Globally, mobile data usage and traffic are on the rise. As a result, mobile network operators (MNOs) are adjusting their offers and billing structures to accommodate user behaviors. More than a quarter of plans tracked in the third quarter of 2016 had allowances of 10 Gigabytes and above according to Ovum Informa Telecoms and Media. At the same time, Ovum tracked a smaller share of unlimited plans – a share that was small to begin with and was only 2% in 3Q16. And this figure may increase in 2017 with the reintroduction of unlimited plans in the US.
For several years, it seemed like the US mobile operators were steering clear from unlimited plans. It caught many industry experts by surprise when Verizon wireless brought back unlimited plans in February 2017, with the Verizon Unlimited offering. The offer includes HD video streaming, with 10GB of LTE data and unlimited 3G data after that for mobile hotspot usage. Industry watchers also doubted that Verizon’s move to join T-Mobile and Sprint in offering unlimited data would have a significant impact on the market. Very few anticipated that AT&T would extend its unlimited plan offer beyond its DirecTV customers – the only customers AT&T was offering unlimited data to at the time. However, within three days of Verizon’s unlimited offer announcement, AT&T’s new offer seemed to have a domino effect. A new price war ensued with T-Mobile and Sprint announcing similar unlimited data plans.
The fight over which cellphone carrier has the best unlimited data offering isn’t over. AT&T announced on March 12th that it is debuting two new unlimited plans this week — one, a no-frills option that tries to undercut its rivals on price; and the other, a more expensive plan with all the bells and whistles. The no frills $60 GoPhone plan offers 3 Mbps maximum wireless data speeds, doesn’t include Mobile Hotspot support. Reaching the 22 GB monthly data cap reduces download speeds to 128 Kbps for the rest of the monthly pay cycle. Stream Saver, AT&T’s mode for downscaling videos to 480p quality to use less bandwidth, is enabled by default. Meanwhile, T-Mobile increased its soft cap to 28 GB per month.
All of the plans offered have reduced speeds and deprioritization of traffic after reaching their soft cap (depending on plan details). All four carriers have soft caps that range from 22 GB to 28 GB per month. Bottom-line, there are limits – but not as costly to the customer as tiered plans once the caps are met.
Shared data plans and tiered plan offerings remain competitive in terms of price offerings but the impact of the reintroduction of unlimited plans on mobile traffic usage is yet to be seen.
Total global mobile data traffic is expected to grow to 49 exabytes per month by 2021, a seven- fold increase from 2016, according to the Cisco Visual Networking Index (VNI). Mobile data traffic will grow at a CAGR of 47 percent from 2016 to 2021.
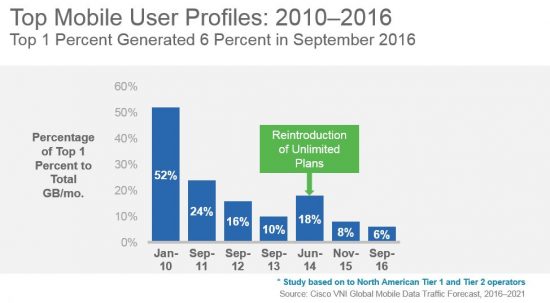
Operators have however historically managed to throttle heavy data users. As a part of the tiered pricing study within the Cisco VNI Forecast, the usage per month of the average top 1 percent of mobile data users has been steadily decreasing compared to that of overall usage. At the beginning of the 6-year study, 52 percent of the traffic was generated by the top 1 percent. With the reintroductions and promotions of unlimited plans by tier 2 operators in the study, the top 1 percent generated 18 percent of the overall traffic per month by June 2014. By September 2016, just 6 percent of the traffic was generated by the top 1 percent of users, showing that operators managed to mitigate the increase in traffic generated by the top 1 percent users.
This phenomenon has not spread beyond the US except in a few pockets around the world, but it is a hot topic of discussion. For example, this year in Malaysia, Webe offered a no-contract postpaid plan with unlimited data, voice, and text, aggressively priced at $18, as a competitive measure.
Similarly, in Taiwan, T Star differentiated on price and through unlimited data in order to gain market share. The three strong incumbents in Taiwan and a new challenger launched promotional unlimited LTE data plans in response.
In India, Reliance Jio announced (March 2017) an unlimited data plan with no daily data cap restrictions along with several other lower priced unlimited plans with daily data usage restrictions. In response, its competitors Airtel and Vodafone have offered other value-added services such as unlimited voice, doubling of data, etc.
After years of tapering growth, mobile data traffic growth in South Korea accelerated in 2016, largely due to unlimited plans (and inspite of broadly available Wi-Fi access).
It should be noted that mobile operators are continuing to offer tiered plans. These offers can be particularly differentiated at lower usage tiers (and lower price points) compared to the unlimited plans. This alternative remains attractive to some customers. Realistically, carriers can’t offer only unlimited data plans – that approach could oversubscribe mobile networks and overtax spectrum limitations. There is also the major consideration that increasing infrastructure costs require commensurate revenue uplifts for long-term sustainability and profitability. Wi-Fi continues to be a viable and in many cases necessary offload alternative for dual mode devices.
The high level of competition among established MNOs is expected to continue on many fronts. There is now also a wider pool of new competitors. Alternative communication technologies, such as instant messaging services that use data rather than traditional voice and text, are increasingly used by mobile consumers. So, what will be next for operators after the unlimited plans race and alternative communication technologies? With 5G on the horizon, I think we can expect more mobile makeovers in the future. The good news is that there should be something for everyone. From IoT applications to Tactile Internet experiences, creativity will be at the forefront. And hopefully, many of us will be able to afford tomorrow’s innovations.









 This post was written by guest blogger Erin Connor, Portfolio Manager for Critical Human Needs, Cisco Corporate Affairs and Cisco Foundation
This post was written by guest blogger Erin Connor, Portfolio Manager for Critical Human Needs, Cisco Corporate Affairs and Cisco Foundation