The Cisco Infinite Video Platform can enable service providers and OTT video businesses to cater for the complex multi-screen habits of today’s viewers
The way we watch video is changing. Yes, people still sit down in front of the TV to watch live programmes – but increasingly, this is only one part of a much bigger picture.
Maybe someone wants to pause watching a film on TV and pick it up at the same point on their phone a few hours later – perhaps in a different location. Perhaps they’d like to record a live sports broadcast on their set top box while also streaming it to their desktop computer at work. Or they want to be able to set which content their kids can view, whether on the TV, games console or tablet.
Figures from the Global Web Index show that millennials own an average of 3.45 video devices. And with Cisco research predicting that there will be 11 billion connected devices by 2020 , things are only going to get more complex – to include screens in cars and planes, for example.
This kind of behavior causes problems for service providers, whose legacy systems are already struggling to cope with the growth and huge variety of demand for online video.
Offering video services limited by device isn’t enough anymore. Service providers now need to offer bespoke, flexible services on any device – whether provided as part of the contract or already owned by the customer – and across any network.
Integrated solutions
Cisco’s next generation video solutions can help service providers succeed in this new future. They use an integrated, cloud-based platform for online video that makes it easy for providers to create, deploy and refine new services, regardless of which device or network they’re using.
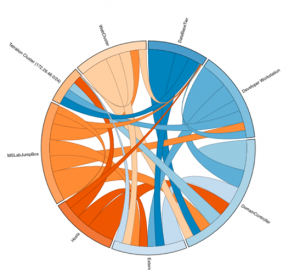
At the moment, service providers are still delivering video using an inefficient, fragmented infrastructure, with broadcast, on demand and over the top video content each distributed along separate pathways. This is inefficient, and as demand becomes more complex, it’s going to become more and more tricky.
This is where the Infinite Video Platform comes in. It brings together these different platforms, making it easy for providers to distribute content wherever they like – including on devices and networks that they don’t manage. This saves operational costs, enabling providers to meet the challenges of the future.
One business that has used Cisco technology to transform its entertainment offer is D-Smart, the Turkish satellite television provider. The company needed a cloud solution that could enable it to quickly expand the variety of services it provided for its customers across multiple screens. It also wanted to create a new user guide that could easily blend multiple sources of content.
D-Smart found that Cisco’s Infinite Broadcast Solution would support it in creating these new customer services . Summarising the appeal of the technology Erdogan Simsek, the chief technology officer of D-Smart, said: “Cisco offered us a flexible cloud software solution to easily merge the worlds of online video and live broadcast TV.”
Scale workflows easily with Virtualised Video Processing
The IVP also includes Virtualised Video Processing technology, which allows users to operate a single production line for all video workflows. It intelligently orchestrates different functions such as encoding, recording and delivery.
This means that both service providers and media companies can easily scale workflows to support the video services required for distributing content to many different screens.
A world of opportunity
For example, a family could all sit around the TV watching a major show, but each person could also view content of particular interest to them on their own personal device. So they could each be reading about the actors, past episodes or filming locations on an app while watching the programme.
And this is just one example of the vast range of functions that are possible with the IVP. It enables existing service providers to meet the challenges of the future, while also making it possible for new businesses to enter the market and grow in a way that suits them.
The massive growth of online video offers huge rewards for those that get it right, but providers will need to be prepared. Why not work with Cisco to create the agile services of the future?
Do you want to seize new revenue opportunities by supplying content across all devices?