In the past 15 years we’ve developed data virtualization products and solutions to keep our customers ahead of the game for many different needs. Our world-renowned engineering provides the competitive advantage our customers have come to rely on. From strategy to infrastructure, from access to analysis, I’m proud of the architectural solutions that drive the highest levels of performance and scalability that fully align technology investments to our customers’ business goals. Today, I’d like to share a few of my favorite operational use cases with you.
An IT Transformation for Power Outage Management: Long Island Power Authority
Hurricane Sandy left roughly 90% of Long Island Power Authority’s (LIPA’s) 1.1 million customers without power, leaving many without power for weeks. LIPA experienced significant issues delivering outage information due to middleware and interface performance and reliability during the stresses of the storm. As the response was the slowest on Long Island, LIPA knew they needed a new storm process with a supporting power outage management system and a transformation of the IT infrastructure.
LIPA selected the Cisco Information Server, the foundation of the Cisco Data Virtualization Suite, for its data federation, query optimization, and enterprise data-sharing capabilities. This enterprise-level system meets the needs of operational and regulatory reporting, while serving the real-time needs of customers. What was once deemed a 3-year project was completed in less than 12 months with Cisco Data Virtualization with 50% faster data integration and 150% improvement in outage location accuracy.
Optimizing the Customer Experience: Comcast
Millions of Comcast customers use comcast.com or comcast.net to manage their Comcast products and services online. Supporting this process involves many products and many disparate data sources that have to be integrated in a variety of ways depending on what the customer needs. A critical challenge was optimizing the process of executing ownership changes on an account. What seems like a simple request has quite a bit of complexity involved with a hierarchy of permissions.
Cisco Data Virtualization was brought in to improve both the performance and accuracy of ownership changes. Comcast’s entire ownership change process is now handled in the data virtualization layer. With this solution Comcast has reduced transaction time for processing a request from 5 seconds down to 1 second. Development costs for managing the systems have reduced by 20% while time to market for deploying new applications has been reduced by 25%. After eliminating the complex reconciliation process, Comcast has reduced technology operating expenses (hardware and software), reduced customer care call loads, and reduced development and maintenance costs – all totaling in excess of $1,000,000 per year.
Building a Better Foundation for Success: Cisco on Cisco
Cisco’s own Smart Web Technology Group was having difficulties accessing all of the data they needed with Denodo Data Virtualization. Too much time was spent trying to get access to each and every data source. The solution was completely inefficient as each team had to be retrained and unlearn what way they had been doing things and relearn a new way that was specific to that team.
As the team moved over to Cisco Data Virtualization they found a lot of the things that were problematic in Denodo were much easier. The biggest challenge, improving time to market, was done easily with Cisco Data Virtualization. Projects can now get done in a day or afternoon, compared to next month or next quarter with Denodo. And as security is key for our customer data, with several layers of security controls, certain teams can have more access while restricting data source access to other groups, as needed.
Learn more from Bill Schongar and Susann Ebberts of the Smart Web Technology Group as they share their experience replacing Denodo with Cisco Data Virtualization:
https://www.youtube.com/watch?v=GGPIVgHDWkM&index=33&list=PLFT-9JpKjRTDSyR4jbCVS5e94fzzhIzWz
Moving Forward
Each day we are working to develop solutions that respond to our customers’ most critical needs. I couldn’t be more proud of the team that has built our data virtualization product and look forward to delivering our future roadmap. Stay tuned for updates as Cisco continues to pave the way for the future of data virtualization!
What are your favorite operational use cases from Cisco Data Virtualization? Comment below.
Join the Conversation
Follow @KevinOttCisco, @CiscoDataVirt, and @CiscoAnalytics.
Learn More from My Colleagues
Check out the blogs of Mala Anand, Mike Flannagan, Jim McDonnell, James Jamison, and Bob Eve to learn more.


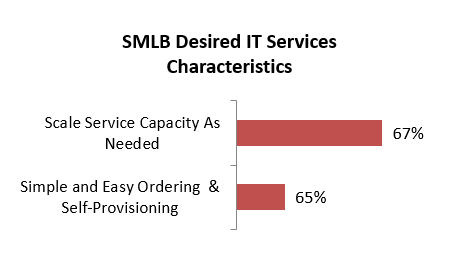 One of the immediate opportunities for service providers to deliver on the promise of IT services simplicity and flexibility is Cloud VPN. Cloud VPN makes ordering and signup easy on a portal. The service is activated, provisioned and scaled dynamically. This simplicity will open up a new, untapped market for service providers. The study shows that SPs will see a $7.6B Cloud VPN opportunity globally. We have summarized these key findings and your opportunity in
One of the immediate opportunities for service providers to deliver on the promise of IT services simplicity and flexibility is Cloud VPN. Cloud VPN makes ordering and signup easy on a portal. The service is activated, provisioned and scaled dynamically. This simplicity will open up a new, untapped market for service providers. The study shows that SPs will see a $7.6B Cloud VPN opportunity globally. We have summarized these key findings and your opportunity in 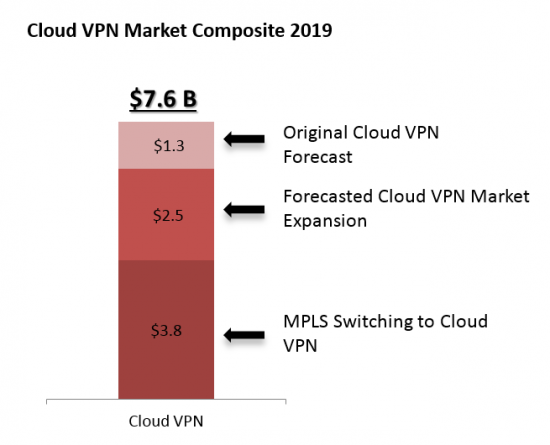
 Watch
Watch  To meet the demand for business agility, companies are turning to virtual workstations to increase flexibility for their workforce and accelerate business transformation. This is happening across a wide range of industries. Take the
To meet the demand for business agility, companies are turning to virtual workstations to increase flexibility for their workforce and accelerate business transformation. This is happening across a wide range of industries. Take the  Cisco offers a complete infrastructure solution that provides an exceptional graphics experience for delivering virtual applications and desktops. It is based
Cisco offers a complete infrastructure solution that provides an exceptional graphics experience for delivering virtual applications and desktops. It is based
 10 Million is a big number. How big? To put it in perspective, 10 million minutes is a bit over 19 years…Which is about 15 years longer than it took the
10 Million is a big number. How big? To put it in perspective, 10 million minutes is a bit over 19 years…Which is about 15 years longer than it took the