Developer
DevNet Sandbox: Building the Future of Developer Experiences
Starting August 1st, the Cisco DevNet Sandbox will go offline for a complete rebuild. We're creating a modern experience focused on AI, automation, and programmability. Stay tuned for our next-gen platform for the developer community.
Explore Enterprise Networking Automation at Cisco Live US 2026
Explore top networking automation sessions, labs, and workshops at Cisco Live US 2026. From IOS XE and AI-ready infra to ACR and telemetry, this guide helps you master the tools driving the future of network management. Plan your schedule now!
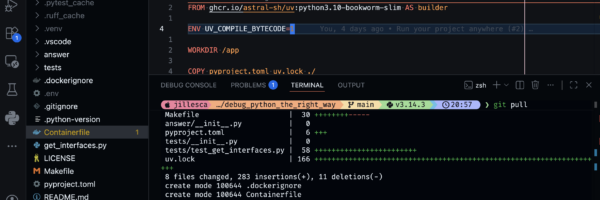
Month of Developer Productivity: Build and Forget
Discover developer productivity tools: set up VS Code, automate code quality, debug Python effectively, and ship reproducible builds with uv and Docker.
Try Cisco AI Defense Explorer Edition in this hands-on lab
A practical DevNet lab for connecting a public OpenAI-compatible target to Cisco AI Defense Explorer, running a Quick Scan, and reviewing AI red team findings.
Recap Scaling the Future: Reddit AMA on Network Automation at Scale
Discover the top insights from our recent Reddit AMA with Cisco experts on tackling real-world network automation challenges at scale. Learn best practices for multi-system integration, deterministic execution, and using AI as a reasoning layer.
Product sprints for developer-oriented portals and content
Use developer portal analytics and feedback to drive product decisions. Learn key indicators and see how Cisco DevNet improves developer experiences. Stop guessing, start measuring what matters for your API and documentation users.
Scaling the Future: Join Our Reddit AMA on Network Automation at Scale
Join Cisco's leading experts for a Reddit AMA on April 20, 2026, to discuss network automation at scale. Bring your toughest questions about network management, architectural scaling, and the future of automation fabrics.
Celebrating the Month of Meraki
Catch up on the Cisco Meraki Month of Meraki series. Explore OAuth, Splunk, Cisco Spaces, ThousandEyes, and AI-driven APIs to build smarter, automated, and observable networks.
Don’t deploy OpenClaw without securing it – Try this opensource solution and hands-on lab
OpenClaw enables powerful AI agent workflows—but introduces new security risks. Learn why securing tools, MCP servers, and agent-generated code is critical, and how DefenseClaw helps protect your environment.