Today’s news of the cyberattack affecting healthcare organizations—including the National Health Service (NHS)—in the UK, is sobering. Sources are reporting that the ransomware attack has “crippled the health system’s ability to treat patients.” Thousands of non-emergency appointments have been canceled, and ambulances have been diverted to other facilities, leading the NHS to declare the attack a “major incident.”
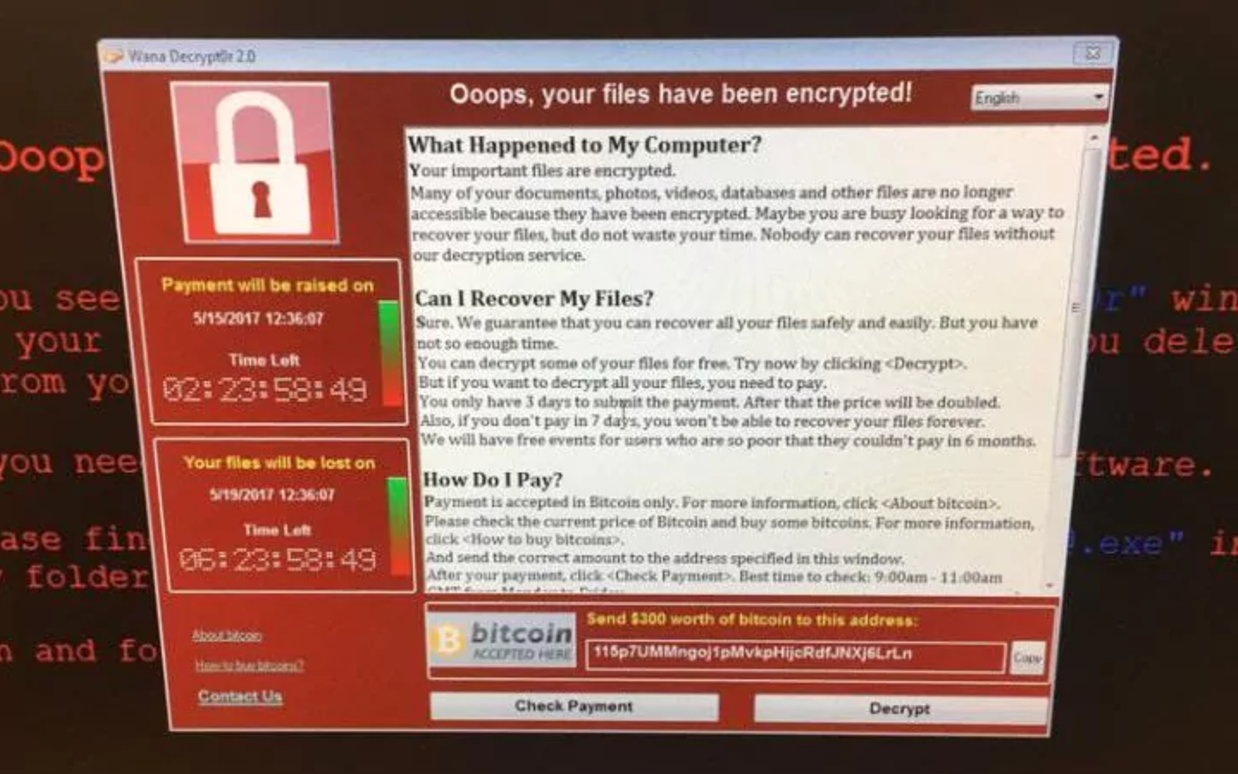
NHS employees attempting to log on to computers Friday were met with a pop-up message stating, “Oops, your files have been encrypted!” The hackers are demanding 415,000 pounds ($534,146) before May 19 or they claim they will delete the files.
The attack later spread to dozens of other countries and all types of businesses, according to the New York Times.
Ransomware isn’t a new phenomenon; it’s been around since about 2005. However, hackers themselves have evolved significantly. The “hacker economy” – estimated to be worth about $1 trillion – is more advanced than you might think. Today, cybercrime is organized crime. New methods of digital trickery are introduced almost daily, many that would fool even the most skeptical user. The ransomware attack on the NHS Friday was reported to be a particularly dangerous variant called the Wanna Decryptor.
Reports indicate that the malware exploited a vulnerability in Microsoft systems and may have links to the National Security Agency in the US. Microsoft created a patch for the vulnerability back in March, but hackers took advantage of the fact that “soft targets” like hospitals hadn’t implemented it yet.
“In healthcare and other sectors we tend to be very slow to address these vulnerabilities,” says Lee Kim, the director of privacy and security at the Healthcare Information and Management Systems Society (HIMSS). “But whoever is behind this is clearly extremely serious.”
For an in depth, technical analysis of the attacks, read the blog by Talos, Cisco’s industry-leading threat intelligence team.
Staying informed of new threats and attacks is a daunting task—but a serious one, especially where patients are involved. Interested in implementing a plan that protects your patients’ well-being? Read our new white paper about cybersecurity strategies for healthcare organizations.






While the solution to this vulnerability is to patch against the EternalBlue/MS17-010/SMB vulnerability and exploit – (a patch which has been available for 60 days now), Cisco AMP customers are protected against the attack. While Cisco Umbrella (OpenDNS) will stop key requests to encrypt files (provided that TOR servers are blocked – which they should be) it won’t stop the spread of malware laterally across the network without AMP or other protective measure. Of course every Windows XP machine (for which there is no patch) would still be infected but wouldn’t encrypt while protected by Umbrella.
https://blogs.technet.microsoft.com/msrc/2017/05/12/customer-guidance-for-wannacrypt-attacks/
Organizations should ensure that devices running Windows are fully patched and deployed in accordance with best practices. Additionally, organizations should have SMB ports (139, 445) blocked from all externally accessible hosts.
For more technical details and an understanding of how this attack works please read the Talos blog at https://blogs.cisco.com/security/talos/wannacry
Microsoft came through with a patch for Windows XP and server 2003 https://blogs.technet.microsoft.com/msrc/2017/05/12/customer-guidance-for-wannacrypt-attacks/
After listening to , ” hackers took advantage of the fact that “soft targets” like hospitals ” , i do not want to know what easy targets are . I always wonder ,
when will people start learning and implementing before waiting for an incident to happen ?
Be advised , it not matter of “if” its just matter of “when” .
And do keep up the good work cisco !
wanna cry makes all cry, but not this time, it can manually hackable ransomware try using decryption tools
I am glad more companies are scrambling to strengthen their overall security posture after this incident which turned out to be not as destructive as it could have been. I am hoping they also found issues in their security coverall they never knew was there all along.