In my previous post, we talked about the complexity that Containers can bring to the network and what that means to different roles within an organisation.
We also introduced Contiv in this context and touched on its high-level architecture.
In this post, we aim to get a big more into detail… 🙂
So let’s begin…
Contiv Architecture
Contiv is made of a master node and an agent that runs on every host of your server farm: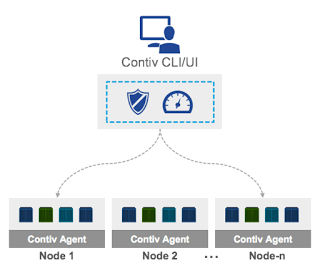
Contiv’s support for clustered deployments
The master node(s) offer tools to manipulate Contiv objects. It is called Netmaster and implements CRUD (create, read, update, delete) operations using a REST interface. It is expected to be used by infra/ops teams and offers RBAC (role based access control).
The host agent (Netplugin) implements cluster-wide network and policy enforcement. It is stateless: very useful in case of a node failure/restart and upgrade.
A command line utility (that is a client of the master’s REST API) is provided: it’s named netctl.
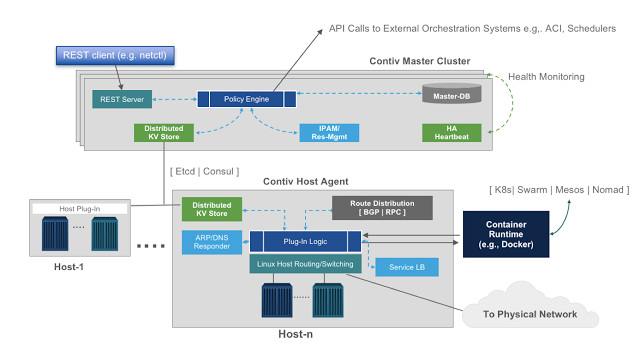
Contiv’s architecture
Examples
Learning Contiv is very easy: from the Contiv website there is a great tutorial that you can download and run locally.
For your convenience, I executed it on my computer and copied some screenshots here, with my comments to explain it step by step.
First, let’s look at normal docker networks (without Contiv) and how you create a new container and connect it to the default network:
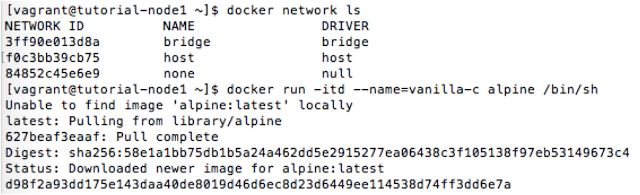
Networks in Docker
You can inspect the virtual bridge (in the linux server) that is managed by Docker: look at the IPAM section of the configuration and its Subnet, then at the vanilla-c container and its ip address.
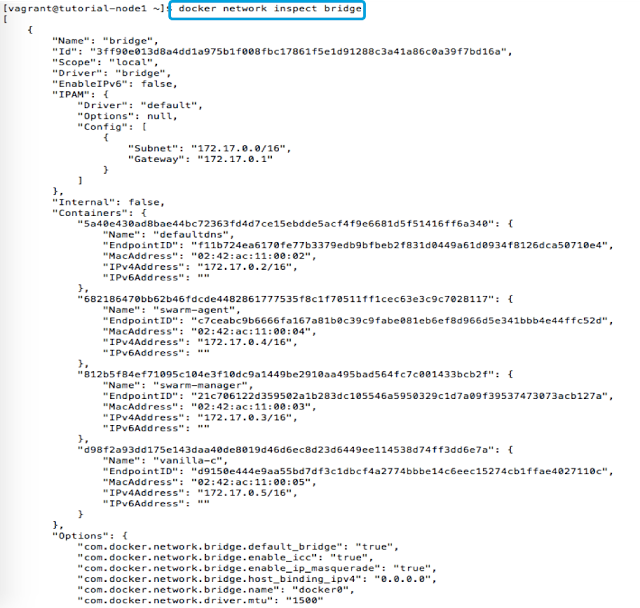
How Docker sees its networks
You can also look at the network config from within the container:
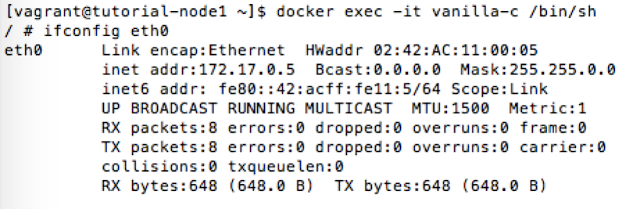
Now we want to create a new network with Contiv, using its netctl command line interface:
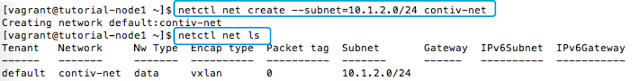
Here you can see how Docker lists and uses a Contiv network:
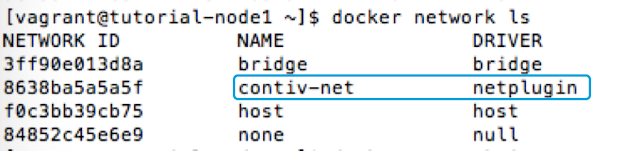
Look at the IPAM section, the name of the Driver, the name of the network and of the tenant:
We now connect a new container to the contiv-net network as it is seen by Docker: the command is identical when you use a network created by Contiv.
