Organizations differ — often radically — in the kind of collaboration solutions they need. And the solution today needs to be flexible to adapt to what comes tomorrow. Agility in technology is key to agile business.
Your organization’s IT customization levels evolve. It’s not just about bringing in the latest products or plugging in simple off-the-shelf solutions. Most important is to establish a foundation with which you can work to best suit your evolving and unique needs.
As new options pervade the market, employees expect work technology to be simple, natural to use, yet easy to customize. In the end, it’s the user experience that counts. And especially in a world where we measure IT against modern online consumer experiences.
Cisco has a unique ability to fulfill these needs. That is the Cisco advantage.
When it comes to foundational business technology, it’s about a pedigree in innovation. Cisco was an early enabler of the Internet and creating connections – not just between machines but between people.
As the Internet progressed to become the great unifier of the digital world, Cisco identified more ways to help people connect and collaborate. It’s a constant cycle of innovation that benefits from the convergence of hardware, software, and the network.
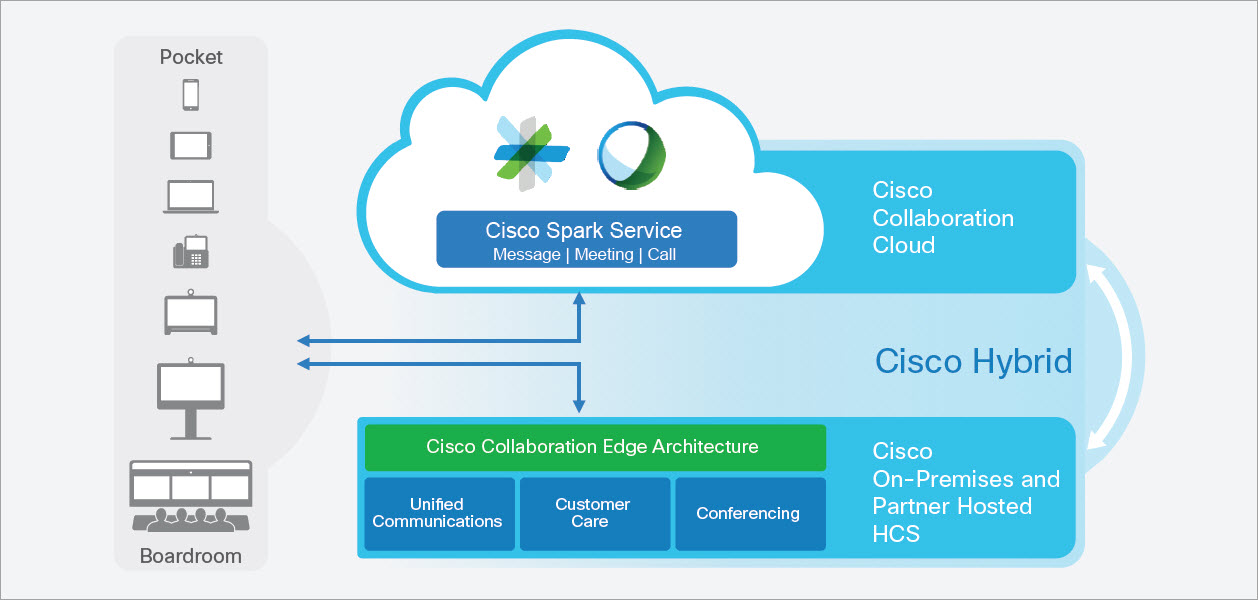
When it comes to collaboration, Cisco’s journey has progressed quickly. It started with the convergence of data, voice, and video, then moved into simplifying the collaboration infrastructure. This paved the way for high-quality video, making web conferencing and video conferencing accessible beyond the executive boardroom all the way to the device in your pocket. As these elements evolve, they continue to contribute toward dramatically simplifying and improving the way we share information, evolve work styles, and advance productivity.
