“You’re doing … what?! And … where?! 5G? What’s that? And why in Orkney?!”
Last weekend I took holiday Friday and Monday – including my Cisco “Birthday Day Off”– to travel to Switzerland for some early season skiing with friends.

Inevitably we talked occasionally about work, and I mentioned I was working on a cross industry/academia/public sector initiative related to 5G. The aforementioned questions and surprised reactions were indeed pertinent. The “What is 5G?” question is a good one. I’ll return to that later, in part 2 of this blog. The question “Why Orkney?” is key and will surprise many, hence I will address that question in this blog. First here is a summary of what we are up to.
This past year I’ve been a Cisco board member representative on an initiative called the Scotland Innovation Partnership (SIP) which was set up to tackle some of the challenges of rural broadband, 4G mobile – and now 5G – coverage. As a team we decided to try to enter the UK Government’s Department of Digital, Culture, Media and Sport (DCMS) “5G Testbed and Trial” competition, which was announced (just!) around the end of October. After the inevitable moaning about the extremely short timeframes, we rushed – starting with a few members of SIP – to form a consortium which we decided to call the “5G RuralFirst Partnership”. We expanded the consortium to include some real innovative like-minded and rural-focused organizations. We aimed to deliver a compelling 5G competition entry, which I believe we now have, which was submitted just in time for the December 13th deadline. This blog is my perspective on what has been a very exciting few weeks.
Caveat: This is a Competition and We May Not Win
What I will describe is our proposal entered into the UK DCMS Testbed and Trial competition, and our journey to submission. My blog should not be interpreted as a commitment that we will bring 5G to Orkney and Somerset. We will only progress on this ambitious cross industry/academia/public sector collaborative R&D project if we are judged one of the 10 winners of this UK-wide competition. I expect competition to be tough. Extremely tough. And if we are not judged as worthy winners, I will still remember these past few weeks as a tremendous learning experience and some of the most exciting weeks of my working life. Oh – I almost forgot – the ski weekend away was pretty exciting too!
The Race to Enter the UK DCMS 5G Competition
In the space of a few weeks, we have formed a wide-ranging consortium – from major high tech companies to public sector organizations to some specialist small and medium enterprises (SMEs) who can deliver very targeted capabilities. We have very ambitious goals to develop and test 5G capabilities. We have 4 main tracks to our program, one of which involves developing and testing advanced radio spectrum capability in the Orkney Isles, which are located to the north of Scotland in the UK. Another track involves examining how IoT and agricultural technology will impact and/or benefit from 5G – and we’ll run some of these tests in rural Somerset in the south western corner of England.
The 5G RuralFirst Partnership I am very happy to say, will be led by Cisco Systems UK & Ireland, and specifically by our Cisco CREATE innovation team. If (and only if) we are judged one of the competition winners, we plan on (literally!) taking 5G testbeds and trials to diverse and challenging rural locations – from Scotland’s Orkney Islands to the rolling hills of Somerset in south-west England (and a few other testbeds in-between). Our goal is to investigate solutions – new technologies as well as potential new business models – to some of the challenges, both technological as well as economic, of rural 5G connectivity.
The Rural Connectivity Market Opportunity: Solutions and New Business Models
With a world population of 7.6 billion and (only) 3.2 billion connected to the internet, the market opportunity for internet-related services and products is actually greater with people who are unconnected. With approximately 40% of the world’s population living in rural areas, the segment of internet services and products for rural communities – and on transport links to, from and around these communities – is almost certainly one of the biggest internet market opportunities today for innovative and disruptive suppliers. However, it is also one of the most poorly served market opportunities.
With such a huge market opportunity, there is a significant market opportunity for the UK – or it has to be said, another country with challenging rural areas – to become a leader in innovative products and services (such as in 5G spectrum innovation, agricultural automation technologies, and rural industrial IOT) and the necessary enabling business models which make rural internet investments feasible and attractive to public/private partnerships.