![]()
Multi-tenancy
You can create a new Tenant using the netctl tenant create command:
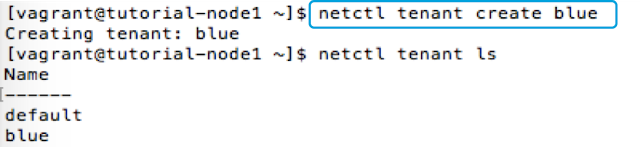
A Tenant will have its own networks, that can overlap other tenants’ network names and even their subnets: in the example below, the two networks are completely isolated and the default tenant and the blue tenant ignore each other – even though the two networks have the same name and use the same subnet.
Everything works as if the other network did not exist (look at the “-t blue” argument in the commands).
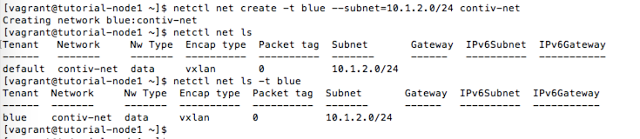
Two different networks, with identical name and subnet
Let’s attach a new container to the contiv-net network in the blue tenant (the tenant name is explicitly used in the command, to specify the tenant’s network):
![]()
All the containers connected to this network will communicate. The network extends all across the cluster and benefits of all the features of the Contiv runtime (see the website for a complete description).
The policy model: working with Groups
Contiv provides a way to apply isolation policies among containers groups (regardless of the tenants, eventually within the tenants). To do that we create a simple policy called db-policy, then we associate the policy to a group (db-group, that will contain all the containers that need to be treated the same) and add some rules to the policy to define which ports are allowed.
 Creating a policy in Contiv
Creating a policy in Contiv
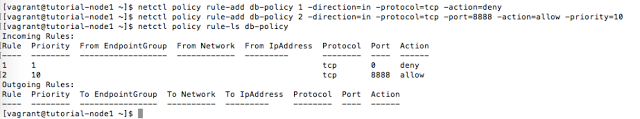 Adding rules to a policy
Adding rules to a policy
Finally, we associate the policy with a group (a group is an arbitrary collection of containers, e.g. a tier for a microservice) and then run some containers that belong to db-group:
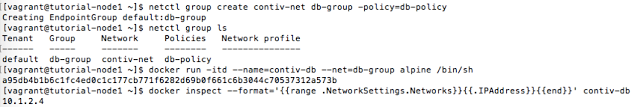 Creating a group
Creating a group
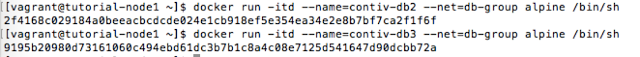
The policy named db-policy (defining, in this case, what ports are open and closed) is now applied to all the 3 containers: managing many end points as a single object makes it easy and fast, just think about auto-scaling (especially when integrated with Swarm, Kubernetes, etc.).
The tutorial shows many other interesting features in Contiv, but I don’t want to make this post too long 🙂
Please reach out to me if you have any questions.
Interesting Resources
- Contiv download – github.com/contiv/install/releases
- Contiv documentation – contiv.github.io
- Contiv tutorial – http://contiv.github.io/documents/tutorials/index.html
- Contiv Blogs – blogs.cisco.com/tag/contiv
- Recorded demo – https://www.youtube.com/watch?v=55s4wAVbTM4
- Cisco DevNet community – https://developer.cisco.com/site/contiv/videos/index.gsp
- Join Contiv Slack to get support – contiv.herokuapp.com
- Contiv on Docker Store – https://store.docker.com/plugins/803eecee-0780-401a-a454-e9523ccf86b3?tab=description
- My Contiv session at Codemotion Rome 2017:
- Video on youtube: https://www.youtube.com/watch?v=Ngjff3pu93w
- Slides: https://t.co/v3D18AoSBk
- Great performances with Contiv – http://contiv.github.io/articles/2016/03/06/scaling-microservices.html



