Defending a network against threats of growing complexity requires a mix of technology and policies that are as sophisticated as the campaigns created by attackers. A necessary component to an efffective defense includes tackling the low-hanging fruit—that is, basic tasks such as patching vulnerabilities and updating old software.
However, as we relate in the Cisco 2016 Annual Security Report too many organizations are relying on seriously outdated network components and operating systems—thus providing even more opportunity for adversaries to infiltrate or attack their network.
As explained in the report, we recently analyzed 115,000 Cisco devices on the Internet across customer environments to better understand the risks that aging infrastructure presents. We viewed the devices by scanning the Internet and then looked at them from the “outside in” (from the Internet view and into the enterprise). We found that 106,000 of the 115,000 devices, or 92 percent, were not running the latest versions of software, exposing them to vulnerabilities.
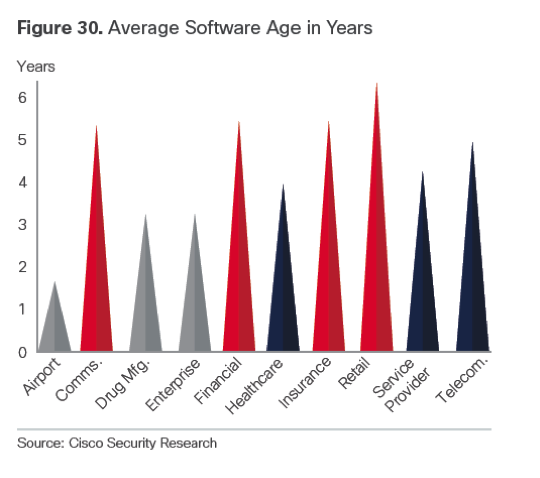
In addition, we found that the version of the software the devices were running had 26 vulnerabilities, on average. In fact, some customers were running software versions that were more than 6 years old- the implication being software that old is likely to have many known vulnerabilities. Many of the infrastructure devices we analyzed also had reached their last day of support (LDoS), which means the devices are not even receiving patches for vulnerabilities.
Why is aging infrastructure such a concern? Outdated components and software provide an easy opportunity for online attackers to breach networks. The need to upgrade infrastructure may not have been viewed as a priority for organizations as recently as 10 years ago, since they did not realize that attackers would make infrastructure a key target. The attackers realize that many business are nearly 100 percent reliant on their network infrastructure and as a result it’s easy to see the progression of attacker behavior to target the infrastructure itself.
Upgrading infrastructure is a costly undertaking and requires network downtime, so it is understandable why many organizations are inclined to put this task on the back burner. However, the costs of ignoring the problem of aging infrastructure can run much higher—namely, in the form of a devastating attack. Organizations therefore need to move upgrading components and software to the top of their to-do list—and make regular maintenance a part of their security strategy. Customers who do so will reduce their risk and increase the resilience of the backbone of their business- the network infrastructure.
Please download the report and continue reading about aging infrastructure and other pressing security topics.






I wish more people would listen …
But as long as there are admins that are proud of the 2yr uptime of their internet-facing firewall, I only have limited hope!
Like creaking rusty pipes in a beautiful home, the risk for compromise is real…
Very interesting article, agree with the above that it is no surprise. There is also a huge cost of change especially in the financial and retail industries and probably an attitude to say if it aint broke dont fix it.