Cisco commissioned Miercom to conduct an independent performance test on Huawei’s Agile Campus Network architecture. The test report consists of wired and wireless test cases. For the wired test cases, Huawei’s S5720-HI Series Agile Switch was compared and validated against the Cisco Catalyst 9300 and 3850 Series switches. This blog will take a deeper look at a wired network’s resources when implementing policy. This is specific to the section titled “Wired Infrastructure: Optimized and Secure Switching Resources” published in the Miercom Report.
If you want an overview and copy of the full report, see the Cisco Blog here
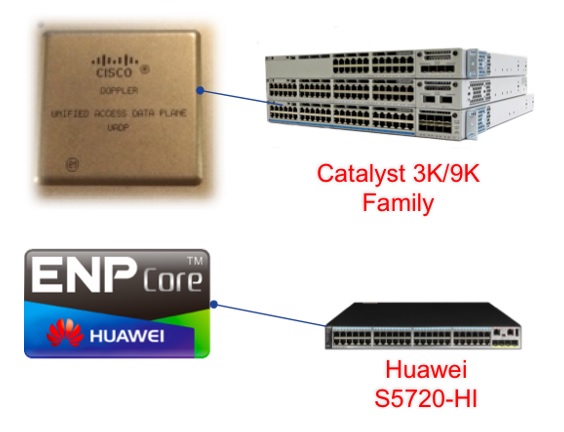
It’s important to note the Huawei S5720-HI switch series are built with Huawei’s custom silicon ENP (Ethernet Network Processor) chip. This compares against Cisco’s Catalyst 9300 and 3850 UADP based switches.
Miercom developed a multi-purpose test to assess the switch policy filter scalability limits and resource management. Additionally, each switch was tested to determine if it would be susceptible to a network security breach during adds/changes/deletes to an existing policy filter.
Why is this important?
With the emergence and growth of IoT markets, there is a critical need for security and segmentation. The network needs to correctively identify and provide controlled-access to what users, devices, and things have access to. Regardless of the communications medium, today’s world consists of dynamic access through automated policy. Without getting too deep into the implementation details of the policy stack, eventually the network infrastructure must support the ability of programming its resources both dynamically and statically. Network policy constructs are used in the form of Security ACLs, QoS Filtering, etc applied to physical and logical ports such as L2 VLANs, or L3 Routed Access interfaces.
An intent-based networking system supports an automated implementation of features. This requires the underlying hardware to be “ready” or in essence fully capable of supporting dynamic manipulation from the controller.
For implementing high-speed lookup functions, switching systems rely on special memory called ternary content addressable memory (TCAM). TCAMs are precious switching resources required to store policy rules and perform lookups based on configuration of the switch. Based on the desired intent, actions will determine the switch’s treatment of packets on the network.
How did they do it?
To investigate the behavior of the hardware capabilities, Miercom performed the following Test Methodology.
Miercom Test Objectives:
- When applying the same ACL to multiple interfaces, does the ACL consume N x TCAM entries, where N = number of ports to which the ACL is applied?
- Does the switch support optimized resources – ACL Sharing?
- How does the switch manage changes to the existing ACL? Is the system Secure?
- Does the switch allow denied traffic to be forwarded during ACL editing?
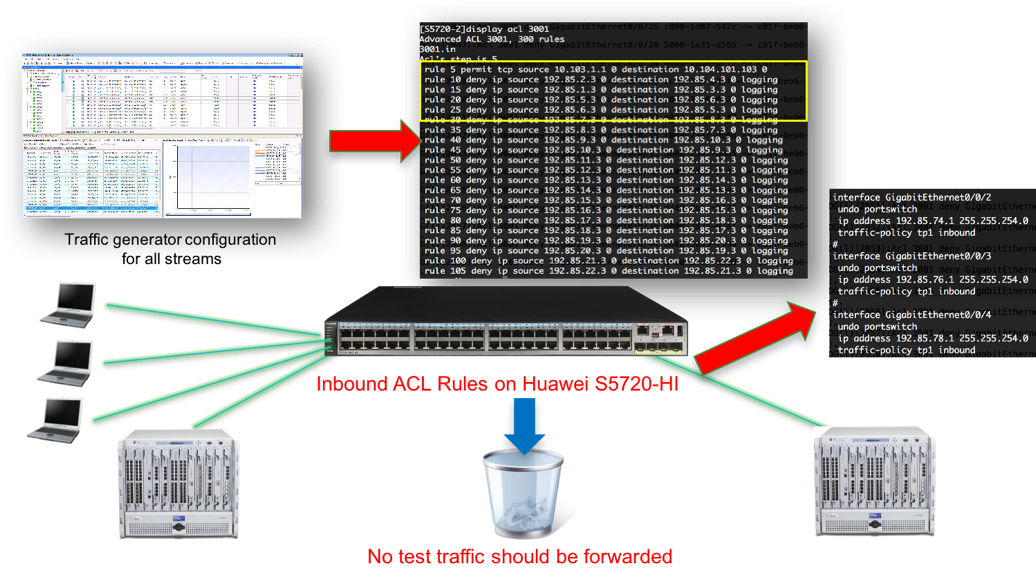
Each switch was configured with inbound and outbound policies applied to Layer 3 interface. A Spirent Test Center was connected to each switch for traffic generation against the ACLs conjunction with PCs connected to each switch to test for access to services such as FTP, ICMP, Telnet, and SSH. The switches were monitored for resource utilization such as TCAM, CPU, acl counters, and system logging.
