Today’s mobile devices and applications not only demand tremendous amounts of data but the user experience must be superior regardless of traffic type, network type or user location. Network administrators desire to deliver this elevated user and application experience BUT not at the cost of added complexity and operational challenges.
Cisco is always ahead of the curve when providing all these capabilities without an exponential increase in cost—and we have it way before the competition. This trend continues with Cisco Digital Network Architecture (DNA). This solution offers the scalability, resiliency and ease of operation without compromising the security.
Configuration and operation of end-to-end Quality of Service (QoS) across the enterprise networks has always been a challenge. And with the growing number of apps and services, its becoming harder and harder to ensure high level quality of service across the network. Today’s massive enterprise networks are a combination of different type of devices like various tiered wired switches, wireless controllers, access points and routers. Moreover, these devices are often a combination of various operating systems and models with drastically different priority queuing structure.
It becomes the administrator’s headache to implement a consistent and reliable QoS across an end-to-end network. Administrators have to know all the devices, operating systems and queuing across platforms and go through thousands of pages of deployment and best practices guides to even get started. This often adds lot operational cost and delays in the deployment and upgrades.
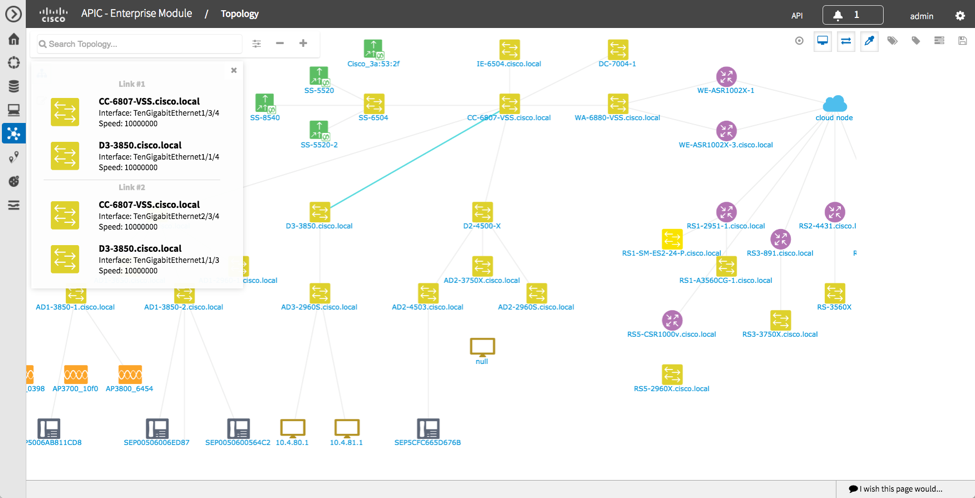
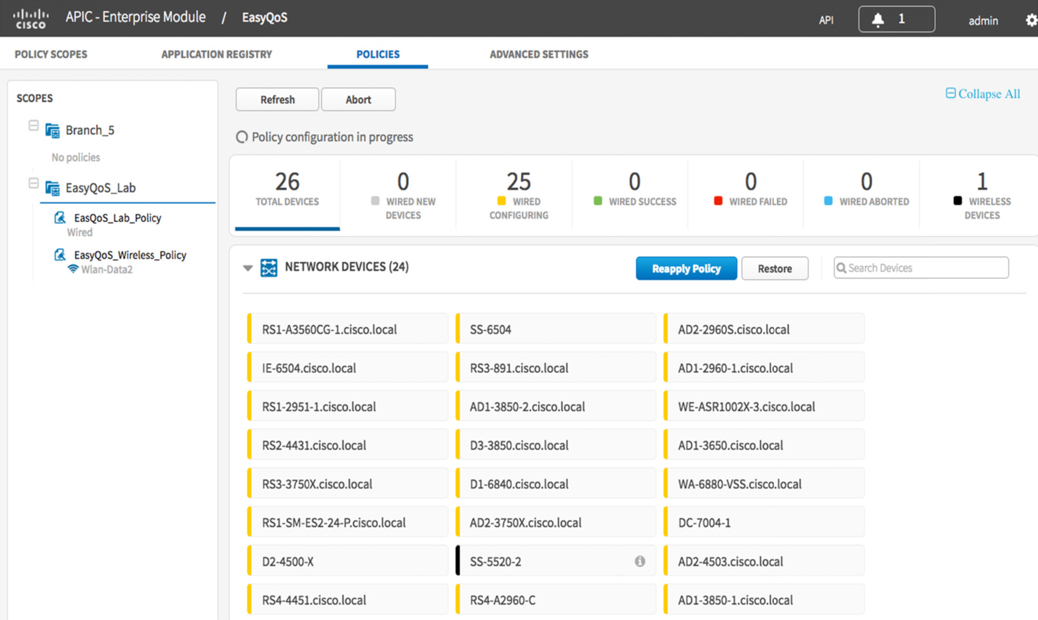
Recently Miercom, an independent testing lab, released a report that evaluated the Cisco EasyQoS app which runs on the Cisco’s APIC-EM controller platform. This app simplifies these challenges by abstracting all the complexities involved in the QoS operations. It offers the administrator a simple-to-use dashboard to configure entire networks with just a click of the button. The EasyQoS app incorporates all of the Cisco best practices and Cisco Validated Designs (CVDs) to create the QoS policies based on administrator’s requirement and then translate those policies into configuration commands and programs every device in the network including switches, wireless and routers.
