Cisco launched Secure Agile Exchange (SAE) last week in Berlin, Germany, as part of Cisco Live Europe. It was part of our DNA Virtualization announcement – so subtle you might have even missed it. We’ve been working on Secure Agile Exchange (SAE) for the last 3 years. We have a few customers going into production now with at least another 2 dozen in the pipeline. It is not a single product or SKU, but a comprehensive solution. SAE was derived from concrete challenges and problems we’ve heard from an endless number of customers. Economists often say that innovation comes from small firms and most of the time they are right – not this time.
What is SAE?
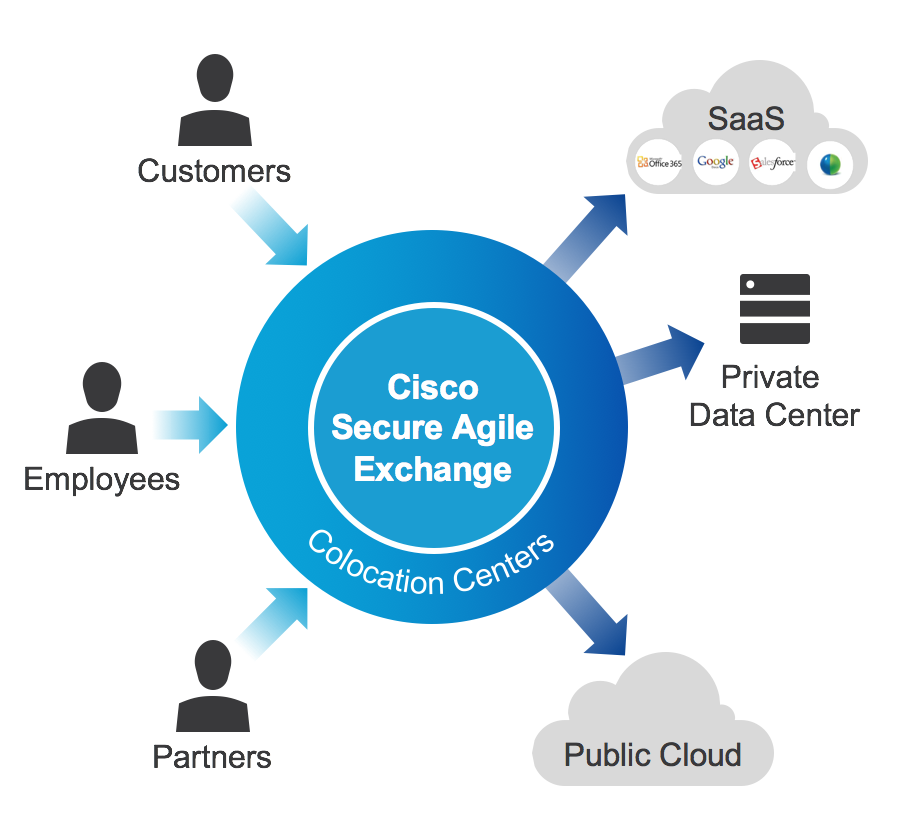
SAE securely connects users – employees, customers and partners to applications across private data centers, public IaaS clouds and/or public SaaS clouds.
SAE enables enterprise hybrid cloud, reduces circuit costs, offers carrier/cloud independence, enforces consistent security, simplifies Moves/Adds/Changes, optimizes traffic flows, and reduces infrastructure. SAE is an open orchestrated NFV platform that doesn’t require the operational complexity of OpenStack or software switching overlays yet delivers on the benefits of virtualization at scale. SAE lives up to its name by securely connecting enterprise application consumers to providers leveraging x86 based hardware when possible and purpose built hardware when necessary.
