The first day of Cisco Live 2017 Las Vegas is in the books. It was a busy day, to say the least. The morning started with the opening keynote and jumped right into the World of Solutions and tech sessions throughout the day. It was nonstop technology.
I’m not sure the tourists visiting the Mandalay Shark Reef aquarium know quite what’s happening when they find themselves among the badge-wearing masses. It’s a bit like a cattle drive of two-legged critters.
The Keynote
As the arena filled, a DJ warmed up the crowd with some karaoke competition among audience volunteers. Honestly, I don’t know that any of the contestants will be giving up their day jobs anytime soon. I hope not, anyway.
After a loud and bright opening light show, Chuck Robbins took the stage with “If you weren’t awake, you are now!” He delivered the keynote, bringing people up to date on Cisco’s latest announcements. He focused on how much change is coming, and how quickly.
There are 8.4 billion connected things on the Internet today. As soon as 2020, as many as 1 million connections will be made to the Internet every hour. All of these device connections require a more secure, intelligent, and intuitive platform upon which you can build your business. As Robbins describes it, it’s “the new network, powered by intent and informed by context.” Learn more about The Network. Intuitive.
Robbins introduced a guest speaker as the leader of a company with which Cisco has had an important strategic relationship for two years. It’s not often that Apple CEO Tim Cook takes the stage at another company’s event, but he and Robbins sat down to talk about how our companies are working together to improve the enterprise user experience through stronger integration of our products – Cisco Spark and WebEx in particular for the collaboration portfolio.
Also visiting the keynote was David Wichmann, CEO of UnitedHealth Group. He shared how Cisco, Optum, and UnitedHealth are working together to transform healthcare with new patient and provider collaboration with technology including messaging and video with Cisco Spark.
Watch the full keynote on demand.
Check out the Apple + Cisco page to learn more about how we’re working together.
Innovation Talk with Jens Meggers
Jens Meggers, SVP and GM for Cloud Collaboration Technology, started his session talking about how well people communicate — at Saturday gatherings compared to Monday morning at work. Outside of work, our communication is natural and interactive. Inside of work, we use the same tools we’ve been using for two decades (think email), to try to communicate and share ideas. Once upon a time — back when we sat in isolated cubicles and worked in siloed teams — that worked. As Jens put it, “in the past, we were sitting together, but we weren’t really working together.” The way our projects, teams, and workspaces are changing, so our tools should too.

To get to the new work reality, we need to work on three things: environment, structure, and tools. He showed side-by-side screen grabs of Microsoft office in 1995 vs. 2017. What’s changed? Honestly, not much. But the way we work has changed. We’re using tools that haven’t evolved with the way we’ve evolved our work, the way we form teams, and the communities with which we collaborate. Old tools don’t let us work the way we want to work. They don’t let us communicate in natural, interactive ways.
He shared how — and why — we developed Cisco Spark. when people aren’t using video in a meeting, about 60% disengage and do something else. When it takes multiple tools to accomplish a task with others, it takes extra time to hop between those tools. If everything is integrated into one tool with a design that emphasizes an intuitive experience, that saves time and effort. “Cisco Spark allows you to create the superhighway of communications to accelerate decision-making.”
Learn more about the Cisco Spark platform and devices.
Kilts, NotSoMiniFig, and bears – oh my!
There was more than plenty to see throughout the day, from the thousands of products in the 1 million square feet of the World of Solutions area to the fashions of the ever-growing and always popular #KiltedMonday. Making their Cisco Live debut were@NotSoMiniFig and a rather large sloth of Cisco Spark bears (the official answer to “what is a group of bears called?”) In fact, the Cisco Spark bears managed to photobomb quite a few of my pictures during the day and created quite a presence on Twitter.

Tuesday Highlights
So we’re off and running! Bring on Day 2! (OK, with all the walking going on, there’s very little energy for running. And if the legs would even agree to do it, the feet wouldn’t allow it.)

Want videos and other good stuff from the Cisco Live event team? Check out the CLUS Daily Highlights page.
Learn more about the new era of networking from our friends on the enterprise networking team.
https://youtu.be/ZuJjncuptz0





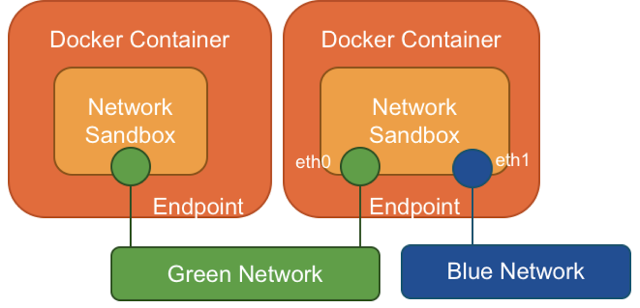
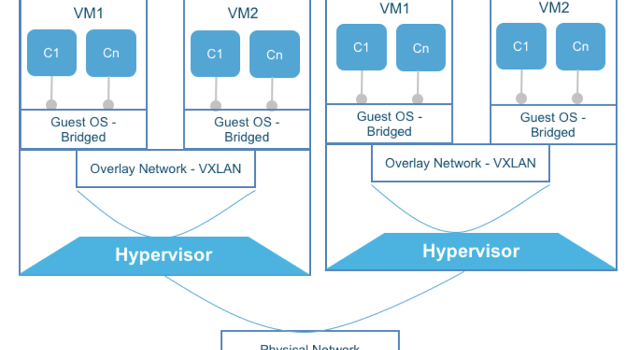 Containers inside VM: many layers of overlay networks
Containers inside VM: many layers of overlay networks






 We like that vote of confidence; Kerravala is no newcomer to watching tech. I remember interviewing him several times years ago, when he was an analyst at The Yankee Group and I was a reporter at
We like that vote of confidence; Kerravala is no newcomer to watching tech. I remember interviewing him several times years ago, when he was an analyst at The Yankee Group and I was a reporter at