Miercom validated this powerful but extremely simple-to-use app against HPE-Aruba’s VAN SDN controller’s Network Optimizer app. HPE-Aruba’s entry claims to have similar functions, but it doesn’t.
In this report Miercom found HPE-Aruba’s Network Optimizer App is limited to only couple of real world applications, such as Skype for Business. This runs counter to Cisco EasyQoS which is optimized for over 1300 built-in business and consumer apps. Cisco EasyQoS also offers options to configure your own custom apps. Even if we consider prioritizing the Skype for Business app, HPE uses a VAN controller to ONLY configure edge switches. For applying similar policies on the wireless, an administrator has to re-create the policies on Aruba Mobility Controller and push it down to wireless access points. So essentially HPE-Aruba requires two separate controllers to apply QoS policies across wired (VAN) and wireless (Mobility Controller).
HPE-Aruba also cannot automate this process for the rest of the network devices, such as: aggregation switches, core switches, routers and WAN. Also, HPE-Aruba doesn’t provide support for rest of the critical applications like Salesforce, Oracle, Exchange and Jabber.
Cisco is the only vendor in the market who is offering this end-to-end QoS functionally which converts business intent into the actual network configuration without exposing the complexities involved.
Bottom-line: An independent testing lab has proven that Cisco APIC-EM offers real world SDN capabilities by offering apps for Day-0, Day-1 and Day-2 network operations. EasyQoS enables end-to-end orchestration of QoS in the Enterprise network making QoS policy simple and easy to deploy with an operator expressing business relevance for applications and the controller doing the rest under the hood.
Please download the complete Miercom report here.
 Federal agencies can breathe a sigh of relief that — so far at least — the exploit hasn’t hit them. But don’t make it too loud, because there is still time. And even if WannaCry leaves the government unharmed, the next major attack might not. The Federal Government is a frequent target of cyberattacks and attempted intrusions, and a few high-profile cases in recent years drive home the point that agencies need security as robust as any private company.
Federal agencies can breathe a sigh of relief that — so far at least — the exploit hasn’t hit them. But don’t make it too loud, because there is still time. And even if WannaCry leaves the government unharmed, the next major attack might not. The Federal Government is a frequent target of cyberattacks and attempted intrusions, and a few high-profile cases in recent years drive home the point that agencies need security as robust as any private company. Aurelia Takacs, Brussels site lead & Global Delivery Partner Manager
Aurelia Takacs, Brussels site lead & Global Delivery Partner Manager
 Louise Mills, Bedfont Lakes, UK, lead & Associate Virtual Sales Rep
Louise Mills, Bedfont Lakes, UK, lead & Associate Virtual Sales Rep
 Bayan Barry, Saudi Arabia site lead & Regional Customer Service Advisor, EMEAR Middle East
Bayan Barry, Saudi Arabia site lead & Regional Customer Service Advisor, EMEAR Middle East
 Shraddha Chaplot, San Jose, CA site lead & Systems Engineer, Cisco Customer Experience Center
Shraddha Chaplot, San Jose, CA site lead & Systems Engineer, Cisco Customer Experience Center







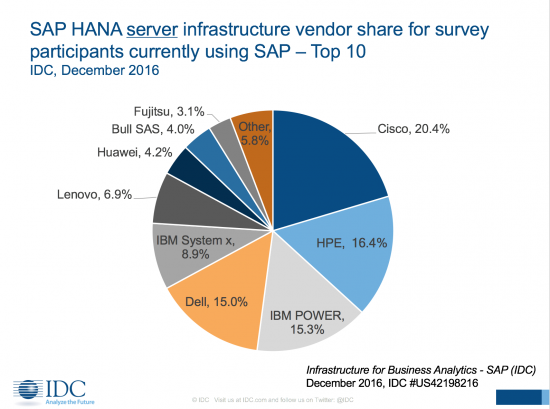

 Does this innovation make a difference for our customers in the real world? In a blind study last year of SAP customers running on the Cisco UCS server platform, IDC found Cisco customers averaged
Does this innovation make a difference for our customers in the real world? In a blind study last year of SAP customers running on the Cisco UCS server platform, IDC found Cisco customers averaged 