Security in not simple and not all companies are the same. Different business needs, inter-connected applications, and compliance regulations are coupled with increasing demands of the network by employees, partners, customers and most recently, devices; the fragmentation of the attack surface is maddeningly complex, as thieves become better organized to take advantage of it.
However, when viewing the problem in its entirety, patterns begin to emerge. Regardless of what industry you work for, certain types of business methods at the branch are likely to be employed and consequently, exploited. I joke, for example, if security concerns around email keep growing, maybe it is time to stop using that form of communication. If the Internet connection in the branch is too dangerous to secure, then don’t use it. If you don’t want malware on your network; don’t have one.
Obviously, most businesses of today require those types of services. SAFE uses common business practices that require common security capabilities to provide a reference for end to end security.
The SAFE model provides a reference architecture that you can use to customize for your company’s specific business needs. The model uses several viewpoints to provide the right level of clarity for all audiences. The SAFE model includes
- An 80/20 rule for common branch business use cases
- Security capabilities mapped to the common threats within these use cases
- Reference branch architectures that logically arrange the security capabilities for simplicity
- Suggested designs that use the reference architectures for common branch deployment scenarios and solutions.
- A method to customize the model for specific company security needs.
Securing the Branch starts with the Business
SAFE uses common business flows that expose risk to a company. Each flow has security capabilities that relate to those threats. By using the SAFE reference architecture, you can understand how to design for the majority of your business needs and let you focus on what is unique to your business. Let’s look deeper at the branch business and how that affects its architecture and design.
The Secure Branch business flows are:
INTERNAL flows are any business need that company employees have on the network.
THIRD PARTY flows are network connections to vendors, service providers or companies external to your company.
CUSTOMER flows are a variety of network services such as guess Internet, website portals and protected customer information.
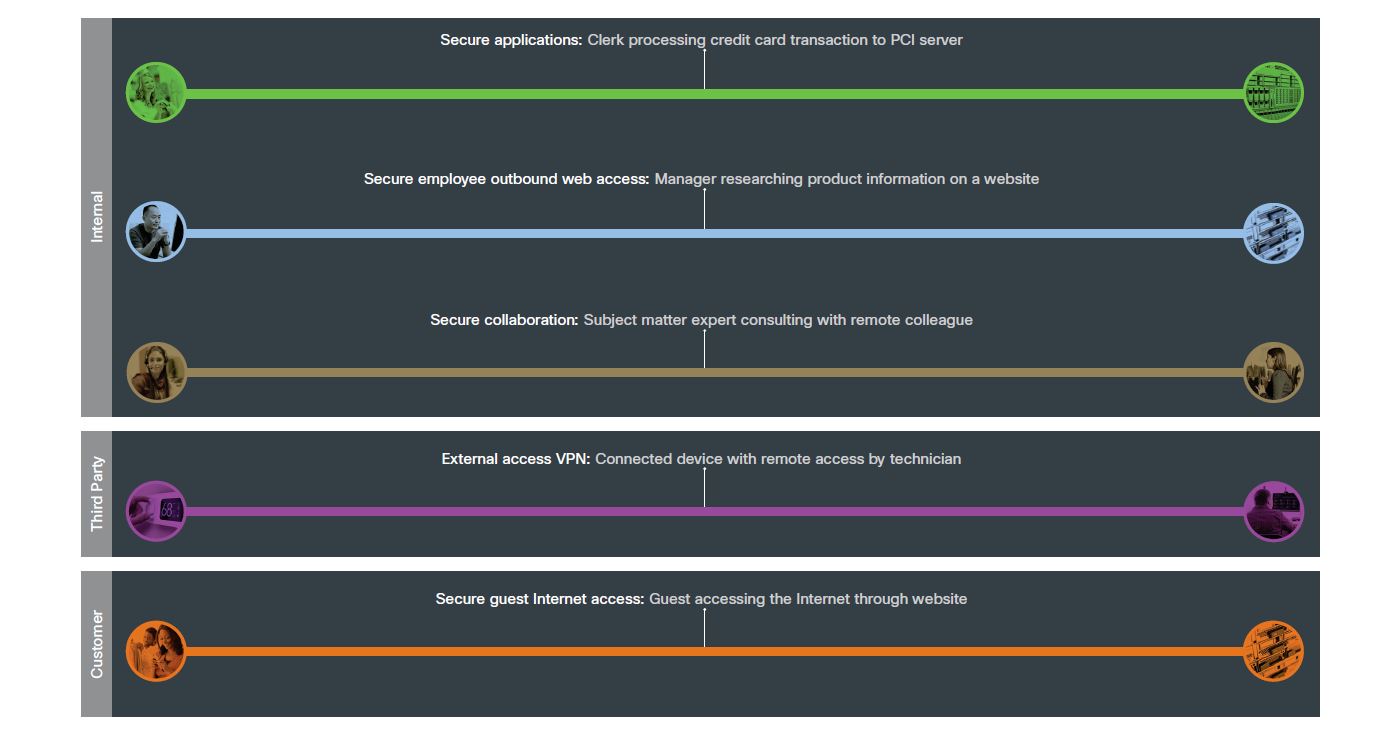
Each of these types of flows have common uses in the branch. To simplify the common branch business risks, we color coded each use case and created an example that can be used for the architecture and design of a secure branch.
