I always admired creative minds who have the insight to change the game based on data, intuition and strong conviction. This is almost expected in technology and entertainment fields. But not in manufacturing. However, there is no shortage of data coming from machines in a modern factory. But being able to analyze and act on the massive data streams from hundreds of factory-floor machines is the big challenge. The right data at the right time will drive big efficiencies and open up new capabilities in manufacturing. It will speed up new product introduction, help with real-time optimization, increase worker productivity, and give customers the ability to track a product from start to finish across the supply chain. This new model for manufacturing is called the digital factory, made possible by quickly transforming data into insights and act upon them.

In recent months, I have met many of our manufacturing customers, including Campofrio Food Group, to discuss how they view the manufacturing plant of the future. The key message I heard is that manufacturing customers are most concerned about security risks, system complexity, and legacy systems that lack automation and intelligence necessary to achieving their smart manufacturing objectives.
Today at Hannover Messe, we are announcing Cisco Connected Factory for Industrie 4.0 to address these key obstacles.
We focus on three core values:
- Simplicity: New tools like Industrial Network Director make managing your plant floor network easy for operations.
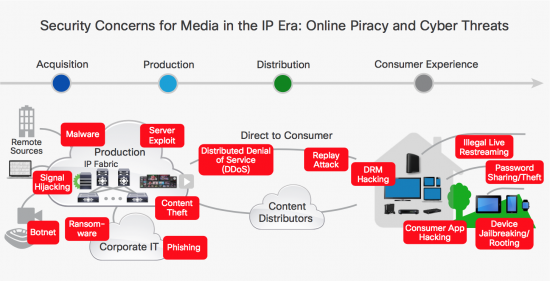
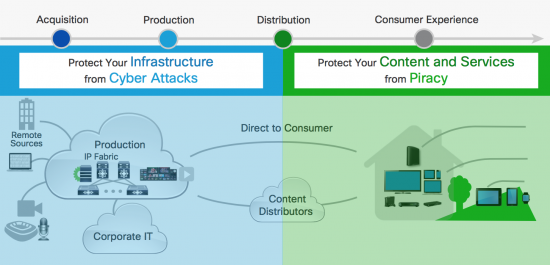
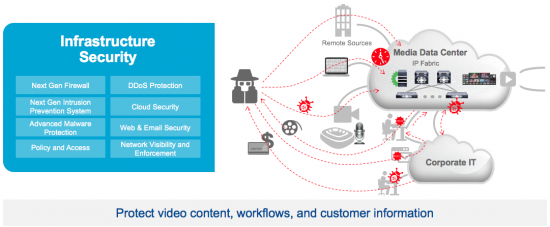
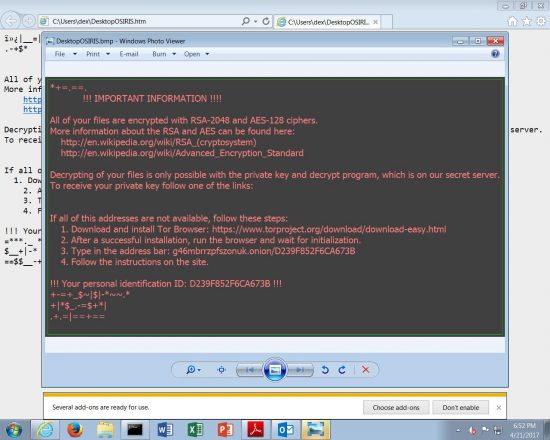
- Security: Cisco’s comprehensive security solutions help you secure your IP and protect production integrity.
- Intelligence: We get your plant data to the right people at the right time, and we provide the tools to manage your network effectively. The more you know, the faster you can act.
Three new solutions enhance the Connected Factory portfolio, powered by our Digital Network Architecture (DNA):
1. Time Sensitive Networking on the IE4000 Switch family: We support a new standard on our switches to better protect your data and make sure your mission-critical applications are running smoothly on a single, unified Industrial Ethernet network. We are reinventing Industrial Ethernet for the factory floor, built to be compatible with the new applications of tomorrow.
2. Cisco Connected Asset Manager for IoT Intelligence: This is not just another data visualization platform – it can mine data from a variety of sources and bring them together in the plant across legacy systems. Reporting is simple – just drag and drop data in a user-friendly interface designed for business users, not programmers.
https://youtu.be/iOOGanHzejQ
3. Cisco Industrial Network Director: Gives factories full visibility of their plant network, allowing easier set-up and less downtime. It offers true plug-and-play functionality and is made with operators in mind, not just IT. Once you install your managed switch, you’ll enjoy the benefit of built-in security, settings, and functionality. No manual programming required.
https://youtu.be/ytAKMxkXSNA
I believe that we are just scratching the surface on the possibilities around gathering new insights from production data, and helping manufacturers on their Industrie 4.0 journey. These newly available insights, combined with automation and security open up great new opportunities to innovate in manufacturing.
This is the time of the creative minds who can re-imagine manufacturing to take advantage of the new solutions to get ahead.
To start your Industrie 4.0 journey, check out our Digital Manufacturing website or our Industrie 4.0 e-Book.