The foundational components of SAE are the following:
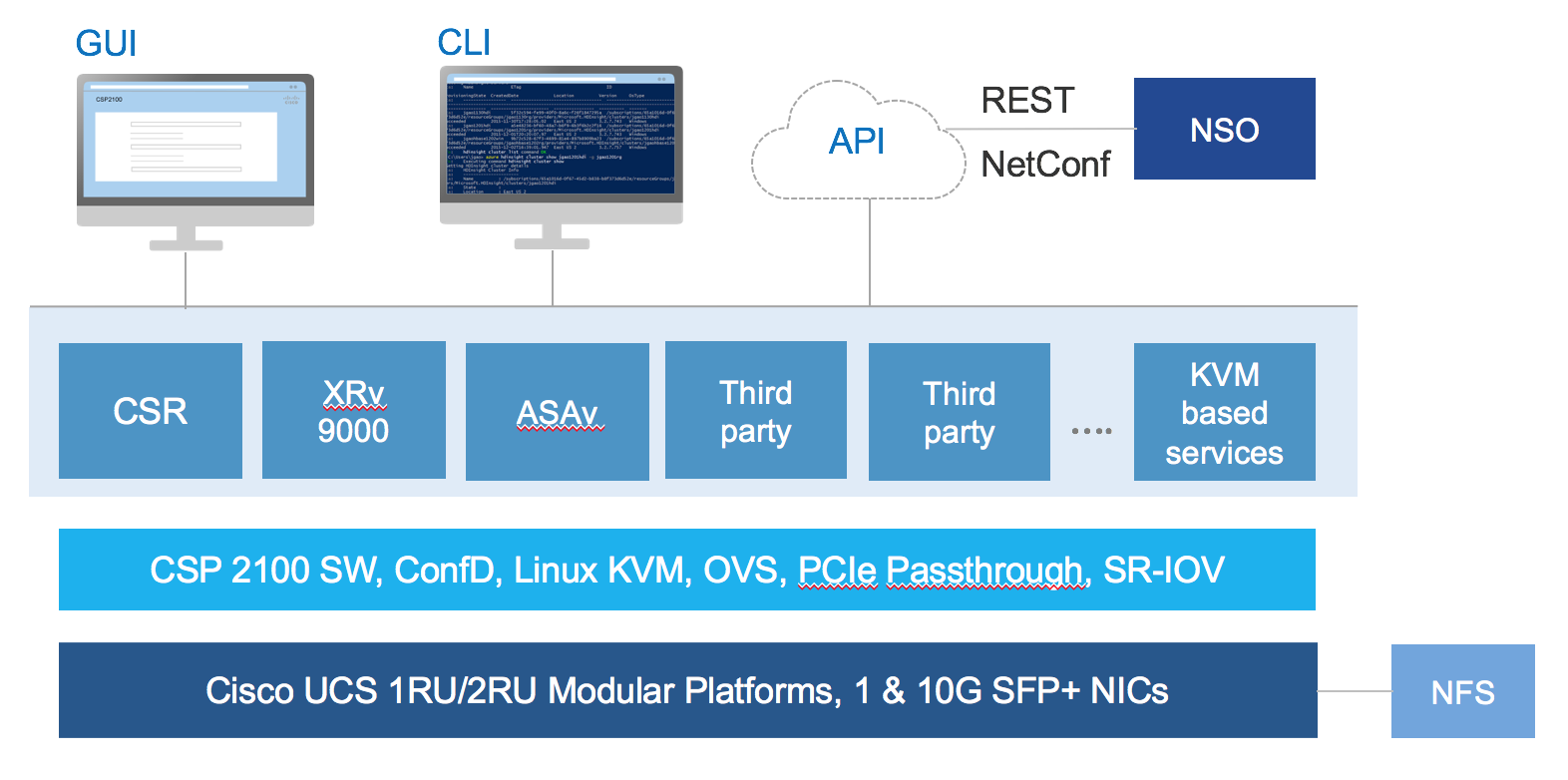
- High-performance NFV platform: Cloud Services Platform (CSP) 2100
- Network services: Cisco VNFs such as CSR 1000V, ASAv, NGFWv, as well as 3rd party services such as the Avi Networks loadbalancer
- Switching fabric: Nexus 9000 Series
- Customer services: Advisory & implementation services; and optional Cisco Managed Services
What are the principles of SAE?
