[Blog authored by Aaron Weis and Samuel Wigley]
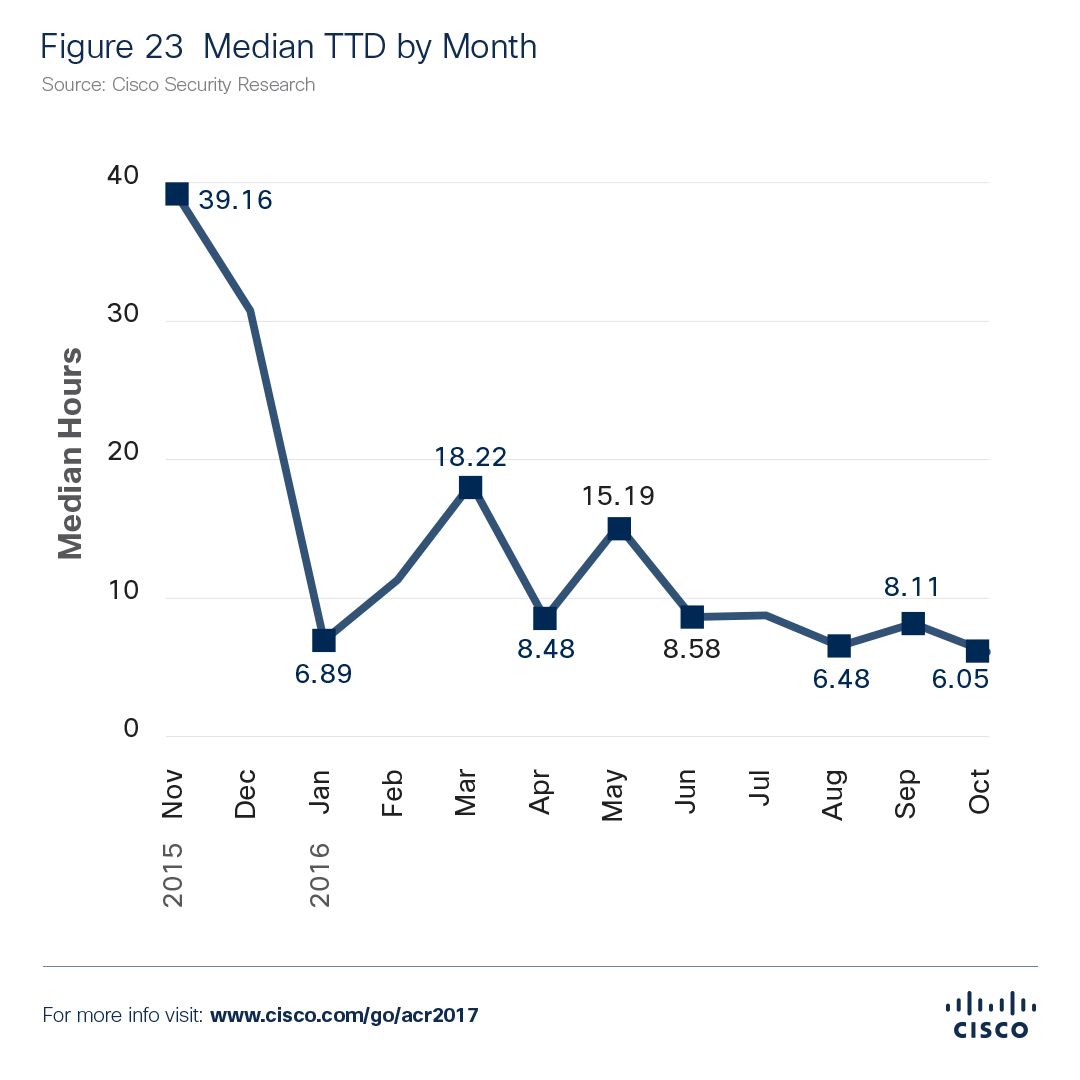
Cisco has been measuring our security products’ median “time to detection” (TTD) — the window of time between a compromise and detection of a threat — since 2015. This exercise is a way for us to benchmark our progress, and continually refine our approach, to detecting threats.
Tracking TTD over time also helps to highlight the constant struggle between defenders and adversaries (see chart below). When adversaries launch new threats, the median TTD increases. Declines in TTD indicate points when security researchers have gained the upper hand.
Cybercriminals use various obfuscation techniques to keep their malware strong and profitable. That means many of the “new” threats that researchers encounter are actually fresh versions of old and known threats. To better understand how adversaries help malware to evade detection and continue to compromise users and systems, we sought to measure “time to evolve” (TTE). This research is highlighted in the Cisco 2017 Annual Cybersecurity Report. From November 2015 through October 2016, we closely examined a select group of well-known malware families to see how adversaries employ two specific tactics: evolving payload delivery types and quickly generating new files (to defeat hash-only detection methods). Our threat researchers looked for changes in file extensions delivering the malware and analyzed the file content (or MIME) type as defined by a user’s system.