As we continue to evolve, our focus is on delivering agility through better collaboration, taking advantage of:
- The depth and breadth of our product portfolio
- The integration of software, hardware, and the network
- An interoperable, open standards-based platform paired with shared services and elegant applications
- The cloud collaboration platform with capabilities of unified communications, contact centers, big data and analytics, and the Internet of Things
- Extraordinary partnerships
Our collaboration portfolio unifies these elements with an architecture engineered for a delightful collaborative experience.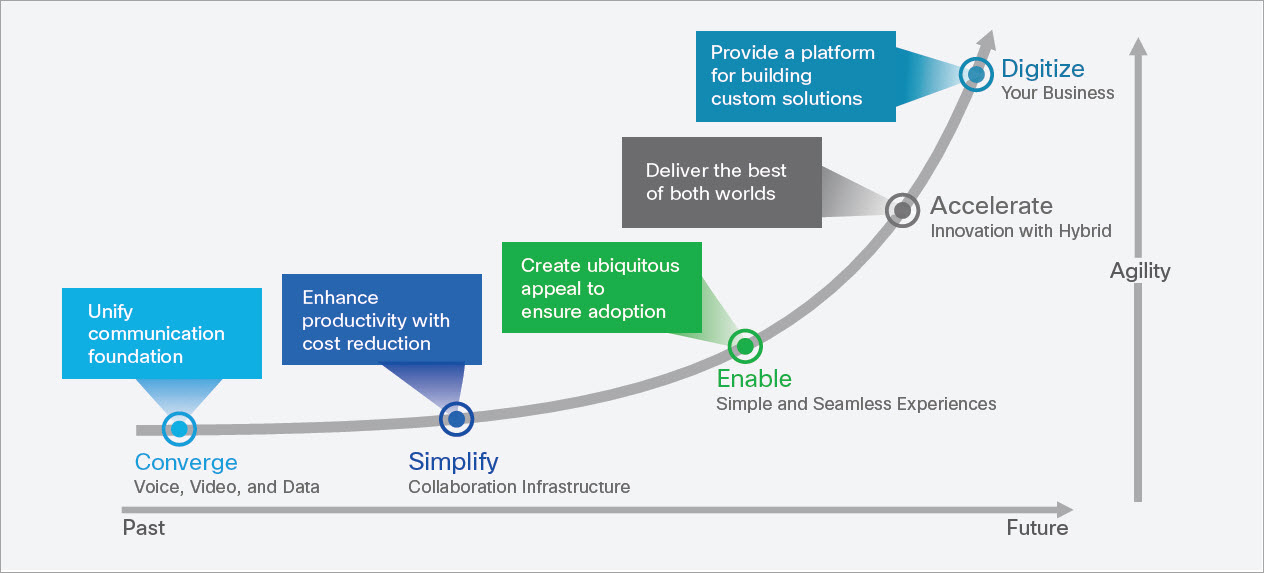
When it comes to collaboration technology, only Cisco offers the combination of hardware and software engineered from the first bit to integrate with the network. And that makes business sense because it provides you with:
- Simplified procurement decision making
- Significantly lower vendor-management expense
- End-to-end solution design without complex multi-party integration
- Avoidance of vendor lock-in due open architecture and standards-based implementation
- Competitive pricing and future-proof solutions for every business need
- Access to easily customizable, award-winning support
Cisco’s integrated approach protects your investment, while also making it personalized and controllable. It embraces the basic principles of communications, while providing flexibility as your organization – and technology — evolves. These make it easy to design, buy, implement, deploy, and to use.
Let’s be real: Collaborating effectively is not easy.
It comes down to this: user experience.
That means we’ve focused on creating a delightful user experience across the board. And not just the end user. You can create a beautiful end-user experience, but if it’s hard to implement, manage, and adapt, you haven’t succeeded. We’ve designed the experience to be delightful to the IT architect, the IT operator, the developer, the help-desk professional – and, of course, the end user. Everyone is included in the broader Collaboration ecosystem of users.
More than 200,000 organizations worldwide use Cisco Collaboration solutions – whether in the cloud, on premises, or a hybrid. Cisco is a partner of choice across industries. Support from Cisco and its well-established partner ecosystem can help you gain fast time to value from our portfolio.
Industry leaders and analysts like Gartner, IDC, and Frost & Sullivan continually recognize and award Cisco’s leadership in collaborative technologies. Products across the portfolio have also received multiple Red Dot awards for high-end design. These represent a small sampling of our global pedigree.
Now Is the Time to Act
Collaboration is the key to delivering solutions that drive business outcomes. Demands are changing constantly. Digital transformation, social networks, mobility, the Internet of Things, and whatever comes next are defining the future workspace – today.
People are using technologies to create new connections and approaches to collaboration. Cisco helps you cut through the noise with integrated solutions that are flexible to your needs, how ever and wherever you communicate. It’s all about transforming tools into conduits for innovation, letting you focus on what you’re doing, not the tools you’re using to do it.
“The most inventive places are hives of activity where people get together and share ideas.” —Steven Johnson, author, Where Ideas Come From
In its research, Dimension Data reports a strong emphasis on collaboration in businesses today:
- 88% of enterprises say collaboration has improved decision-making process in their organizations
- 81% say collaboration has enhanced their ability to engage with customers and improve customer service
- Productivity enhancement stands out as the most important goal of enterprises’ collaboration strategies
Ensuring sustained innovation across your organization is critical. And that means putting collaboration at the core of your innovation strategy.
It always comes back to collaboration. Collaboration is a journey, not a destination. This journey itself is the path to agility. So are the opportunities for your business.
