Legacy networks are at risk. Faced with increased security risks, an explosive growth in IoT, mobility & access issues, and new cloud-based consumption models, these old networks must evolve; evolve to the new era of intuitive networking.
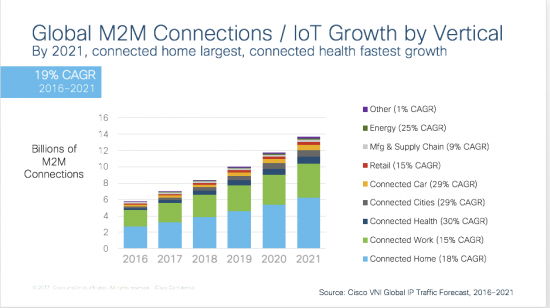
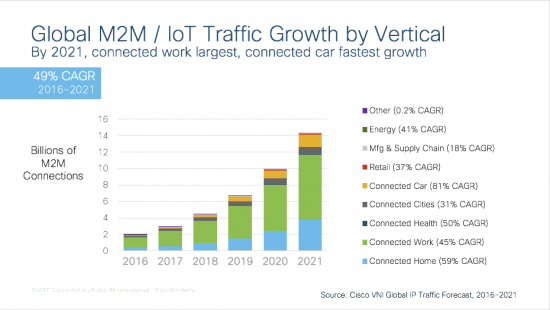
The new era is introducing a multitude of new devices that range from mobile devices and video endpoints that need high capacity and scale, to low power sensors with varying latency and bandwidth needs. In the new era, driven by advancements in IoT, various IT and Operational Technology (OT) services are converging. In the new era mobility is taken for granted, and network boundaries don’t exist. In the new era, the threat landscape has expanded with an ever-growing attack surface. In the new era, users expect robust connectivity and a consistent, secure experience for accessing applications in the public and private cloud. And in the new era users, devices and services seamlessly interconnect to enable the consumption of services across the network.
Digitization is a boardroom conversation for all leading organizations. Whether it is a retailer trying to transform in-store experiences, or a hospital that needs security and privacy for its patients, or an office creating an engaging workspace for its employees, a digital ready network is foundational. More than ever before, organizations need the network to aid and abet innovation, and not stall and hinder progress. The network needs to powered by intent and informed by context, continuously learning and adapting. It needs to evolve into an agile platform that drives innovation across various business processes from enabling access, and ensuring policy and control, to allowing visibility and assurance, the network should simply work. To that end, the following network functions become critical:
Automate Everything, from Edge to the Cloud
Increased IT agility and speed foresees the need for automation. Automation is needed to Design, Build and Run the network. From image and configuration management and user and device onboarding, to enabling operations that optimize application performance and end user experience, automation is fundamental for faster delivery of services. APIs, as the new global currency for networking are a necessity in the new era. The use of APIs will drive advanced automation on programmable, intent based infrastructure, such that intelligent network functions don’t remain daunting and cryptic, but become intuitive, the new normal.
Secure Everything, Based on Intent
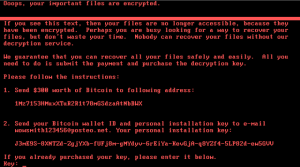
Security breaches are a huge financial risk. In the new era, the threat landscape has increased, and perimeter security is simply not sufficient. With about 50% of the network traffic now encrypted cyber-attacks are also encrypted. To protect, and to effectively detect and respond to threats, security must be integrated into the network. Trusted hardware, that is first hitless itself, and which enables secure access and sophisticated threat detection – even for encrypted traffic – is critical. Beyond that, a network powered by intent, expressed as a policy, will automatically segment users, things, applications, and data to secure assets and restrict threat proliferation.
Drive Outcomes Through Context
Enterprises spend significant resources in the ongoing management of their network, with up to 3 times the dollars spent on managing the network than on the infrastructure itself. Whether it is network health monitoring, change management, load balancing, detecting failures, or diagnosing and debugging issues, it takes time, which draws organizations away from their core focus of running their business. The ability to easily collect, manage and analyze data will create winning organizations. In the new era, the network will become a fully automated system that provides contextual insights into users, devices and applications; and that can self correct and enable intelligent decision-making and outcomes.
Cloud First, Edge Ready Applications
The proliferation of cloud applications continues to transform traditional architectures and traffic patterns, ushering a need for organizations to re-architect their network. And now, with the emergence of applications at the edge for IoT control, firewalling, intrusion prevention, network monitoring, telemetry, and analytics, the network needs to be ready for applications hosted anywhere. The network will evolve, to not only enable consistent secure access from edge to the cloud, but also enable hosted applications at the edge.
In the new era of intent driven networking, we must evolve. The opportunity is immense and organizations must seize this opportunity to reap the full rewards of digitization. For an organization to transform, the following are fundamental –
- A new culture that drives and rewards innovation. A traditional culture with restrictive change management and stringent approvals has paralyzed organizations. In the new era, we must adopt new tools and processes.
- Investment in people with new skills and capabilities in the cloud, DevOps, software, APIs and analytics.
- Cost and functional innovation. Full automation will enable organizations to tackle higher priority business problems.
- A closer partnership between network and security teams to design and implement the most secure, most agile and comprehensive architecture to protect their business.
The new era of intent based networking is here. How do you believe organizations will transform? What help do organizations need to embrace this new era? I would be interested in your thoughts.
For more information on the Catalyst 9000, SD-Access or the Network Intuitive, click here.
#NetworkIntuitive