The 5G RuralFirst competition entry will test the viability of using 5G to provide critical connectivity that is sharable, potentially even on a licence-exempt basis. The challenge in trialling such connectivity is amplified by the geography of Scotland and other parts of the UK, with rugged coastlines, large numbers of Islands, mountainous areas and challenging weather conditions. Here, the cost economics of rural broadband and mobile delivery are not attractive to the free market and therefore become a financial burden on local, regional and national governments who must intervene to make necessary investments. Hence it could be said that 3G and 4G have at best under-served rural communities – with a notable exception of UK MNO EE’s expansion, driven by public sector investment in connectivity for Emergency Services together with – in my view – a real and genuine ambition to cover 100% of the UK’s geography. EE as an example, have just this past January (2017), delivered 50 MB/s 4G connectivity to Glencoe Mountain ski centre, a connectivity-challenged, significant tourist attraction which I blogged about in March 2016.
The 5G RuralFirst Partnership – following the charter we developed in the aforementioned Scotland Innovation Partnership – has been formed to kick-start the development of products, services and (arguable most importantly) the new business models which address the challenges and cost economics of rural internet connectivity. And I’m delighted that we have such a strong partnership, excellent teamwork, vision and identified innovative test cases to make a dent in this huge opportunity.
Let me now introduce a few members of this 5G innovation partnership (next week I’ll publish a full list).
5G RuralFirst Partnership
The 5G RuralFirst consortium contains a diverse mix of academic institutions, major global technology vendors, and small/medium enterprise specialists. Led by Cisco Systems, the consortium includes the following major organisations as “Key Project Partners” who all provide funding if this proposal is one of the winners. In addition to Cisco, we have the BBC, BT, and Microsoft and more as Key Project Partners.
From academia, Key Project Partners include: the Universities of Strathclyde, Edinburgh, Harper-Adams, Heriot-Watt and Surrey, CENSIS and the Agricultural Engineering Precision Innovation Centre (Agri EPI Centre). This competition is particularly important to our academic partners. If we are judged one of the winners, the grants from the government will enable them to invest in further 5G research, development and most importantly commercialisation, an area Cisco is looking forward to assist with.
As SMEs (specialist small/medium sized enterprises), key project partners include Broadway Partners (London-based), CloudNet (Orkney), DataVita (Chapelhall), Lime Microsystems (Surrey), Milkalyser (Exeter), PureLiFi (Edinburgh), Soil Essentials (Brechin, Angus), Zeetta Networks (Bristol), and others. I never thought I’d see Cisco partnering with such a wacky list of partners 🙂 however in the world of IoT, it’s very satisfying to see such small companies in the 5G RuralFirst Partnership. Indeed I personally hope that our competition entry will provide a platform for these innovative UK companies to showcase their solutions on a global stage.

I was personally delighted when we convinced DataVita to join our team (literally only last week) – a local company I blogged about last year. They are based not too far from the Cisco office in central Scotland and are one of only 3 Tier III data centres in the UK. With DataVita’s expertise and state of the art, Cisco ACI-enabled data centre, Cisco and the 5G RuralFirst Partnership aim to be the first “production-grade” 5G testbed and trial project in the UK, with deployment in the impressive DataVita data center (again, only if we are one of the winners of the DCMS 5G competition) .
Another particularly interesting partner is Shefa, a subsidiary of Faroese Telecom – which brings tremendous diversity, experience and opportunities for further innovation to the partnership. I’ve got to say, I was genuinely excited when I heard that Faroese Telecom was joining the team – there is 4G on the Swiss ski slopes (sad person that I am). I remember flying – sorry struggling – down a black run with “Wow, I can’t believe we have Faroese Telecom on the team” continually running through my mind. Such diversity is bound to drive innovation! Faroese Telecom will bring strong experience of addressing rural connectivity challenges and will provide the fibre connectivity we need from Orkney to the DataVita data centre.
Finally, we have excellent public sector support – including for example Orkney Islands Council, as well as the Scottish Futures Trust (SFT – a public corporation of the Scottish Government) and the Scotland Innovation Partnership (SIP), who are also key project partners providing funding and/or resources – and indeed SFT and SIP are the genesis of the 5G RuralFirst Partnership.
Why Trial 5G in the Orkney Islands?

The Orkney Islands form an archipelago in the Northern Isles of Scotland, situated off the north coast of Great Britain. Orkney is 16 kilometres (10 mi) north of the coast of Caithness in Scotland and comprises approximately 70 islands, of which 20 are inhabited.
Why, then, setup a testbed and run a 5G trial in Orkney? The answer is simple: because it will be a real challenge! Orkney is about as rural as you can get in the UK. It’s not even on the UK mainland, and even only recently was raised in the Scottish Parliament as an example of an area with below average superfast broadband availability, with only 75% of the Islands premises being served by fibre-to-the-cabinet (FTC). Additionally, the weather can be quite wild – which can cause challenges such as out-of-alignment microwave dishes. It’s also steeped in history and rural beauty and is a lovely tourist destination – although these factors (honestly!) have not influenced out choice of one of our 3 5G testbed and trial locations.
Finally – we really do believe that 5G R&D teams must seriously address rural connectivity challenges right off the bat, so that 5G is not impacted by the same challenges that dog 3G and 4G today. The SFT-led Scotland Innovation Partnership set that goal very clearly for us, given the challenges of rural broadband and 4G delivery in the UK, and particularly in Scotland. We are thinking “rural first” – hence the name of our consortium, 5G RuralFirst.
More Next Week ….
It’s been an exciting few weeks. Coupled with a ski trip and my Cisco “Birthday Day Off”, it will be hard to beat. I’ll write a part 2 to this blog over the next week or so, to describe more of the 5G RuralFirst competition proposal, and – again only if we are one of the competition winners (caveat caveat!!) – hopefully there will be further episodes of our 5G RuralFirst adventures once the DCMS 5G Testbed and Trial execution phase starts in April 2018.
PS: Another local university, the University of Glasgow, have also formed a consortium and have submitted a 5G competition entry. I’d like to wish them all the best in their bid!
PPS: I do need to apologise to my ski friends, James, Jon and Colin – sorry Patrick (holiday joke :-)) – they say I talked non-stop about 5G last weekend. I’m convinced that is not true. However, with 5G (realistically) a few years away from widespread production roll-out, they are sick fed-up of it already 🙂


