team offers proven migration methodologies to help streamline your move to Cisco collaboration. In fact, we recently helped a global insurance agency migrate more than 12,000 agents from a competitor’s contact center to Cisco Unified Contact Center Enterprise within 18 months. Our deep services expertise can help you quickly build a secure collaboration environment, increase team productivity, and realize a faster ROI.
Let Cisco Advanced Services for Collaboration help ease your headache before it turns into a migraine. In the meantime, take two aspirin. We’ll call you in the morning.
 By Giovanna Carofiglio, Distinguished Engineer
By Giovanna Carofiglio, Distinguished Engineer The
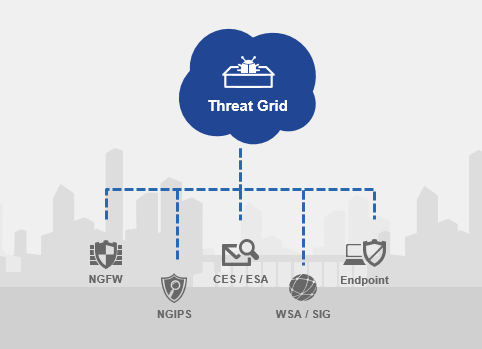
The  that? What if you just want to have your security tools automatically submit samples to a sandbox and check if it’s good or bad – and block those bad files? It seems so simple! A few years ago most customers I was talking to were deploying a bunch of expensive appliances on each of their network segments. However, as Frank Costanza said “there has to be a better way!”
that? What if you just want to have your security tools automatically submit samples to a sandbox and check if it’s good or bad – and block those bad files? It seems so simple! A few years ago most customers I was talking to were deploying a bunch of expensive appliances on each of their network segments. However, as Frank Costanza said “there has to be a better way!”