Next Steps
Explore more about how Cisco Collaboration technology can help create a more innovative, agile business environment.
This is the fourth post in a four-part series. Read the previous posts here:
Collaboration: The Foundation of the Agile Business
The Way We Work is Changing
Cornerstones of Agile Business
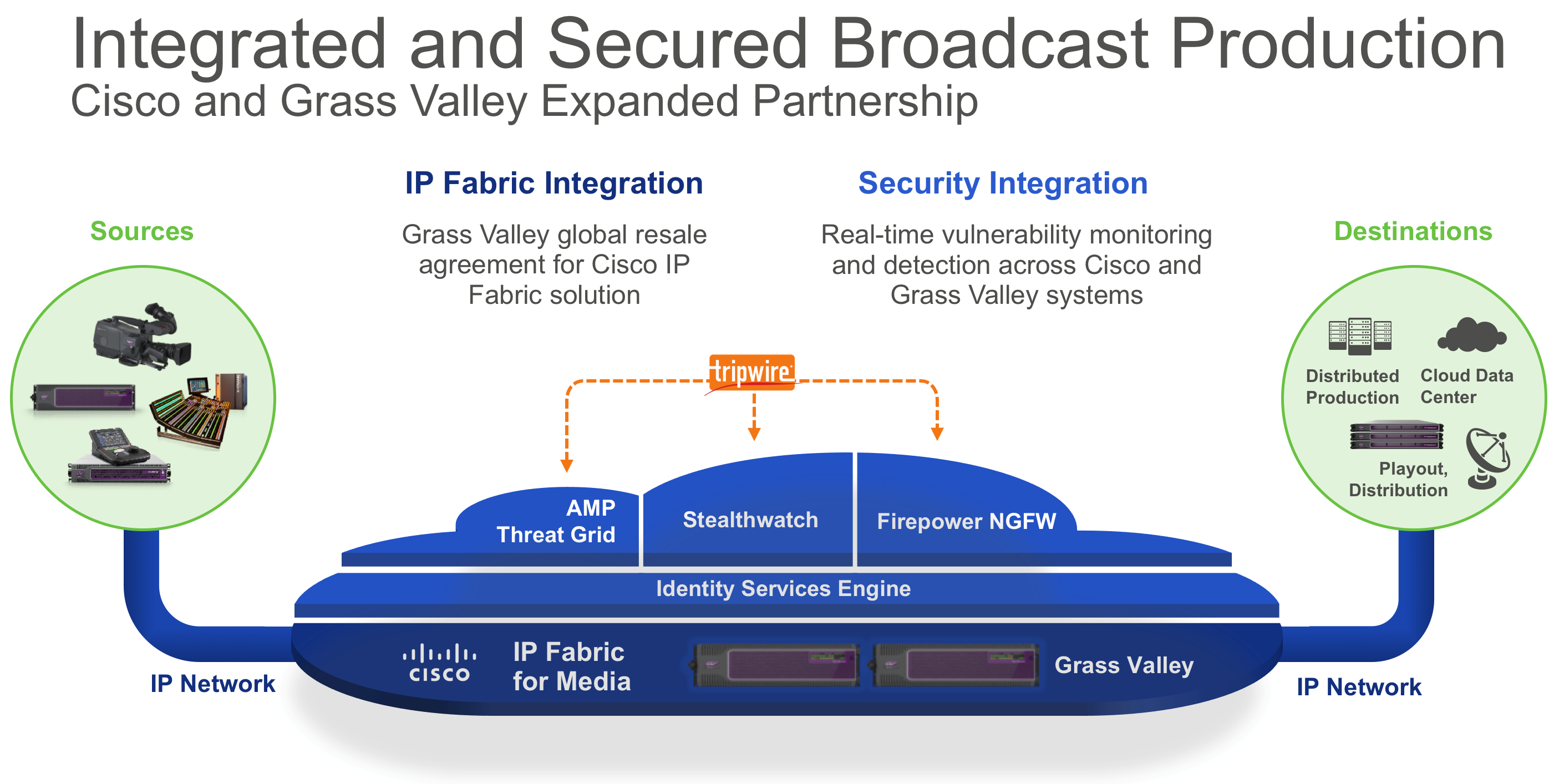
 By Ted Rose, Operational Security, Service Provider Video Software and Solutions, Cisco
By Ted Rose, Operational Security, Service Provider Video Software and Solutions, Cisco




 From
From  If each Terabyte in a Zettabyte were a kilometer, it would be equivalent to 1,300 round trips to the moon and back (768,800 kilometers).
If each Terabyte in a Zettabyte were a kilometer, it would be equivalent to 1,300 round trips to the moon and back (768,800 kilometers). From
From  From
From 
