We’ve talked about the market transition from implicit to explicit trust. It’s not enough to go on the word of an individual or the reputation of a vendor, customers are demanding explicit trust. Explicit trust is trust that is earned, not assumed. In other words, our customers are demanding evidence to confirm trust.
I am thrilled to share that we have taken a massive step towards explicit trust.
Cisco has created a framework, in partnership with the National Institute of Standards and Technology, for automating and testing the correctness of a foundational security mechanism – cryptography. As the world goes digital, there is an even higher reliance on cryptography because of its fundamental role in allowing for the transformation of information to prevent others from observing its meaning or adversaries reaching it to do harm. This new breakthrough allows us to test the cryptography, on demand and in real-time, to ensure it is behaving how we expect it to be. It is a first, yet crucial, step in putting forth automated, transparent, data driven methods to earn customers’ explicit trust. Our intent is to be completely transparent with the technology by providing open source code and will be leading the development of an international standard for the supporting protocol through the Internet Engineering Task Force.
For the new digital world with live in, with interwoven systems being created and massive amounts of data being generated, a new level of trust is needed. It’s important to stop and just think about what we are asking – for both Cisco as a company and all of us as an industry – in terms of trust. We are asking our customers to trust the systems that manage and process their data, the people and partners who access their data, the systems and controls and the fundamental technologies and processes that protect their data. With so many systems, handling so much data, it is near impossible to get that evidence in a timely and scalable manner.
Any discussion about trust needs to include transparency. Transparency is important but being transparent about the right information is critical. For example, our customers challenge us about our products being secure. They ask, “Why would I trust the router I just bought from Cisco?” To prove it, we would hand over information about all of our security tests, all of our design documents and in some cases even pieces of our source code. Within this pile of massive amount of information is a needle or the right piece of information to prove that router’s trustworthiness to that customer. It can become about time and efficiency. Right now, enterprises and government entities alike are investing a ton of money building complicated certification activities that only do a fraction of the job. The digital world amplifies the complexity. To keep up, we need automated capabilities that allow us to challenge systems in real-time to their trustworthiness – i.e. asking it to provide information about its activities and verify it is indeed doing what we expect it to be doing. It requires an automation of explicit trust.
This is why Automated Crypto Validation Protocol (ACVP) was created. ACVP allows for automated, simple ways to empower any customer to challenge the trust of a critical security system (via cryptography) in order to inexpensively, and quickly, provide real-time evidence of explicit trust. It’s a game changer and provides the opportunity for organizations to have the confidence to adopt new technologies quicker. Similarly to ACVP, innovators need to create more automated, simple ways to confirm the integrity and trustworthiness of platforms.
Trust is a long-term journey. It requires a long-term approach and commitment to constant improvement. For more about Cisco’s journey and commitment to Trust and Transparency, please visit our Trust Center.
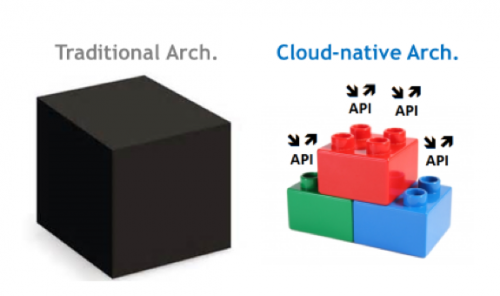







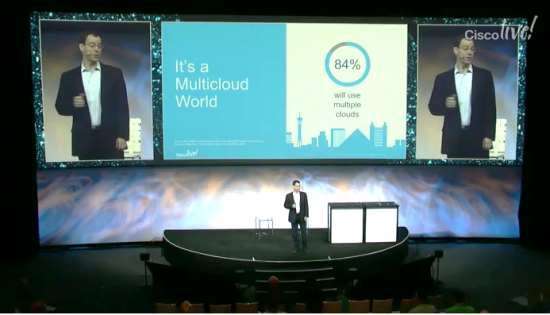 Multicloud was also a big topic. Chuck said it best when he half-jokingly asked in his keynote, “How many of you use ONE cloud?” <Audible groans and chuckles from the audience>.
Multicloud was also a big topic. Chuck said it best when he half-jokingly asked in his keynote, “How many of you use ONE cloud?” <Audible groans and chuckles from the audience>.