By analyzing web attack data from various Cisco sources — web proxy data, cloud and endpoint advanced malware products, and composite antimalware engines — we can measure the time it takes adversaries to change the way specific malware is delivered. We can also measure the length of time between each change in tactics.
For each malware family included in our study, we examined patterns in both web and email delivery methods. We also tracked the ages of unique hashes associated with each family to determine how quickly adversaries are creating new files. Through our research, we learned that:
- Each malware family has a unique pattern of evolution
- The examined ransomware families appear to have a similar rotation of new binaries
- Some malware families employ only a handful of file delivery methods; others use 10 or more
- Adversaries tend to use effective binaries over long periods
- Frequent file changes indicate that malware authors are under pressure to switch tactics
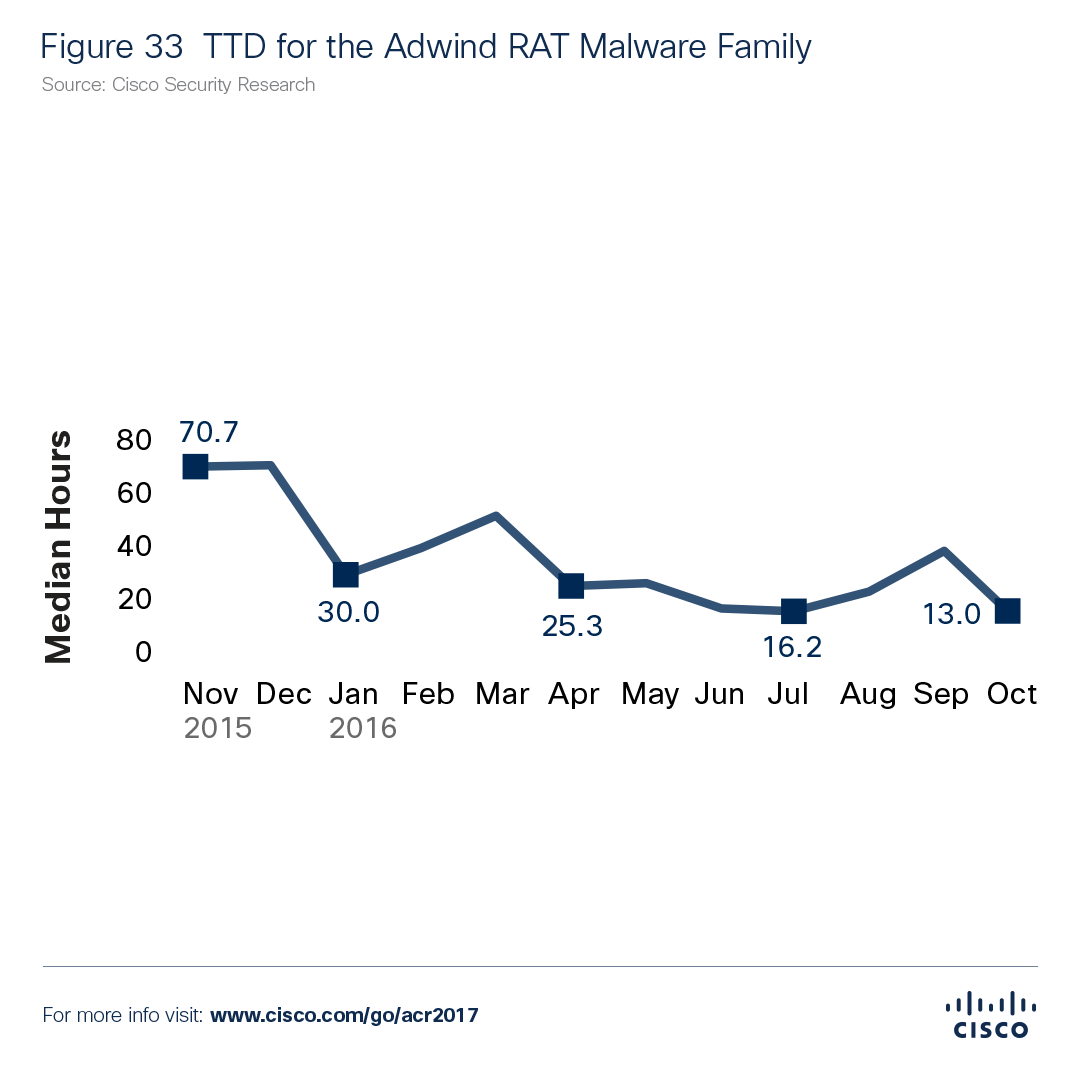
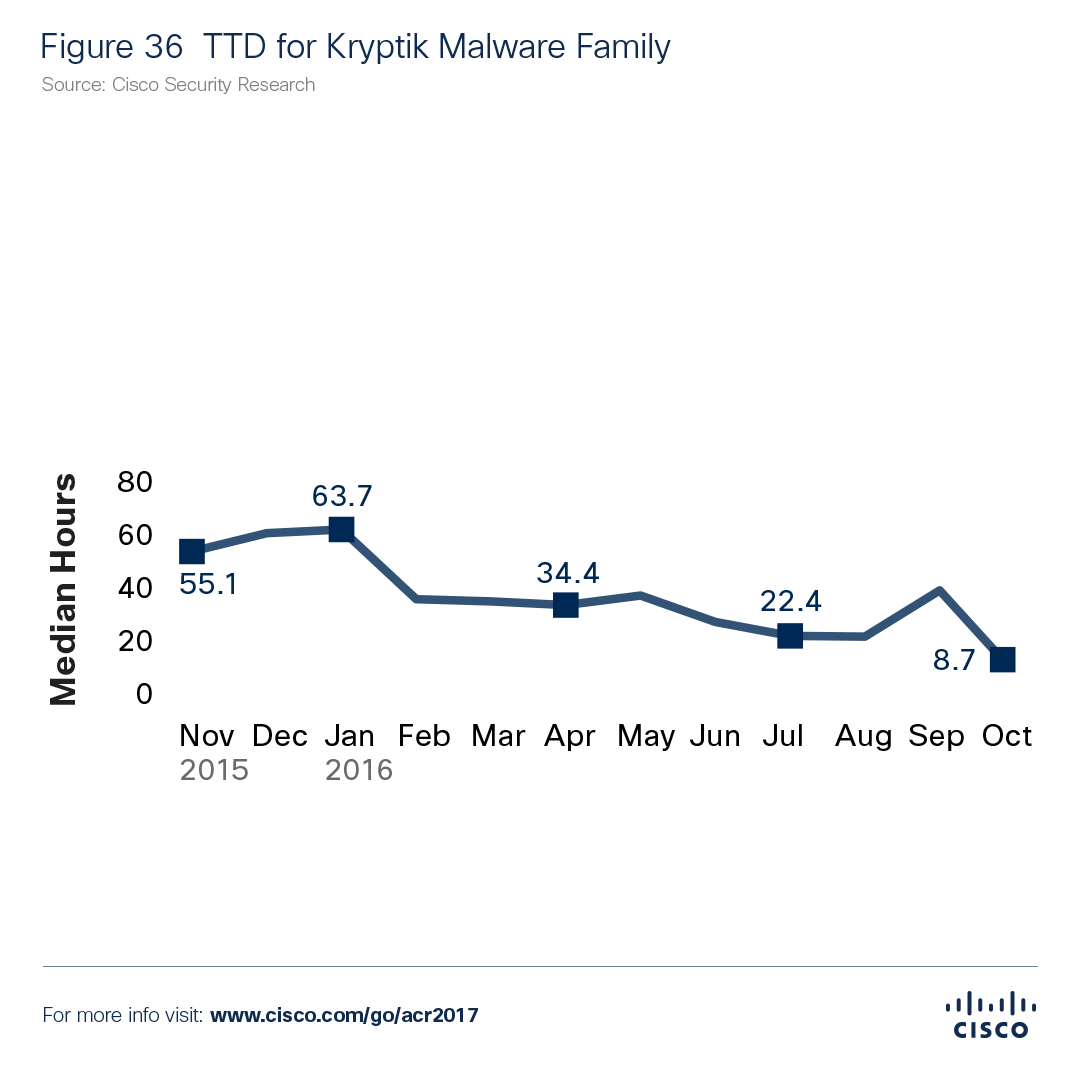
Two of the malware families included in our research were Adwind RAT and Kryptik. Our researchers found that these two families had a consistently higher median TTD than the other families we analyzed. In addition, they have a greater mix of file ages compared to other families in the study. This suggests that adversaries reuse effective binaries that they know are difficult to detect.
However, as the charts below illustrate, by October 2016 Cisco products were detecting both malware types within 14 hours: Adwind RAT (13 hours) and Kryptik (about 9 hours). (Note that Cisco’s overall median TTD for the period from November 2015 to October 2016 was 14 hours.)
Our research also showed that Dridex, a once-popular banking Trojan, was fading. In late 2016, we observed that detection volume for Dridex had declined, as did development of new binaries to deliver this malware. Near the beginning of this year, Dridex was seen re-emerging with a new variant in the wild leveraging a new code injection method dubbed AtomBombing. This reinforces that malware authors monitor their effectiveness to evade detection to maximize profits and will devote resources towards evolving their malware.
This research offers a glimpse into two ways that attackers’ shift their methods to evade detection, but the landscape is complex and ever-changing with many opportunities for attackers to shift methods. In order to stay ahead, or at least keep pace with attackers, organizations need integrated security architecture that is open and automated to allow their defenses to communicate to provide real-time insight into today’s threats and ensure quick detection and remediation.
Download the Cisco 2017 Annual Cybersecurity Report to learn more about our research into TTE and other security topics.