These flows have different attack surfaces that need security capabilities to protect them.
Secure Branch Architecture
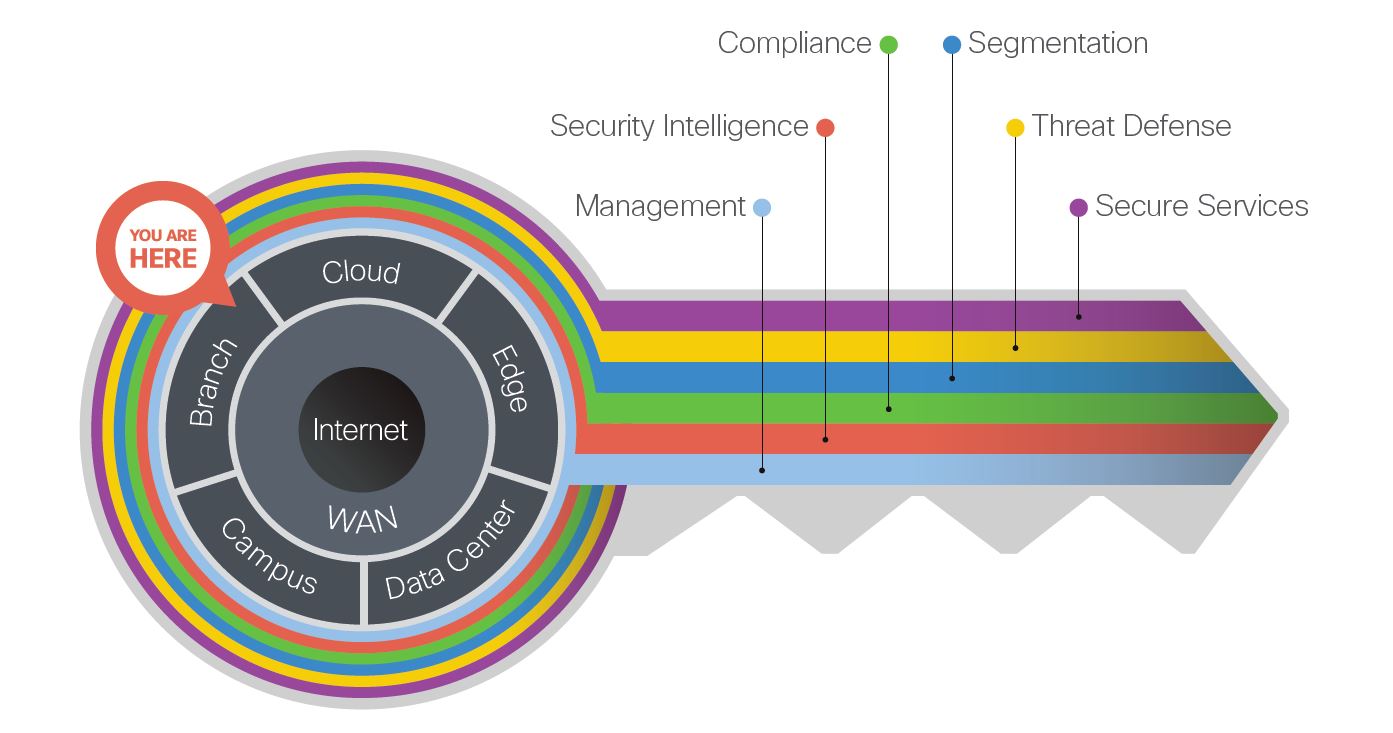
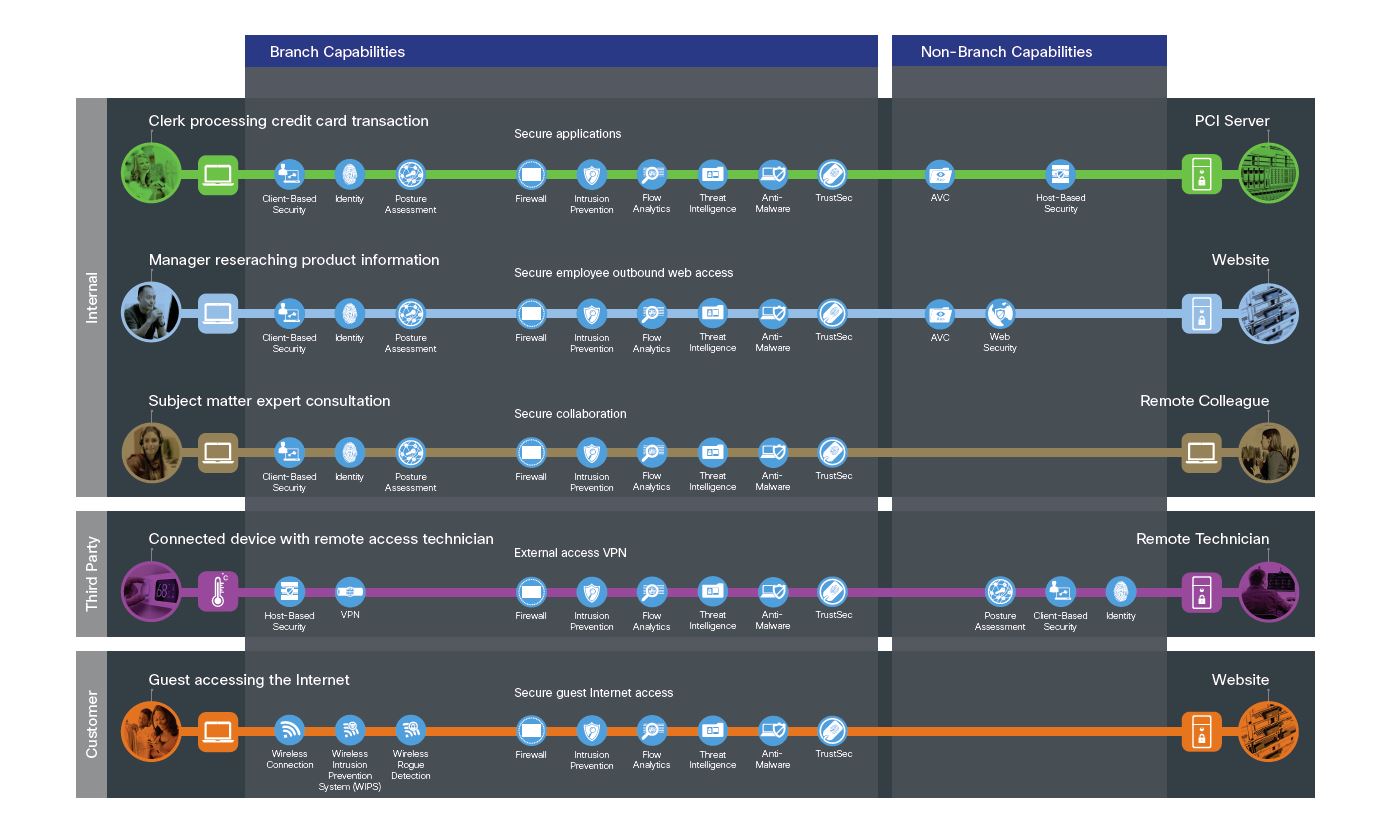
