New OpenTofu Providers for Cisco Technologies Now Available!
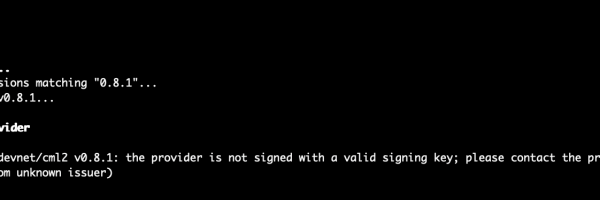
If you are cloud-native, you probably work with Terraform modules and providers. Since Terraform changed its license, some communities and companies have decided to keep the project open-source and create OpenTofu. OpenTofu is a fork of Terraform