- Virtualize, Orchestrate and Automate
- Virtualize, Orchestrate and Automate
- Virtualize, Orchestrate and Automate
Virtualize
Virtualization is foundational to orchestration and automation. In networking, VLANs were instrumental in reducing the number of switches required to provide the desired network segmentation. A single switch could be securely shared through re-programming. The same holds true for Virtual Network Functions (VNFs) which can be created, retrieved, updated, and deleted (CRUD) through programmatic interfaces (CLI, Rest API, GUI, Netconf/Yang).
You can simplify and dramatically speed up your operations by making the leap to NFV. There are very few use cases today in which you need a purpose-built physical appliance for L4-7 services. SAE is built on a cluster of Cloud Services Platform (CSP) 2100s, an x86 hardware and software platform for data center NFV. Scaling up and down and adding new services can all be done remotely and can be automated. The CSP 2100 negates the need to order, cable, rack-and-stack dedicated hardware appliances every time capacity needs to be increased or changes are required. Rolling in new purpose-built hardware appliances to increase capacity is not agile. A pool of NFV compute resources based on the CSP 2100 is agile. Also, we are seeing the trend to have a virtual firewall and virtual router per tenant so updates and problems do not affect other tenants (something not possible in the physical world).
Orchestrate
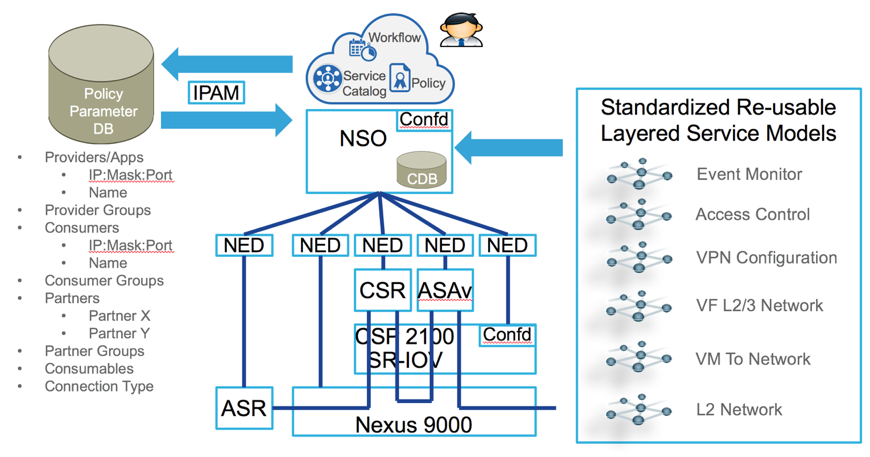
Orchestration is the non-real time configuration across many components within the SAE fabric to create a consumable end user service chain. Within a single SAE location, application consumers and providers meet at an orchestrated cross connect built upon intelligent high speed switching, virtualized network services hosted on x86 compute, patterned and orchestrated for service catalog based operations.
Orchestration can be manual or automated. If the end user service will be implemented frequently, then the orchestrator used within SAE is Cisco’s own Network Services Orchestrator (NSO). The power of NSO lies in its model-to-model mapping principles. It is able to describe complex services at the Service Layer and map those services to device models, which represent different devices from different vendors. This way, complex services can be described and implemented in a simple way and pushed to the devices without having to worry about device vendor, configuration semantics, configuration interfaces, etc.
Automate
Automation is the workflow of collecting parameters and approvals to feed orchestration in support of creating end user services. Automation originates with business policy that is collected through a workflow based portal. The automated workflow may be retained in a service catalog and reused through an abbreviated workflow.
Automation is targeted at those zones that have frequent and complex Moves, Adds and Changes (MAC). Extranet zones and application hosting zones are places where MACs usually occur frequently. Even though MACs of applications and partners occur frequently, the basic connectivity and service chains in these zones will not change that often. As a result, the automation focus is on the application specific policies that change often.
For additional details, please see our SAE Solution Overview. If you have questions/comments, please email us at csp-2100@cisco.com.



