It’s been a year since I wrote this blog detailing our software innovations aimed at helping Service Providers address the ever-increasing challenges imposed by digitization. IOS XR for cloud-scale networking has really taken flight since then and I am proud to share with you some highlights from the journey thus far.
Our strategy is essentially to simplify networking in terms of its operations, usage and ability to support more innovation.
That starts with the foundational layer – offering best Silicon choice that support fixed and modular form factors, the right silicon diversity across in-house and merchant silicon and flexibility of HW consumption with different scale points. So with this in mind, we built the best hardware that supports our innovation and delivers the right price/performance ratio.
I am particularly proud that this richness of portfolio does not come at the expense of feature sets and operational consistency. All these platforms are powered by a single, scalable software paradigm – IOS XR.
Cloud-scale enhancements to IOS XR – ruthless automation, visibility and control, simplification and open innovation – bring you significant operational improvements across your entire network infrastructure. We are thus able to offer customers the flexibility and agility to deploy the right hardware depending on their place in the network architecture.
In that respect, we’ve seen many customers embracing cloud-scale networking and using our equipment to satisfy different business contexts. From interconnecting data centers with highly-scalable routing platforms to dense 100G aggregation applications for content and caching infrastructure to transforming traditional central office with scaled-out infrastructure to support the virtualization of services.
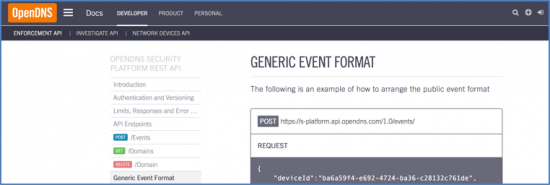
XR’s model-driven programmability is built on data models that are expressed in a variety of YANG models – industry driven OpenConfig models as well as standards driven IETF models. With a paradigm of any data model (Native, OpenConfig, IETF), any encoding (XML, JSON), and any transport (NetConf, RestConf, gRPC), our Operating System is very adaptive to your operational environment. In the last year, we have tripled the number of OpenConfig models we support and increased the number of XR native models by roughly 50%. Furthermore, we introduced model-driven APIs to simplify the adoption of data models and made them available to the larger community as an open source project. We are not stopping here. We remain committed to offering the most comprehensive set of data models along with model-driven APIs and tools to accelerate the adoption of software automation.
Model-driven telemetry is another critical area we are furthering the agenda on. Telemetry exports critical state and statistics from your infrastructure. Model-driven telemetry does that many times faster than traditional monitoring technologies, providing deep insights into the real-time operation of the network. The system is also fully configurable using telemetry YANG models. I would like to share an interesting customer use case: within two weeks of deploying model-driven telemetry in production, one customer turned off SNMP because they didn’t need it any longer! Model-driven telemetry provided the mission-critical network data at a higher frequency, in a more automation-friendly format, with less load on the network. With programmability and telemetry combined, the network definitely moves into a self-driving mode.
The final innovation I want to list is application hosting that gives customers a platform for leveraging their own tools and utilities. The transition of IOS-XR from 32-bit QNX to 64-bit Linux paved the way for better integration with industry-standard DevOps tools, furthering our goal to “automate everything”. Support for containers in an LXC or Docker format along with the ability to run custom apps and scripts natively to manage the box, enabled our customers to be more flexible in the way they operationalize their network. Further, to deepen our ties with the Open Source DevOps community, we released support for configuration management tools like Ansible, Puppet and Chef, with more modules coming up in the future. As we release an IOS-XR vagrant box on a bi-weekly basis, we expect the developer community to grow even stronger and make IOS-XR the leading platform for DevOps integrations in the routing space. With the application hosting toolbox, customers can now truly extend the capabilities of their network infrastructure.
Fundamentally, I am proud of the work we have accomplished with XR and would like to thank every team member, customer and partner who has accompanied us on this journey. Cloud-scale Networking gives you the operational efficiency, flexibility and openness to equip your network for being a transformative engine for the digital age. We are pushing the limits of networking excellence and we invite you to join us on this journey.
For more information download this ebook.


