You didn’t think WannaCry was the end of the ransomware story, did you?
This week, a new ransomware exploit began sweeping Europe and apparently made its way into the United States in a matter of hours. Although many press accounts identified the malware as Petya, Cisco’s Talos threat analysis team has documented it to be distinct from Petya and dubbed it Nyetya.
Nyetya encrypts the victim computer’s master boot record. Once it enters a system, it has several means to spread through the network. Microsoft issued patches several months ago, but unpatched systems are vulnerable.
Our U.S. Federal customers who want to be sure they are safe from the exploit can click here for the latest information from Cisco, including a rundown of our Ransomware Defense solution.
Ransomware is a type of malware that encrypts the victim’s files and promises to decrypt them once a ransom is paid. Sometimes the attackers keep the promise to set things right, sometimes they do not.
Get the scoop on the state of federal cybersecurity.
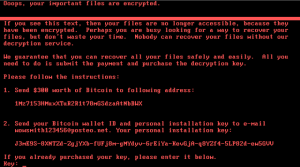
In this case, paying the ransom (something nobody recommends doing) is already impossible: The company that hosted the address where victims were to send their payments shut down the account once it became aware of the scheme, reports The Verge.
Ukraine appears to have been hardest hit, with the attack locking data in banks, public transportation, the airport and power systems, among other targets.
The new ransomware does not yet have an obvious mechanism of transmission, according to Talos. At least some of the infections appear to be connected to software updates for MeDoc, a Ukrainian tax accounting package.
Get more of the technical details from Talos here.






Excellent post, and links, agree with your insights.