 Guest blog by:
Guest blog by: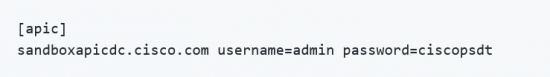
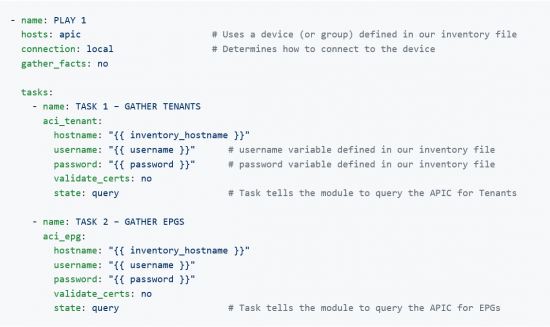
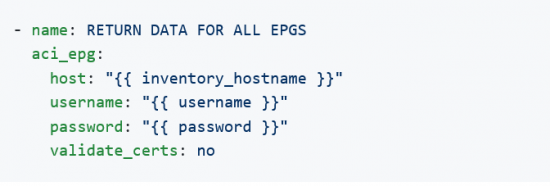
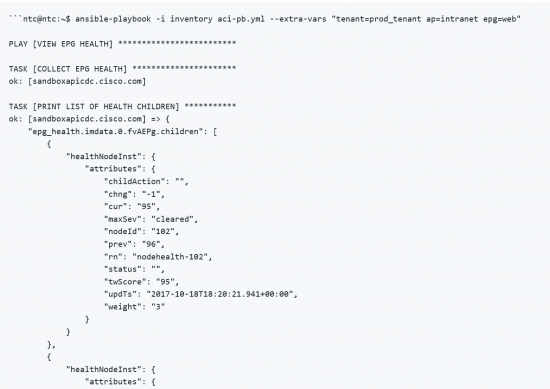
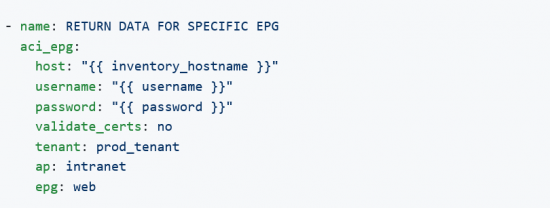 This task will return all EPGs in the specified Application Profile, intranet, since the epg parameter is not provided:
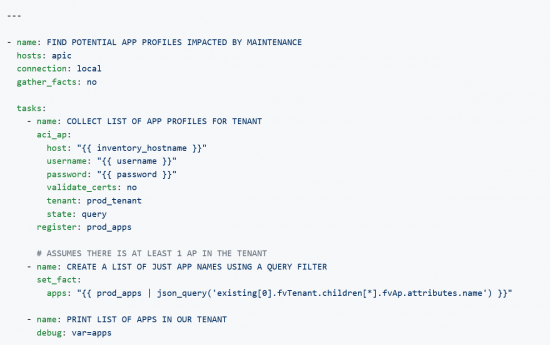
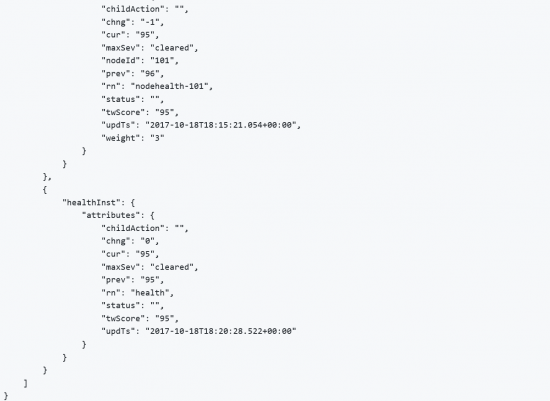
This task will return all EPGs in the specified Application Profile, intranet, since the epg parameter is not provided: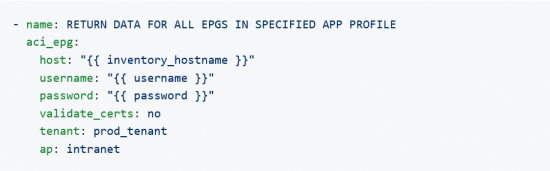 This task will return all “web” EPGs in the specified Tenant regardless of Application Profile since the ap parameter is not provided:
This task will return all “web” EPGs in the specified Tenant regardless of Application Profile since the ap parameter is not provided: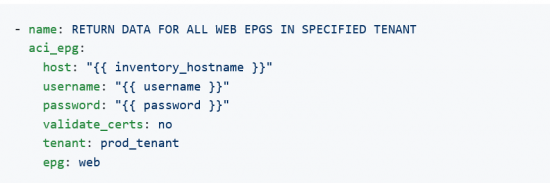
 Guest blog by:
Guest blog by: