Digitization and APIs
Before we get into digitization, let’s discuss disruption. As we all know, Blockbuster was disrupted by… Netflix; and the taxi business is being disrupted by Uber as we speak. If we look deeper, Netflix and Uber essentially streamlined processes through digitization, and hence disrupted their industries. These are two examples of disruption via digitization that I hope we can all relate to. Digitization is constantly happening all around us, and Cisco and several of our partners are helping customers to digitize their processes.
In the DevNet Zone at Cisco Live, I hosted a lively panel discussion with 4 of our partners to discuss how the various technologies from Cisco are helping them drive digital transformation with their customers. Let me briefly introduce the panelists who joined me:
- Craig Sanderson, Senior Director at Infoblox, leading provider of security and network control solutions.
- Russell Wiant, VP of Product, Nectar Services Corp, enabling seamless communication across the network.
- Chris Gaun, Director of Strategy, Apprenda, Enterprise PaaS solution provider.
- Jose Bogarín, Chief Innovation Officer, Altus Consulting, helping customers reduce their IT costs.
Enabling Adaptive Network Control with Cisco pxGrid and Infoblox
In the discussion with Craig, he shared that Infoblox partnered with Cisco to help customers with an automated response to a variety of security threat-related events. He emphasized that “Threat intelligence sharing helps in rapidly closing the gap between detection and response.”
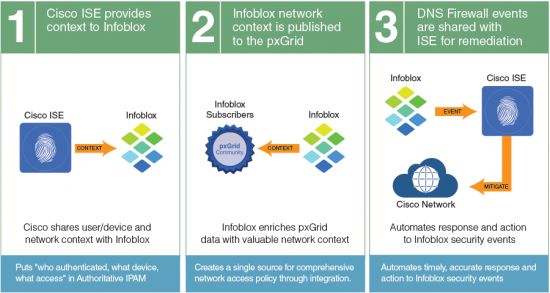
Cisco’s pxGrid, a data exchange platform, provides a publish/subscribe model that eliminates the need for point-to-point integration between the various security products a customer might have. Infoblox and Cisco ISE integration utilizes the Cisco pxGrid to exchange information between Cisco ISE, Infoblox, and other pxGrid participants, for a unified and automated solution.
Craig further explained that pxGrid APIs help Cisco ISE share the user, device and network context. At the same time, the pxGrid APIs help Infoblox share the DHCP and IPAM (IP address management) context. Based on the combined context, Cisco ISE is then able to automate a security response, such as quarantining an endpoint.
Optimizing Unified Communication Experiences with Cisco DNA and Nectar
Next, Russell joined me from Nectar, where they help customers to have seamless voice and video communication between any two endpoints, be they wired or wireless. During a video communication, have you ever seen a message saying “the call is experiencing quality issues due to the network,” or something along those lines? The reality is that several factors could be compromising the experience, such as network bandwidth and latency, server performance, and configuration issues .
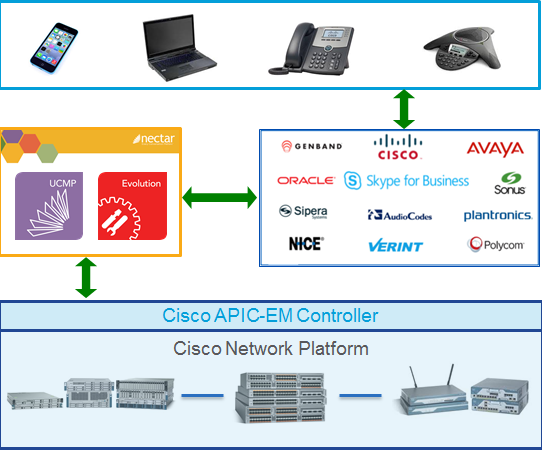
Russell shared that Nectar provides monitoring capabilities with its Unified Communications Management Platform (UCMP) solution, which help identify where communication problems are occurring. In addition, the recently launched Nectar Evolution provides the means to set the appropriate QoS settings to correct the problem. Nectar Evolution learns about UC events in real time and communicates them to the APIC-EM controller from Cisco using corresponding APIs. This intelligence, when given to the APIC-EM, enables it to configure the network dynamically with the right prioritization and capacity needed for the two endpoints to communicate effectively.
