Over the last half decade the term sandboxing has become so pervasive, many customers I speak to have forgotten what it’s for! Sandboxing is a type of malware analysis – dynamic malware analysis to be exact. You execute a sample / file in a virtual environment and see what happens. There are numerous other types of analysis including static analysis, where we look at the code and compilation of the file, forensic analysis of in-memory activity and patterns on disk, as well as pre- and post-execution analysis of the master boot record. In short, Threat Grid is a comprehensive malware analysis engine.
Recently we showed how it can be used for investigations in this blog. But what if you don’t have time for  that? What if you just want to have your security tools automatically submit samples to a sandbox and check if it’s good or bad – and block those bad files? It seems so simple! A few years ago most customers I was talking to were deploying a bunch of expensive appliances on each of their network segments. However, as Frank Costanza said “there has to be a better way!”
that? What if you just want to have your security tools automatically submit samples to a sandbox and check if it’s good or bad – and block those bad files? It seems so simple! A few years ago most customers I was talking to were deploying a bunch of expensive appliances on each of their network segments. However, as Frank Costanza said “there has to be a better way!”
Not all analysis are created equal. On one hand you can use a free open source cloud based sandbox. On the plus side it’s free. The downside is all the malware authors use the same free opens source sandboxes to test their malware against. They are designing their stuff to evade these environments.
Threat grid provides malware analysis and threat intelligence across the Cisco security portfolio. Regardless of a sample’s submission origin, the subsequent intelligence derived informs all integrated products. It also provides a single common view into all the potential malware samples being seen across your infrastructure.
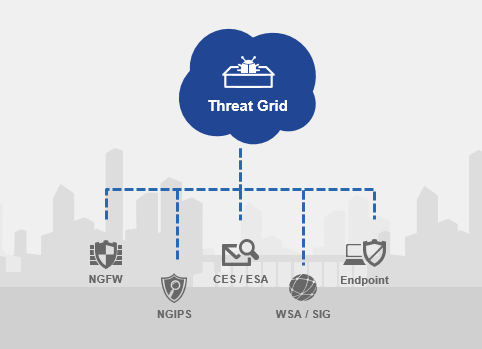
Figure 1: Integrated across Cisco security portfolio
Any Cisco security technology you invest in will provide you with a number of samples that you can submit to Threat Grid on a daily basis. You can set policies on what you want submitted automatically. If you don’t want to deploy a bunch of appliances around your network, we can simply increase the number of samples you can submit from each of those with sample packs. These allow any of your Cisco security devices to send more samples to be analyzed so you don’t get caught with a pile of malware that you weren’t able to inspect.
Don’t use the same engines that malware authors are using to test their code against. Leverage your existing Cisco investments to analyze, detect, and block more malware. More information is available on the Threat Grid web page, or sign up for a free trial account here.






Imformative article
Very useful, Thanks.
I could read a book about this without finding such real-world aprphacoes!
I am confused would yo get both AMP and one of the NGFW ASA or 2100. Or does the ASA, 2100/4000 series replace the AMP
Clear, inaifmrtove, simple. Could I send you some e-hugs?
Starr, I think you just did! 🙂
Peter, AMP is a separate license that can be added onto a new or existing firewall. It provides continuous monitoring and retrospective security, along with the sandboxing capabilities mentioned above. Check it out here: http://www.cisco.com/go/amp
Life is short, and this article saved vaablule time on this Earth.