Business costs from the recent WannaCry ransomware attack are still being tallied and data center managers are quickly assessing their vulnerabilities within their data center infrastructure.
There are two immediate questions to think about when evaluating your operating environment and the applications that run on these systems:
- Are they running on current software releases?
- Is the underlying infrastructure of switches, routers and servers updated to their latest firmware releases?
There are other methods data center managers can deploy to detect ransomware and cyber attacks before they spread and do their damage. Consider using newer tools like Cisco Tetration Analytics that search and explore tens of billions of flow records, and by leveraging machine learning, provide actionable insight in less than a second.
Three Immediate Benefits to Having Pervasive Visibility and Control in Your Data Center in Real-Time: 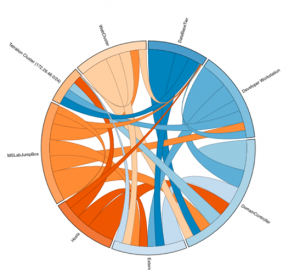
1. Ability to create policies around all your information which enforces tighter security between applications running across data centers, segments applications between various business entities, and applies an overall white-list model to the entire data center.
2. Automatically enforce a dynamically created policy in the hosts, no matter where they’re deployed – on premise, in the cloud, or a combination of the two.
3. Monitor the system to make sure the policies that are in place are, in fact, enforced and more important, see who is trying to work around those policies to create security breaches within your data center.
Are you ready? Learn how Cisco Tetration Analytics can help your data center be prepared for the next cyber attack. http://www.cisco.com/go/tetration




Good read !