Companies that don’t comply with the new GDPR rules could be hit with a huge bill.
Security breaches that lead to customer data being compromised are an increasing concern for service providers.
Last year, Yahoo announced two serious data breaches, one of which led to hackers accessing the personal data of over 1 billion customers.
Other recent attacks, like those on the UK service provider Three, and the professional social network LinkedIn, also breached the personal data of millions of customers.
The danger is clear – and as the internet of things grows, there will be ever more opportunities for hackers to access sensitive information.
This is a real worry for any responsible service provider. And there will be an extra challenge from May 2018, when the EU General Data Protection Regulation (GDPR) comes into effect.
The GDPR will affect every organisation that processes the personal information of European Union residents. So all service providers that work in the EU will need to think about new rights, duties and obligations regarding people’s personal data.
For example, the definition of personal data will be broader, and companies will be obliged to notify the relevant authorities within 72 hours when they have suffered a breach.
It’s worth noting that the UK will still be in the EU when the GDPR comes into force. And in any case, UK service providers may well still be processing the personal data of European citizens, especially since the legislation’s definition of personal data will include IP addresses and many cookies.
Organisations that don’t comply can be fined up to 4% of their annual turnover, or 20 million Euros – whichever is larger. So it makes sense to be prepared.
A comprehensive approach
The best way for businesses to be sure they are complying with GDPR is to take a comprehensive, holistic approach to data protection.
You should review all your policies and procedures, on everything from how data is protected to what your response would be in the event of a breach. And make sure your team is on board with them.
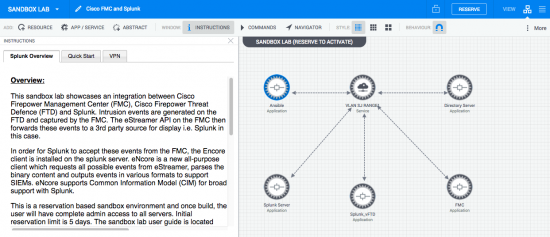
It’s equally important to focus on the technical side, making sure that your security solutions are up to the task and are working together effectively.
Making things simpler
Maintaining strong data security is a real challenge, and it’s getting harder all the time. Our Annual Cyber Security report this year found that two-thirds of companies (65%) are using more than five security products, and some are using more than 50.
With this level of complexity, it’s no surprise that 44% of security alerts aren’t investigated.
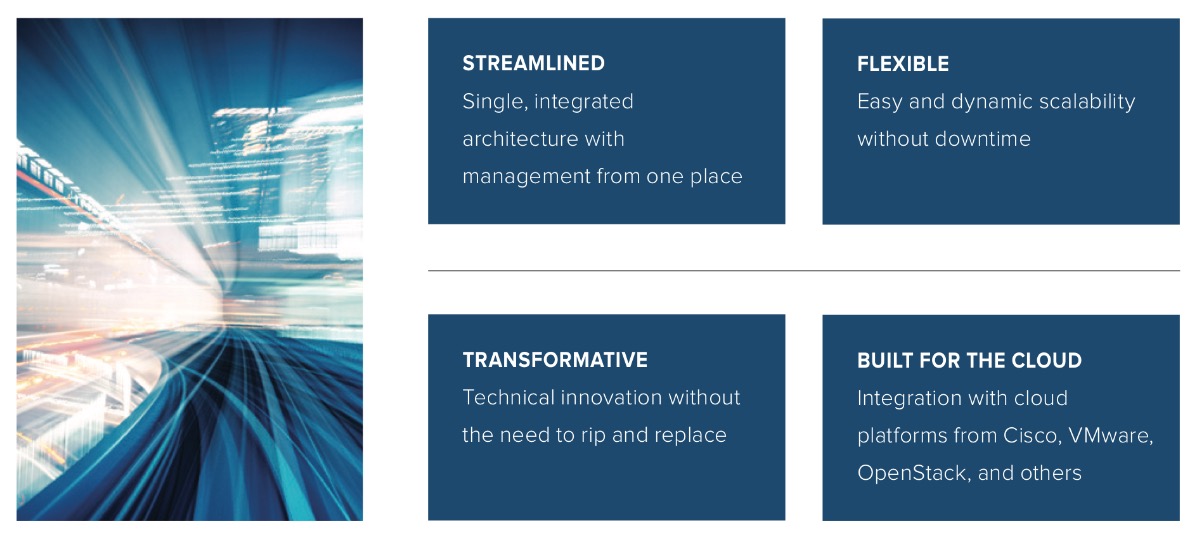
Cisco’s threat-centric security technology is designed to make things simpler, so it’s easier for you to fight back against hackers. We can bring together our comprehensive suite of best-of-breed solutions into an integrated architecture to deliver effective security that’s simple, open and automated.
Our security provides greater visibility, actionable insight through analytics, and enforcement. And network and context information is automated through shared telemetry and cloud-processing.
This unique approach enables us to keep on reducing the time it takes us to detect threats. As set out in our 2017 Annual Cybersecurity Report, we lowered the median time to detection (TTD) to 14 hours for the period from November 2015 to October 2016.
And for the second part of that period (between May and October), the median TTD was just nine hours (compared to the industry average of 100 days).
Reducing the TTD gives hackers even less time to work in. And it means you can respond to threats in a way that others simply can’t match.
Data security: a challenge and an opportunity
The GDPR presents a challenge. But it’s also a great opportunity for service providers to adopt a smart approach to data security.
Cisco can support you in updating your technology and architecture to make sure you’re less likely to experience a damaging data breach. And if you do, we’ll help you identify it quickly and react effectively.
We put trust at the heart of our products and services. That’s why we consider security at every stage of their design, production and implementation.
Security involves thinking defensively, to prevent harm to your data and assets. But for smart service providers, it’s also a huge opportunity to grow your reputation and your business.
Find out more about how Cisco Service Provider Security Solutions can help you get ready for GDPR.