 In the spring of 2016, Germany reached the milestone of providing almost all of its energy needs from wind and solar power at least for part of the day. Portugal ran four days entirely on renewable power. Denmark set similar records. Wind power has increasingly been a key component of energy strategy for many countries driven by their carbon footprint and sustainable development initiatives. A wind farm is a perfect example of a sophisticated and highly complex IoT system in action that incorporates all four
In the spring of 2016, Germany reached the milestone of providing almost all of its energy needs from wind and solar power at least for part of the day. Portugal ran four days entirely on renewable power. Denmark set similar records. Wind power has increasingly been a key component of energy strategy for many countries driven by their carbon footprint and sustainable development initiatives. A wind farm is a perfect example of a sophisticated and highly complex IoT system in action that incorporates all four  We’ve talked about how Cisco is helping network operators leverage the tools of the data center to better manage the network. To show a real world example of this a few weeks back Cisco and Ansible teamed up for SDx Demo Friday. We showed how to manage large-scale networks using Cisco IOS XR application hosting infrastructure and Ansible version 2.2.
We’ve talked about how Cisco is helping network operators leverage the tools of the data center to better manage the network. To show a real world example of this a few weeks back Cisco and Ansible teamed up for SDx Demo Friday. We showed how to manage large-scale networks using Cisco IOS XR application hosting infrastructure and Ansible version 2.2.
![RAS Blog Kali Alphonsine[1]](https://blogs.cisco.com/gcs/ciscoblogs/1/RAS-Blog-Kali-Alphonsine1-300x400.jpg)

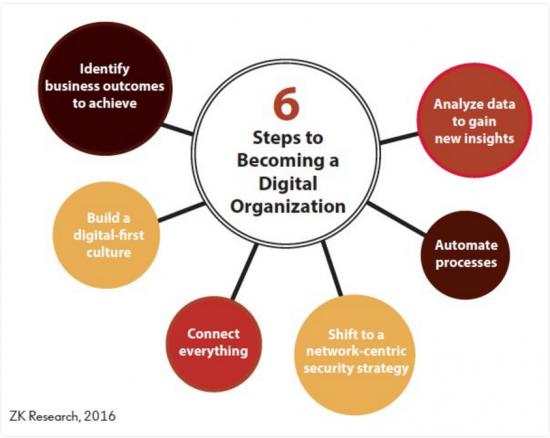 According to ZK Research, there are 3 primary drivers of digital transformation: transform business models, create new customer experiences, and empower workforce innovation. These drivers all require a much higher level of business agility. Software is much more dynamic and agile than hardware, so it better enables digital transformation.
According to ZK Research, there are 3 primary drivers of digital transformation: transform business models, create new customer experiences, and empower workforce innovation. These drivers all require a much higher level of business agility. Software is much more dynamic and agile than hardware, so it better enables digital transformation.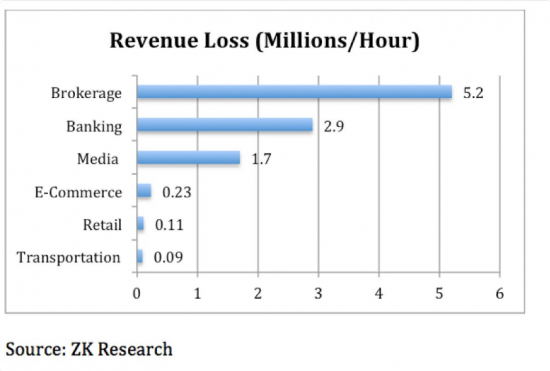 Downtime not only costs money, but also can damage a company’s brand reputation and cause customers to churn. If a company is bleeding customers, in the end the amount of money lost doesn’t really matter. The bottom line is that downtime can be catastrophic, so have the right software support in place to minimize the risks of downtime.
Downtime not only costs money, but also can damage a company’s brand reputation and cause customers to churn. If a company is bleeding customers, in the end the amount of money lost doesn’t really matter. The bottom line is that downtime can be catastrophic, so have the right software support in place to minimize the risks of downtime.