Cisco LaunchPad’s startup cohort #2 graduated with resounding success. All eight startups received an enthusiastic response from investors, partners, and the Cisco Community. Currently, Cisco LaunchPad has 16 startup alums, of which seven are actively engaged with Cisco on technology and Go-to-Market collaboration. Through Cisco LaunchPad, we are building engagement with highly relevant startup communities and their networks.
It is now time to welcome Cisco LaunchPad’s cohort #3 startups. For this cohort, we focused on key technologies such as IoT, Security and Mobility and fine-tuned the selection process to better assess startup potential and program fit: more intense, front-loaded, and Agile. Fifteen shortlisted startups attended a three-day immersive bootcamp session at Cisco, covering the following themes:
- Product Market Fit
- Brand, Revenue Model, Pricing, Distribution Strategy
- Tactics to validate/iterate fast
After joint learnings and a week of applying those learnings in the real world, the startups returned for detailed pitches and deep dives with Cisco teams. From there, we selected eight startups with strong growth potential and alignment with Cisco technology and/or GTM. These exciting startups are leveraging cutting-edge technologies such as edge compute, ML/AI, sensor fusion, and Homomorphic Encryption to deliver innovative IoT and Security solutions.
Please join me in welcoming Cisco LaunchPad Cohort 3:
Asquared IoT: Machine learning and edge compute enabled monitoring of production quality and Overall Equipment Effectiveness (OEE) in manufacturing factory floors.
Atoll Solutions: End-to-end solution for asset tracking, tracing and even usage.

eXabit Systems: Cloud-based IoT Agri-Tech platform with a focus on Smart Sensing & Monitoring, Smart Control Systems and Smart Crop Analytics.
FluxGen Engineering Technologies: IoT-based water management solution that can help in saving water expenditure by up to 15%.
SenseGiz: Enterprise and Industrial IoT products for sensor-based condition monitoring, security and real-time asset/people tracking applications using a combination of connected hardware, cloud, analytics and apps.
Talasecure: Lifetime security for IoT devices through a comprehensive, easy-to-use and affordable solution that helps device manufacturers to reduce time to market of secure devices.
Trapyz: Software platform from Planetworx that provides brands with location intelligence to map offline consumer journeys across multiple venues in the real world thus helping derive purchase intent, buying propensity and campaign attribution.
Ziroh Labs: Creating software-defined security stack with privacy-preserving, performant cryptographic algorithms.
Please stay connected with us on this initiative. Join us on Facebook and Twitter, @CiscoLaunchPad. Do visit our website to find out more about Cisco LaunchPad, opportunities to refer potential startups or to apply to this program.
 It shouldn’t come as a surprise that an increasing number of applications and workloads are moving to the cloud. Due to the ability of cloud infrastructure to scale quickly and efficiently, cloud operators are delivering a growing variety of services to businesses and consumers alike.
It shouldn’t come as a surprise that an increasing number of applications and workloads are moving to the cloud. Due to the ability of cloud infrastructure to scale quickly and efficiently, cloud operators are delivering a growing variety of services to businesses and consumers alike.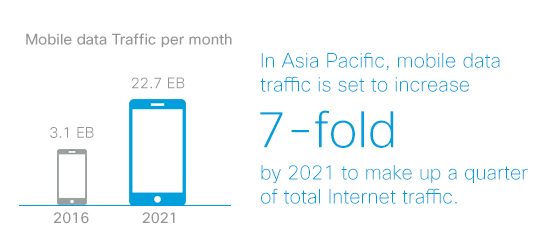 Smartphones have quickly become the main “communications hub” for many people across the Asia Pacific region, especially in countries such as India. Consumers and business users are increasingly using their mobile devices to access cloud-enabled applications such as collaboration, social networking and video streaming. Mobile data traffic in Asia-Pacific is set to increase 7-fold from 2016 to 2021 to make up a quarter of total Internet traffic. Of that traffic, 92 percent will be from cloud services, up from 85 percent in 2016*. This shift means that mobile users’ quality of experience will be increasingly dependent on the mobile network’s ability to deliver cloud services with high bandwidth and low latency.
Smartphones have quickly become the main “communications hub” for many people across the Asia Pacific region, especially in countries such as India. Consumers and business users are increasingly using their mobile devices to access cloud-enabled applications such as collaboration, social networking and video streaming. Mobile data traffic in Asia-Pacific is set to increase 7-fold from 2016 to 2021 to make up a quarter of total Internet traffic. Of that traffic, 92 percent will be from cloud services, up from 85 percent in 2016*. This shift means that mobile users’ quality of experience will be increasingly dependent on the mobile network’s ability to deliver cloud services with high bandwidth and low latency.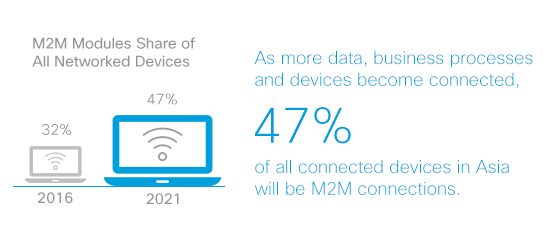 Cloud services are also accelerated by the unprecedented amount of data traffic being generated by not only people, but also machines and IoT connected devices. As more data, business processes and devices become connected, 47 percent of all connected devices in Asia Pacific will be M2M connections1. For service providers, the ability to create M2M connections can generate significant new business opportunities in the B2B and enterprise market segment. Service providers will need to leverage hybrid cloud enviroments to build these IoT platforms to allow for service agility and capability exposure to enterprises.
Cloud services are also accelerated by the unprecedented amount of data traffic being generated by not only people, but also machines and IoT connected devices. As more data, business processes and devices become connected, 47 percent of all connected devices in Asia Pacific will be M2M connections1. For service providers, the ability to create M2M connections can generate significant new business opportunities in the B2B and enterprise market segment. Service providers will need to leverage hybrid cloud enviroments to build these IoT platforms to allow for service agility and capability exposure to enterprises.