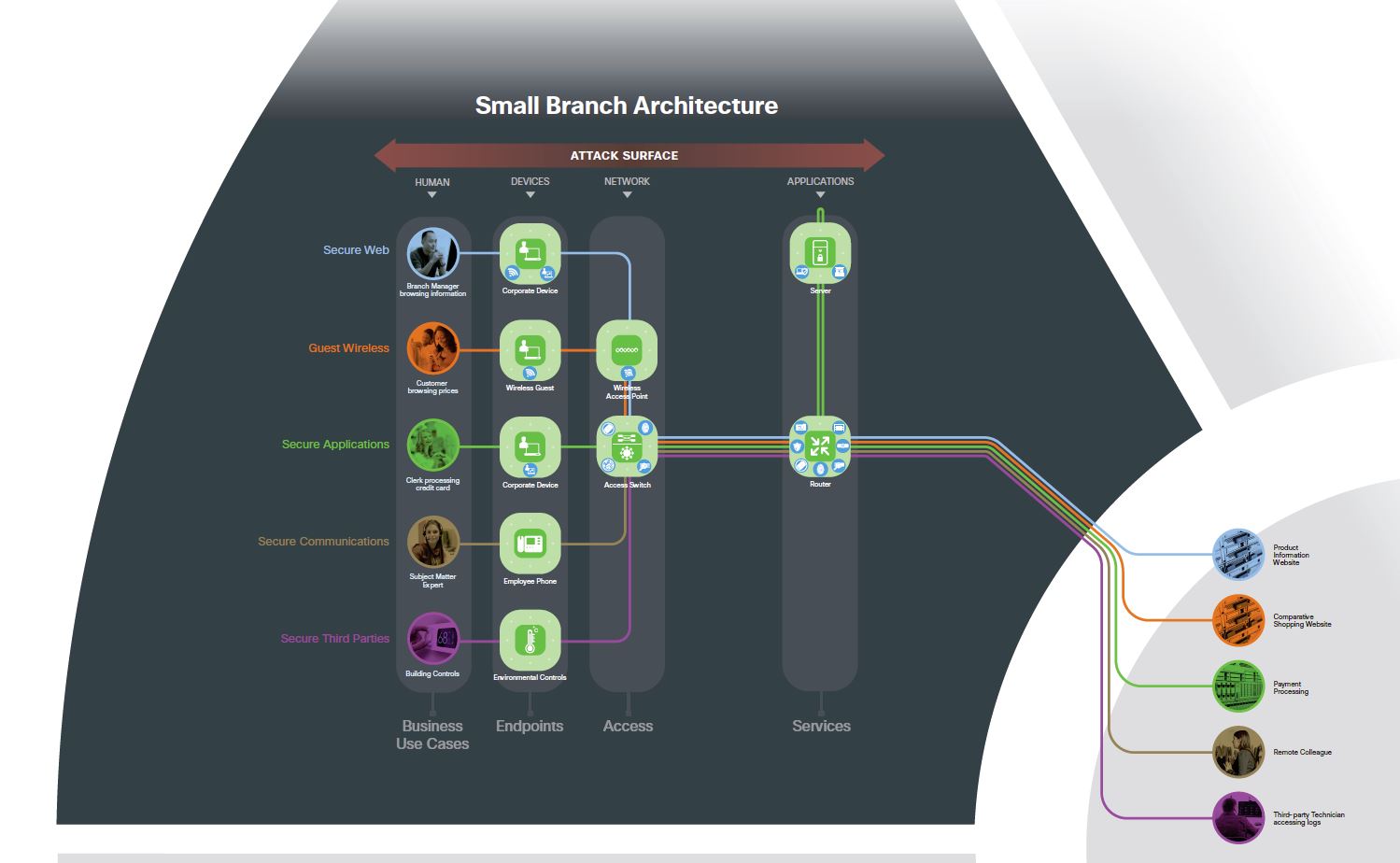
Each of these flows go across many parts of the organization. In order to secure them, we must look at each flow and what Places in the Network (PINS) they connect to. SAFE provides guidance on each PIN and the common threats that exist there by using these flows to illustrate and simplify security. Here is an example of a small branch PIN using the business flows and security capabilities from above.
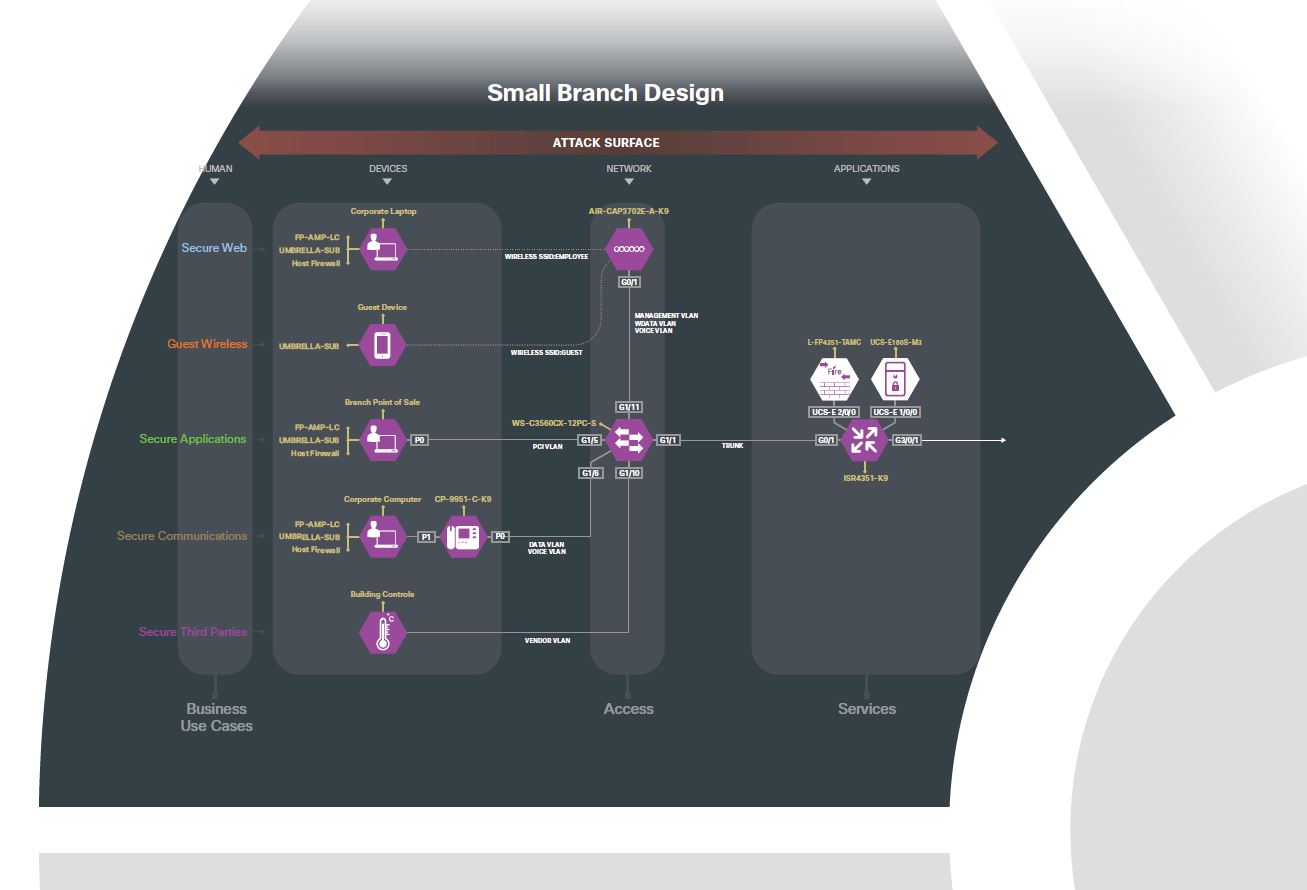
This business flow architecture ensures that each line of business has the appropriate controls. This allows a design to be created by selecting the vendor that can provide the product that has the requisite security capabilities. Here is an example design of that same small branch but with specific hardware chosen to meet the needs of securing the business.
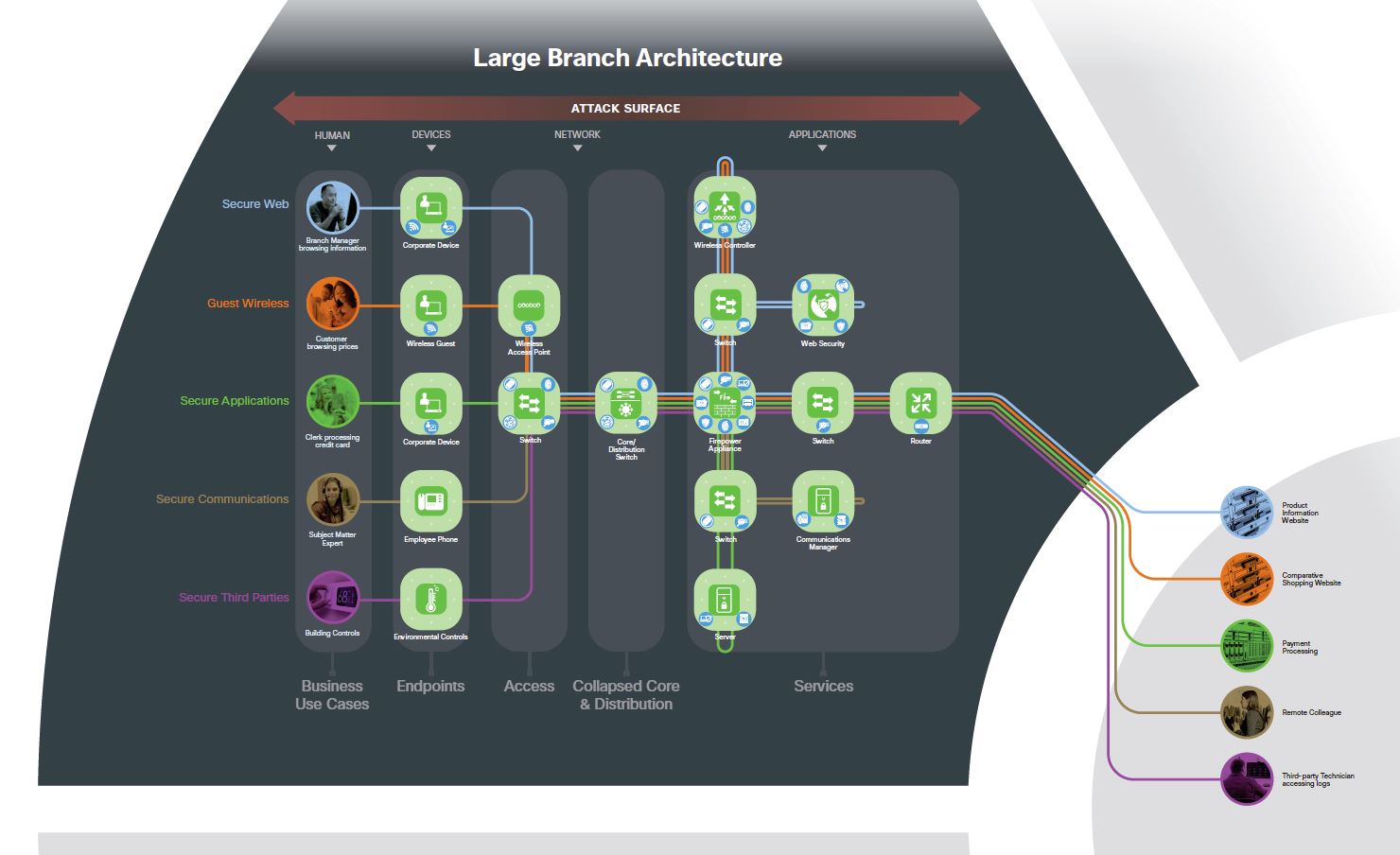
This same mapping of business flows with corresponding security capabilities can be reused for different designs. For example, in contrast to the small branch, perhaps you need a more redundant and available network for your business. In this case, the large branch might be a better fit. It is important to note the same business flows and risks are being secured the same way. Here is an example of the large branch architecture.
