The Challenge of Encrypted Traffic Inspection
Traffic inspection remains one of the most critical capabilities in modern firewall systems. However, the widespread adoption of encryption protocols like TLS and QUIC has created significant blind spots for traditional deep packet inspection (DPI) technologies. When traffic is encrypted, firewalls cannot examine packet payloads, leaving security teams without crucial visibility into what’s traversing their networks.
While decryption technologies offer one solution, they’re not always practical. At Cisco Live! 2026 Security Operations Center (SOC) in Amsterdam, we analyze a passive copy of network traffic (SPAN) rather than sitting inline. This is where Encrypted Visibility Engine (EVE) becomes a gamechanger, providing valuable insight into encrypted connections without requiring decryption.
What is Encrypted Visibility Engine?
EVE identifies client applications and processes in TLS and QUIC encrypted traffic by fingerprinting the ClientHello message – without ever decrypting the connection. This enables visibility into the source process by generating encrypted connections, a capability traditionally limited to endpoint antivirus and anti-malware software.
The technology leverages machine learning algorithms developed at Cisco, providing Cisco Firewalls with a database of over 10,000 known client process fingerprints, paired with 35 billion connections determining destination context of the encrypted connection. Beyond legitimate software, EVE detects known malicious processes. Coverage continuously expands to identify encrypted malware traffic without intrusive man-in-the-middle decryption.
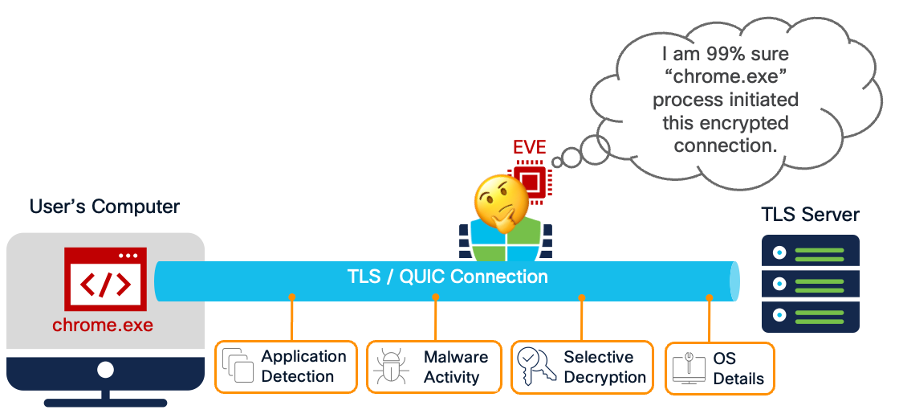
In inline deployments, EVE provides Intelligent Decryption Bypass capability—a dynamic, risk-based approach to preserve performance by skipping inspection of the lowest-risk connections. By combining EVE’s connection threat score with Talos server reputation intelligence, organizations can confidently bypass decryption for low-risk traffic while focusing resources on potentially malicious connections.
EVE also enhances passive host discovery by improving operating system identification from encrypted communications, increasing accuracy for application visibility, vulnerability insights, and features like Snort Recommendations.
It’s important to note that EVE is not a replacement for decryption and packet inspection, when possible, but rather an additional layer of defense in Cisco Secure Firewall’s comprehensive threat protection arsenal. While EVE’s machine learning models are highly accurate in most cases, they are probabilistic by nature and may occasionally produce false positives, false negatives, or misclassify applications. Organizations should leverage EVE as a complementary capability alongside traditional security controls, using it to enhance visibility and guide more intensive inspection efforts when suspicious activity is detected.
Real-World Threat Hunting: How much can happen within 48 seconds
Theory is valuable, but how does EVE perform during actual threat hunting in a live environment? Here’s a compelling incident we discovered while monitoring conference participant traffic on Cisco-provided Wi-Fi.
