This blog post was guest-written by Kimberly Bowman, Marketing and Communications  Specialist, Cisco Community Relations.
Specialist, Cisco Community Relations.
It is the start of the annual holiday season. In the United States, we have a day for getting deals (Black Friday), a day to support local businesses (Small Business Saturday), and a day to buy goodies while shopping online (Cyber Monday).
Then, we have #GivingTuesday — celebrated annually the first Tuesday after the Thanksgiving holiday — a day for “doing good” through the power of social media and collaboration. In its fifth year, #GivingTuesday is becoming a global phenomenon among philanthropists and techies alike.
In a day and age where social media allows you to connect with old and new friends, give updates on daily routines, and keep tabs on your favorite celebrities, Cisco will use that power to “do good” on #GivingTuesday.
As part of our Be the Bridge: Annual Giving Campaign, we will use our corporate social media handles on Twitter, Instagram, Facebook and Snapchat to highlight the good work of over 20 of Cisco’s nonprofit community partners in local communities around the world. We’ll be providing our employees and our social media following the opportunity to “Be the Bridge” to these organizations.
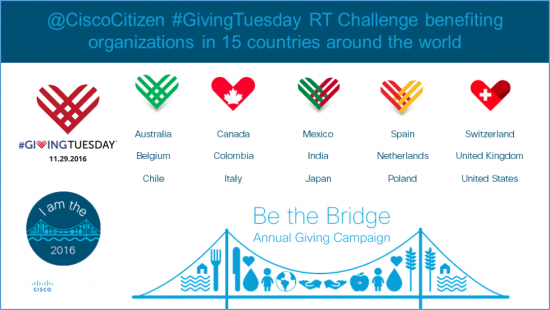
Starting with Australia, moving from East to West and ending in the US, we’ll release a tweet acknowledging the donations from our employees around the world. For every retweet, whether it’s from an employee or anyone else on Twitter, we’ll donate an additional $1 to those organizations, up to $10,000 (aggregate total contribution for all participating organizations). The retweet challenge closes at 6 p.m. local time in all markets.
The locations listed below reflect areas where Cisco has a presence and employee base. The nonprofits were selected based on employee donation trends in the past, and a genuine need for amplification of the great work that happens in local communities around the world. If you retweet this blog post, we’ll split all funds generated equally among these 26 organizations!
Location |
Organization |
| Australia | Special Olympics Australia – @SOAustralia |
| Belgium | Restos du coeur – @Restoducoeur |
| Canada | Daily Bread Food Bank – @DailyBreadTO |
| Chile | Red de Alimentos – @RedAlimentos |
| Colombia | Colombianitos – @colombianitos |
| India | Akshaya Patra – @AkshayaPatra |
| Italy | Attento a te – @AssAttentoAte |
| Japan | Class for Everyone – @class4every1 |
| Mexico | Un Kilo de Ayuda A.C. – @Unkilodeayuda |
| Netherlands | Habitat Nederland – @HabitatNL |
| Poland | Polish Humanitarian Action (Polska Akcja Humanitarna) – @PAH_org |
| Spain | Apsuria (Fundacion Apsuria) – @apsuriafunda |
| Switzerland | Save the Children Switzerland – @STC_Schweiz |
| United Kingdom | Mary’s Meals – @MarysMeals |
U.S. Location |
Organization |
| Austin, Texas | Caritas of Austin – @caritasofaustin |
| Carmel, Indiana | Gleaners Foodbank – @GleanersFBIndy |
| Chicago, Illinois | Northern Illinois Food Bank – @ILfoodbank |
| D.C. Metro | Miriam’s Kitchen – @miriamskitchen |
| Greater Atlanta, Georgia | Partnership Against Domestic Violence @PADVAtlanta |
| Greater Atlanta, Georgia | Atlanta Community Food Bank @ACFB |
| RTP, North Carolina | Special Olympics North Carolina – @SONC_BeAFan |
| RTP, North Carolina | YMCA of the Triangle – @YMCATriangle |
| Boxborough, Massachusetts | Habitat for Humanity of Greater Lowell – @LowellHabitat |
| San Jose, California | Spark Mentoring Program – @SparkProgramSF |
| San Jose, California | The Tech Museum of Innovation – @TheTechMuseum |
| Seattle, Washington | Northwest Harvest – E.M.M. – @NWHarvest |
Now through December 16, we hope to inspire thousands of employees worldwide to support the cause of their choice, and together, raise more than $5 million in donations and matching funds through our Be the Bridge: Annual Giving Campaign.
Join us in spreading the word by using social media to let the world know how you are “being the bridge.” Share your stories by using the #BeTheBridge and #WeAreCisco hashtags and inspire others by posting to the Cisco CSR Facebook page.
If you’re a Cisco employee and want to donate or volunteer, visit our internal Annual Giving Campaign community and learn how you can start making a difference locally or globally today.