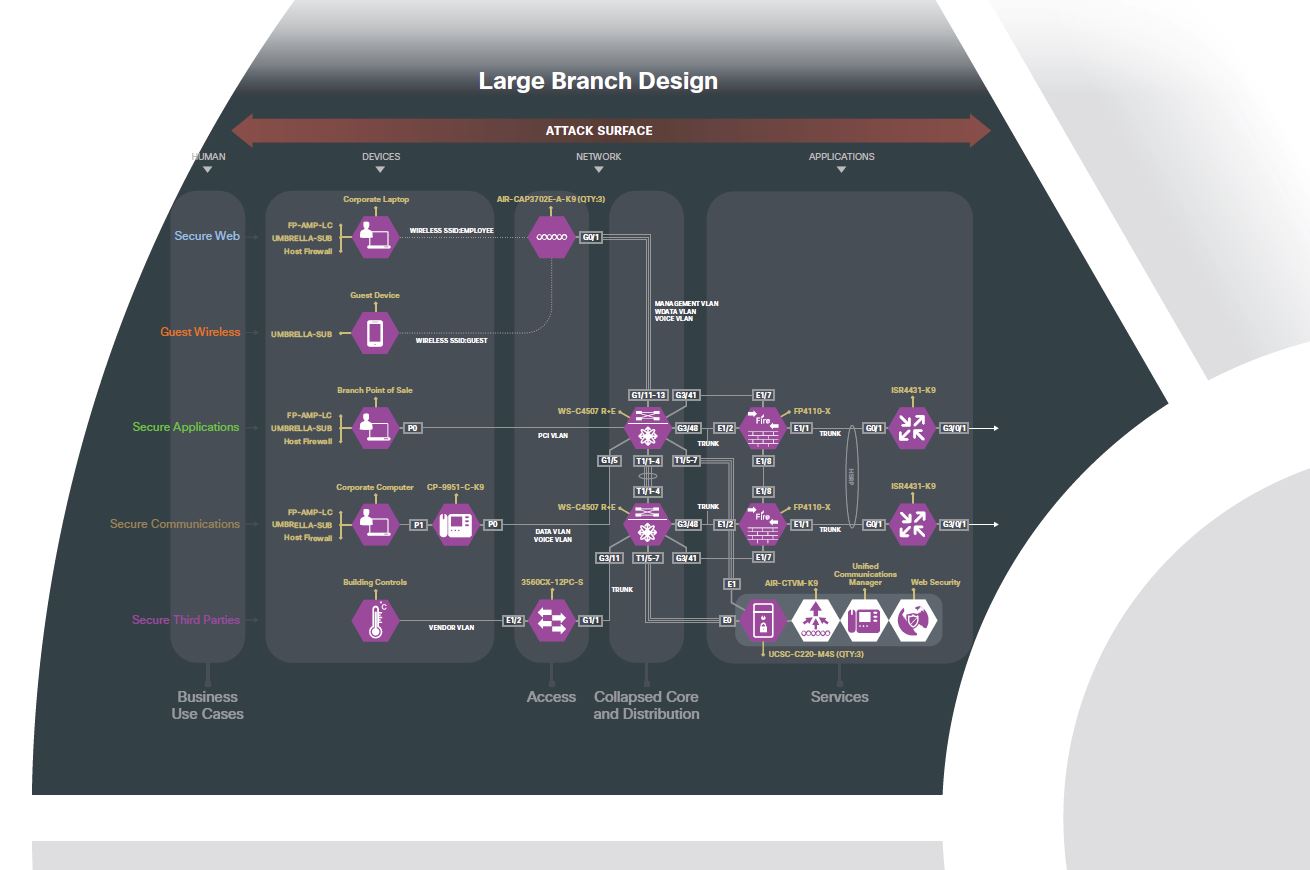
This large branch uses the same controls but has more local compute services and redundancy. The vendor selection and configurations to make this architecture into a design is illustrated by the following large branch design.
By using the SAFE reference security architecture, you can get best practice security guidance that maps to today’s security challenges. This allows you to tailor it to your specific business needs or have your Cisco account representative schedule a SAFE workshop for your company.
Visit www.cisco.com/go/SAFE to download the new SAFE Secure Branch Architecture guide and other SAFE tools.