This post was authored by Nick Biasini
Throughout the majority of 2016, Locky was the dominant ransomware in the threat landscape. It was an early pioneer when it came to using scripting formats Windows hosts would natively handle, like .js, .wsf, and .hta. These scripting formats acted as a vehicle to deliver the payload via email campaigns. However, late in 2016 Locky distribution declined dramatically largely due to the slowdown of Necurs that occurred at the same time.
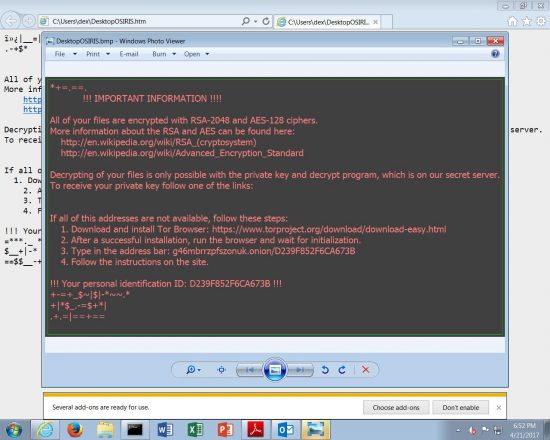
On April 21st, Talos observed the first large scale Locky campaign in months from Necurs. This campaign leveraged techniques associated with a recent Dridex campaign and is currently being distributed in very high volumes. Talos has seen in excess of 35K emails in the last several hours associated with this newest wave of Locky. This large wave of distribution has been attributed to the Necurs botnet which, until recently, had been focused on more traditional spam such as pump-and-dump spam, Russian dating spam, and work-from-home spam.