When applying the same ACL to multiple interfaces, the ACL consumed N x TCAM entries, where N = number of ports to which the ACL is applied. For example, on the Huawei S5720-HI, an inbound ACL with 300 rules applied to all ports (48 x southbound interfaces and 4 x uplink interfaces) consumed 15,600 rules. When attempting to apply the same ACL for outbound direction, the S5720-HI was limited to only a subset of interfaces as it completely exhausted the hardware resources of the Huawei Switch. Huawei’s resource allocation was not optimized and did not offer scalability for this test case. Their documentation recommends the user to perform a merge of rules, change of the hardware resource template, or switch to a VLAN based approach.
Miercom observed when applying the ACL to all 48 ports of the S5720-HI, the switch exhibited significant amount of time (minutes) for the ACLs to the become active.
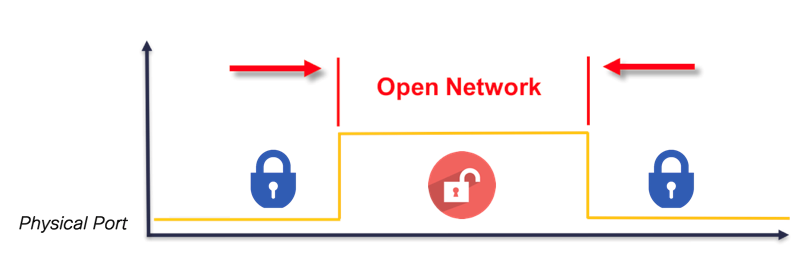
Miercom also observed when editing an ACL on the S5720-HI, the implementation behavior is flawed and unfortunately exposes the network to a security breach. Due to the architecture of the switching resources, the Huawei 5720-HI switch “allowed” denied traffic to forward during an ACL edit. When edits are made, the switch completely removes the old Security Policy from its hardware resources, then reprograms the resources with the revised statements. Not only did this takes a long time, it left the network vulnerable.
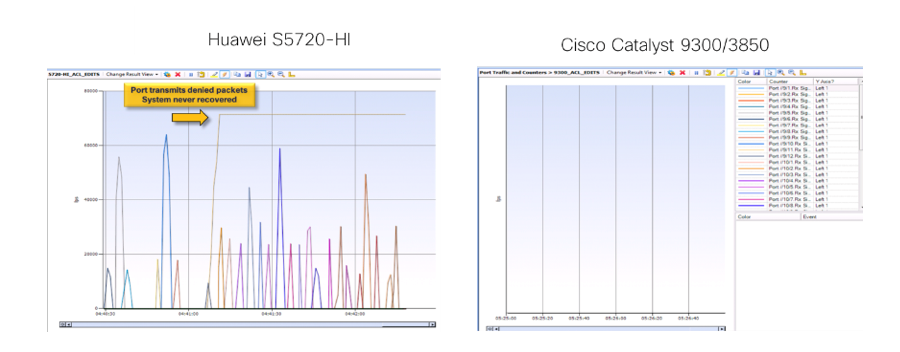
Miercom observed the S5720-HI allowed thousands of denied packets on every switch port. The Spirent system reported that, by the time the ACL change took effect on all ports on the Huawei switch, 70,000 packets had leaked through each switch port –more than 3.3 million packets that should have been blocked. This is a policy violation and creates a window of opportunity for a security breach.
The same set of tests were performed on the Catalyst 9300/3850 Series switches. The Catalyst 9300/3850 switching resources support high-speed policy edits (Adds/Deletes) with efficient resource allocation for scale, and secure implementation. With features such as “ACL Label-Sharing” and “Hitless ACL updates”, the switches demonstrated programming of policy to the network without being compromised. A table-stakes requirement for dynamic policy based automation.
An overlooked yet critical component to support this capability is the implementation of policy programmed in switching hardware. ACLs are one of the most basic mechanisms used for traffic classification. They can be used for multiple use cases such as multicast, QoS, and security. It is critical that modifying entries for a particular use case, does not affect other operational uses cases for customers. And more importantly, for the specific area of security, it is instrumental that non-permitted traffic is not accepted under any circumstance. While Cisco passed this test with great colors, Huawei failed to meet this important requirement.
Download the complete Miercom report here.








 How does Cisco and IDC have you covered?
How does Cisco and IDC have you covered?