Building a secure PaaS with Cisco ACI and Apprenda
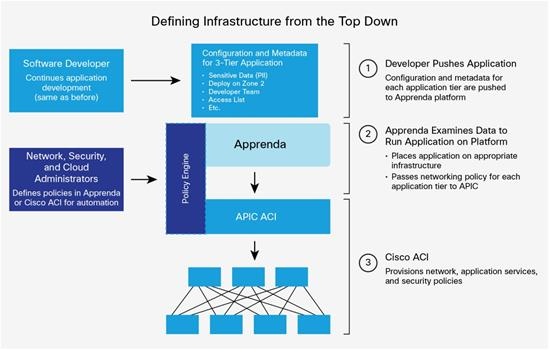
I also had the pleasure of having Chris join us from Apprenda. He shared with the audience how they are using Cisco’s Application Centric Infrastructure (ACI) to provide a “secure PaaS” offering to their customers.
Chris explained that developers are responsible for hosting or making changes to their applications on Apprenda. They need not be aware of the underlying network or infrastructure architecture, which is abstracted by the Apprenda platform, to do their jobs — the platform takes care of those details. When the developer is ready to host the application on the platform, the developer defines information about the application, such as whether it includes personally identifiable information (PII). This definition creates policy information about the application. The Apprenda platform passes that policy information from the application configuration file and metadata to Cisco ACI.
Cisco ACI then stores that policy in the Cisco Application Policy Infrastructure Controller (APIC), creating the rule book that determines which applications (or tiers or arbitrary groups of endpoints) can talk to each other. The Cisco APIC pushes the policy down to the individual Cisco Nexus® 9000 Series Switches in the fabric, which implement the required networking rules for the application architecture.
The result is a secure, policy-based hybrid cloud application platform that helps you achieve the dynamic isolation of application tiers, including data and network, without a dedicated infrastructure. Apprenda also integrates with Cisco Metapod to enhance the provisioning of infrastructure services. Together, Cisco and Apprenda provide the best possible way for enterprises to drive governance, security, rapid development, high service levels and order-of-magnitude savings in operational and capital expenses.
Allowing business users to configure Cisco Contact Center securely with Altus Contact Center Manager
Jose joined me to share how his company’s solution is able to help their customers automate the tasks within Cisco Contact Center Express. Tasks that previously took days can now be done in minutes, freeing up time for the end user and IT administrator to focus on activities with more business value.
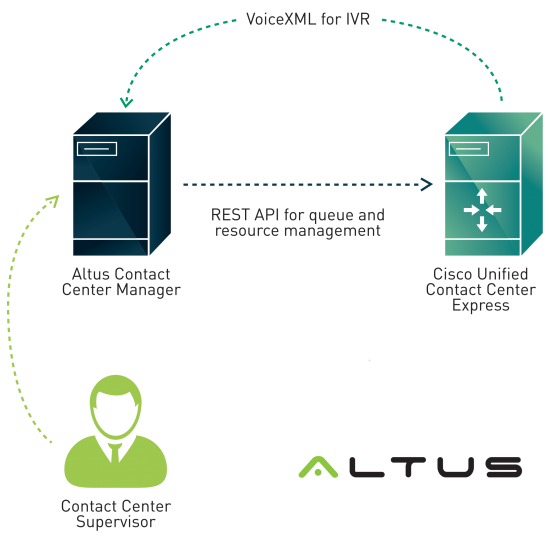
Jose’s organization, Altus, developed Altus Contact Center Manager (ACCM), a software solution that uses APIs to integrate UCCX and provide an easy-to-use interface that allows the end user to configure it.
ACCM enables business users of Cisco Contact Center Express to make configuration changes in the IVR, CSQs (contact service queue) or other agents, without having to go through IT.
In most cases, IT would have to open a support ticket with their Cisco Partner in order to make such changes. Jose mentioned that, “if you take into consideration having to go through two help desks in order to make a simple configuration change, like a greeting audio or an agent skill, our software allows to do in five minutes something that right now may take two or three days to solve.”
Begin your journey towards Digital Transformation
It is amazing to see how these partners have leveraged Cisco technologies, and how their innovations work to digitize various processes: threat detection and response, network automation for seamless communication, security policy propagation via an application to the network, and quickly enabling changes to the contact center. Cisco DevNet played a key role in helping our partners learn how to use the various APIs and test their applications in our sandbox.
As you can tell, there has never been a better time for Digital Transformation with Cisco DevNet!






 It is correct that we are currently partnered with four service providers to provide SD-WANs, to their business customers.
It is correct that we are currently partnered with four service providers to provide SD-WANs, to their business customers.