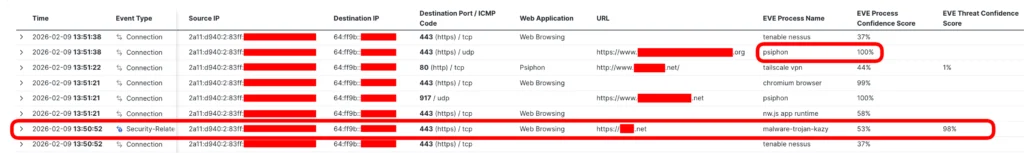
EVE flagged a fingerprint matching Kazy Trojan establishing a command-and-control (C2) connection over an encrypted channel. Further investigation revealed a whirlwind of suspicious activity: the endpoint used Psiphon software to bypass network restrictions, attempted multiple SSH/Telnet connections, and possibly ran Nessus scanning software.
The entire sequence unfolded in just 48 seconds, before the endpoint was disconnected from the network.
The Kazy Trojan Connection
EVE detected an encrypted connection originating from a Kazy Trojan binary with a 98% confidence score. Pivoting to EVE’s Process Analysis dashboard in appid.cisco.com revealed that Cisco Secure Malware Analytics (formerly Threat Grid) previously recognized this fingerprint across multiple malware samples. This pattern indicates that malware authors are likely reusing similar core components, including cryptographic binaries.
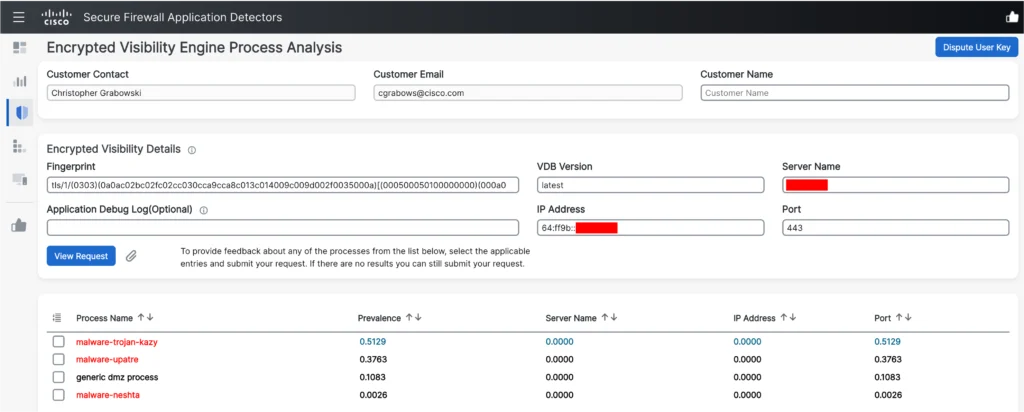
EVE’s probabilistic classifier matched the “malware-trojan-kazy” sample based on the highest prevalence of connections to destination TCP port 443 among known fingerprints. Importantly, neither the destination IP address of the server nor the Server Name Indication (SNI) server name visible in the TLS handshake is added to known lists of malicious IPs/domains. Without Encrypted Visibility Engine, this connection would have succeeded unnoticed by a security analyst.
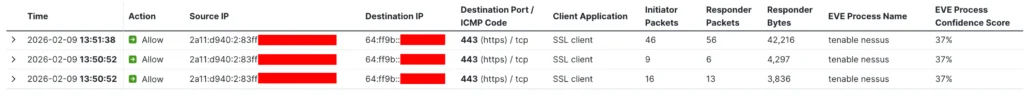
Possible Nessus Activity
Next, EVE detected three encrypted connections to public IP addresses using a binary with a 37% confidence score for Tenable Nessus. While the lower confidence requires additional investigation to confirm whether this was Nessus, it could indicate a process Cisco’s ML system has never observed – potentially a red flag for a suspicious custom-built binary.
