Just a month ago, I was at OpenStack summit Austin presenting Cisco technologies to our valuable customers. To me it was quite obvious that OpenStack has hit mainstream, particularly after listening to Gartner’s keynote. The keynote emphasized how customers are adopting Cloud and OpenStack operationally. I also observed that there was great interest among customers and operators in OpenStack use cases like NFV, private and public cloud. Containers, in particular, were a hot topic, and it came as no surprise given the mode1-mode2 transition evident in many enterprises.

Time flies fast and Red Hat summit 2016, San Francisco, is fast approaching. I will be carrying pleasant memories and experiences from OpenStack summit to this event looking for a synergistic continuation of the excitement and learning. So what is Cisco doing at Red Hat 2016? I am pleased to inform you that Cisco has several key insertions from keynotes to breakouts and theater sessions featuring ACI, UCSO/Metapod and NFVI technologies at the Red Hat summit.
Cisco CTO David Ward will discuss in his keynote, the key shifts and importance of open source, open communities and collaborative development in building out the next generation of data centers. From investments in open source foundations and in projects hosted on GitHub, Dave will dive into the ones he sees as leading the forefront of innovation – and why these technologies need to be built in the open for a better, more effective data center.
Following Dave’s keynote are the breakouts, and our breakout sessions at the summit are meticulously aligned with current trends and customer care-abouts in the context of Red Hat OpenStack. Infrastructure managers are constantly asked to push the envelope in how they deliver cloud environments. In addition to speed, scale, and flexibility, they are increasingly focused on both security and operational management and visibility as adoption increases within their Organizations. Mike Cohen, an industry-recognized open source contributor and Networking expert, brings valuable insights via his breakout session titled “Running A policy-based cloud with Cisco Application Centric Infrastructure, Red Hat OpenStack, and Project Contiv.” The session covers how Cisco and Red Hat are partnering together to deliver policy-based cloud solutions to address the afore-mentioned challenges.
Mike will discuss how Cisco and Red Hat are collaborating in the open source community and building products that serve as proof-points for this collaboration. It will cover topics including:
* Group-Based Policy for OpenStack
* Cisco Application Centric Infrastructure (ACI) with Red Hat OpenStack
* Project Contiv and its integration with Cisco ACI
Please mark Mike’s session as a must-attend, slated for June 29, 4.45 PM. We have a double-treat for you with another great speaker, Duane DeCapite, ready to delight you with “Hot topics in Containers, OpenStack and Hadoop”, June 28, 10.15 AM. This session will highlight hot topics related to the convergence of containers and OpenStack, including projects Magnum, Kolla, and Calico. Join us and learn about new communities and products, including Open Container Initiative (OCI), Cloud Native Computing Foundation (CNCF), Cisco NFVI, and related topics.
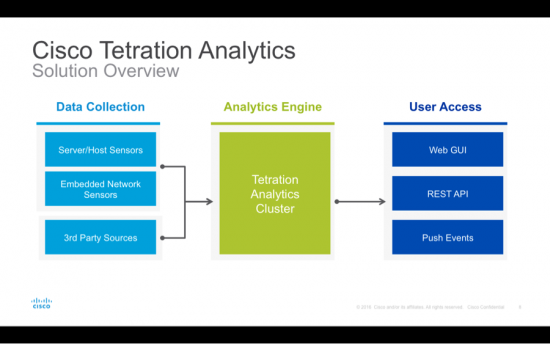
We also have Cisco Theater presentations that run every 20 minutes on ACI, UCS and Cloud topics in the context of OpenStack. They will run Tuesday-Thursday. By attending these sessions, you can gain critical insights into private and public cloud architectures, and the mechanics behind building massively scalable and modern infrastructure, while maintaining increased security and control.
For a full agenda of all the excitement at Red Hat summit, visit the Cisco Red Hat Summit experience.