Meet Derek: the man, the myth, the legend. As deputy CIO and the CTO, he is tasked with the overall technology strategy and oversees day-to-day operations for infrastructure, enterprise apps and research computing teams at the University of Arizona. By 5pm, he is enjoying the finer things in life like his scotch, the walking dead, or hiking with his 2 sons.
Although you just met him, something tells me you can relate to his perils. See Derek loves the agility and flexibility cloud delivers. However, he found himself restless and anxious at night. To Derek, cloud is safe if used properly. But when he isn’t enjoying zombie battles, he is battling cloud sprawl in his day-to-day. A lack of visibility into how and what his constituents are doing in the cloud. See he was in the dark about his stakeholders. Ironically, Shadow IT not only operates in the shadows, but put Derek in the dark about his own users.
- What data was in the cloud and how were his users storing it?
- How much Cloud sprawl existed?
- How much were we spending?
These are all questions Derek and many CXOs wonder.
So we sat down with Derek for a quick Q&A. 10 Questions. Unfiltered. One CTO and his journey to squash cloud sprawl and minimize the risk of Shadow IT.
Quick shameless plug: if you want to learn more about managing the risk of Shadow IT, cloud sprawl, and implementing cloud governance attend our: Shadow IT and Cloud Governance Webinar Series
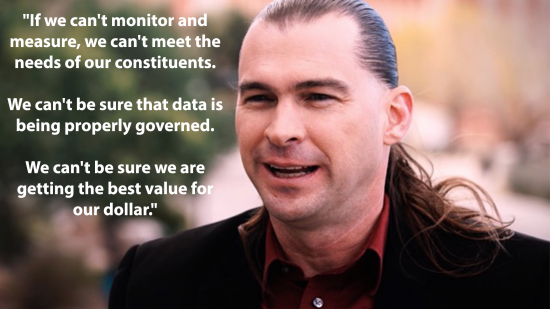
Derek Masseth: CTO and Deputy CIO at the University of Arizona
Q: Derek What’s your charter at UoA?
“Our goal is delivering the right IT service at the right Time to facilitate teaching, research, and learning. Whether big Data, connectivity, or cloud services to all our constituents.”
Q: How do view the cloud?
“Driving agility and flexibility into IT, that’s what cloud is about to me.”
Q: Previously you mentioned anxiety. What specifically gave you anxiety as CTO about cloud sprawl?
“The bulk of the anxiety that we felt in IT was around privacy, regulatory concern, and the security of data getting out in ways that were endorsed…
The cloud can be quite secure, as long as the provider and consumer are leveraging it with the right controls. Ensuring the controls exist is where we focused to minimize the bulk of our exposure.”
Q: Why did you decide to implement multi-cloud governance?
“If we can’t monitor and measure, we can’t meet the needs of our constituents. We can’t be sure that data is being properly governed. We can’t be sure we are getting the best value for our dollar.”
Q: Elaborate on what you mean by cloud sprawl?
“Cloud sprawl is the condition where multiple cloud providers are leveraged for fundamentally the same service. That leads to waste since there is overhead. Our goal was to drive costs down and ensures that there were proper controls…
(Cloud Sprawl) is incredibly inefficient. And efficiency in IT and everything in Higher Ed is important, particularly with IT as a cost center. IT must be very efficient in delivery of its service. We knew sprawl existed, driven by individual consumption of cloud services. And we knew we could do better.”
Q: So what did you do?
We knew we had all this cloud sprawl, but didn’t know what to do about. We heard about Cisco Cloud Consumption Assessment, and it seemed to really fit the bill.”
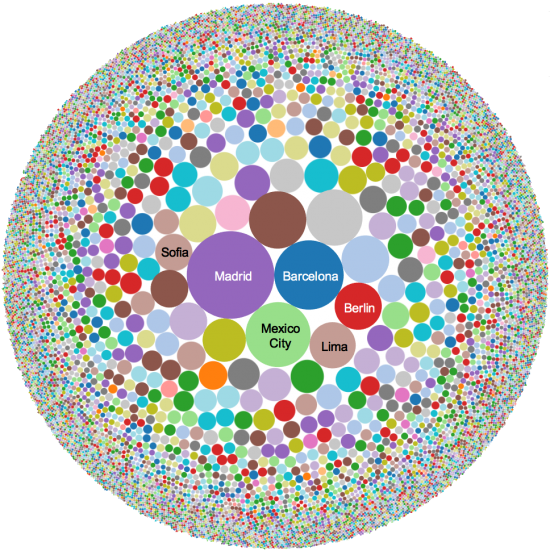
Q: So what sprawl did you find?
“We went into the cloud discovery process thinking we had 50 cloud services. A few weeks later, we found 900 cloud services being used! The amount of overlap was astonishing. We knew we would find sprawl but at 50 it’s sprawl, at 900?!!! It’s more than that! What’s more than sprawl right? It gave us insight into how our constituents were using the cloud more than we could have anticipated.
Cloud Consumption Service told us that IaaS was wildy the most popular service being consumed. So that was the thing we needed to address.”
Q: You said IaaS was wildly the most popular use case, how did you meet the IaaS needs of your users?
“The value of Cisco metapod is we tried to build and deliver private cloud functionality prior, and it’s hard! We selected Cisco Metapod for our Private Cloud because it delivered public cloud functionality, in our facility in a manner that we dont have to manage. The beauty of public cloud is not having to manage the infrastructure. The notion that I can get that in my data center without having to buildup and maintain the staff involved with building private cloud infrastructure is amazing.”
We selected Cisco Metapod for our Private Cloud because it delivered public cloud functionality, in our facility in a manner that we dont have to manage. The beauty of public cloud is not having to manage the infrastructure. The notion that I can get that in my data center without having to buildup and maintain the staff involved with building private cloud infrastructure is amazing.”
Q: What results have you seen since using Cloud Consumption Service?
“The results have been an ability to focus efforts where our staff needs us. Insights into how cloud is used at UoA has been invaluable in directing our efforts for cloud adoption. Because IT has been given insight on what matter most in cloud to our constituents. The ability to focus has enabled us to deliver high-value services where and when they are needed most!”
Q: What advice do you have for fellow CIOs and CTOs?
“If I had any advice, if you’re experiencing anxiety or need to get handle on cloud sprawl, services like Cisco Cloud Consumption Service provide the visibility you need to focus your efforts in an area that is difficult to navigate…. I talk about visibility and the ability to focus, but what that does too, is it drives up our confidence level. Now we can make sure we are doing the right thing at the right time.
Now I can turn on dime, and I couldn’t do that before.”
If you would like to learn more about Cisco Cloud Consumption Service please visit our site. You can register for a Free Shadow IT Risk Assesment with our SaaS, analyzing up to 1 million records across 150+ risk parameters.