SSH and Telnet Connections
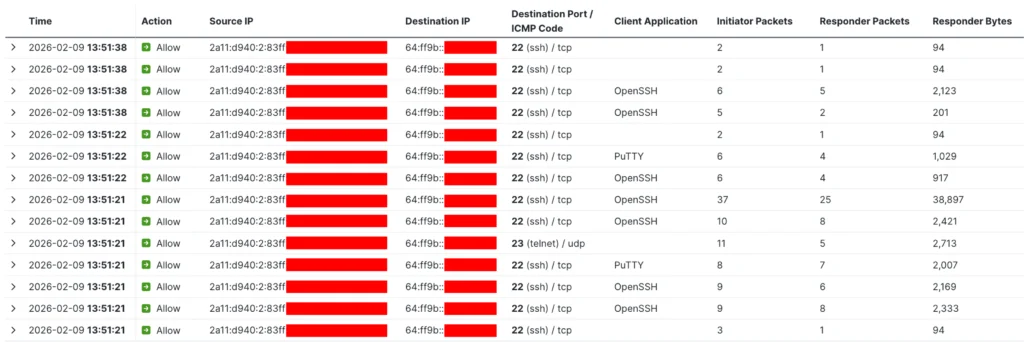
The client initiated a series of SSH connections and one Telnet connection. Analysis of responder packets and byte counts confirmed the endpoint successfully established connections to several servers. The destinations used public IPv4 addresses, which the endpoint reached via NAT64/DNS64 translation.
Psiphon: The Evasion Tool
Just before disconnecting, EVE detected two outbound connections using Psiphon—a circumvention and anti-censorship tool. Psiphon functions as a VPN/proxy hybrid that obfuscates traffic to resemble normal web activity, using multiple techniques to evade blocking and dynamically switching methods to remain accessible.

What made this particularly fascinating was how these connections attempted to bypass traditional firewall security controls:
- QUIC protocol usage: a blind spot for most competitor firewall solutions
- Non-standard UDP port 917: designed to deceive security devices expecting standard ports
- Unknown, uncategorized SNI: making the connection appear benign to URL reputation filters
EVE added a crucial layer of visibility that’s extremely difficult and expensive for attackers to forge: the cryptographic fingerprint exposed by the software during the QUIC or TLS handshake.
Incident Summary
The incident timeline reveals the sophistication of modern threats leveraging stealthy cryptography capabilities and traditional firewall blind spots. In just 48 seconds, the endpoint:
- Connected to a C2 server via Kazy Trojan
- Used Psiphon circumvention tool
- Attempted multiple SSH/Telnet connections
- Possibly ran Nessus scanning software
We discovered this activity thanks to EVE flagging an Indication of Compromise (IoC) on the C2 connection. The endpoint is considered highly suspicious and likely to perform additional harmful actions if it reconnects to the network.
This incident was escalated for further investigation. The observed behavior suggests either a user unaware of malware running on their device or someone intentionally attempting to bypass filtering controls and conduct reconnaissance.
The Value of EVE
This real-world incident demonstrates how Encrypted Visibility Engine provides security teams with:
- New visibility angles: process-level detection without endpoint agents
- Encrypted traffic analysis: insights into fully encrypted connections without decryption
- Rapid threat detection: identifying suspicious activity in seconds
- Defense against evasion: detecting circumvention tools that use advanced obfuscation
In an era where encryption is the norm, EVE ensures security teams maintain critical visibility without compromising privacy or performance. EVE detected malicious activity across encrypted QUIC and TLS connections, without decryption. The connections used non-standard ports and obfuscated/benign SNI values that would bypass traditional security controls. Without Encrypted Visibility Engine this 48 second connection would likely pass unnoticed by the Security Admins leaving the network at risk of further reconnaissance or lateral movement.
To explore how Encrypted Visibility Engine can enhance your security operations, visit Firewall Essentials Hub and watch the latest BRKSEC-3320 deep-dive session covering TLS/QUIC decryption and EVE in Cisco Live! On-Demand Library.
Check out the other blogs from our SOC team in Amsterdam 2026.
We’d love to hear what you think! Ask a question and stay connected with Cisco Security on social media.
Cisco Security Social Media






It’s really a good idea by analyzing the encrypted network traffic without decrypting it. Also, This is the first time I’m seeing this kind of security techonology. This tool will definitely give some insights to the SOC analysts and reduce the MTTR.