Research shows that experiential and project-based learning is linked to significant improvements in student test scores, attendance and classroom engagement, as well as improved higher order thinking and problem solving skills and speaks to a broader range of learners.
Additionally, there is a great deal of information about learning modalities that suggest a combination of telling and demonstration work well for information transfer.
I recently participated in “Innovate Together,” a program organized and managed by Cisco’s Services Innovation Excellence Center (SIEC). The program was aimed at teaching students how to identify a problem impacting their community, complete research to validate it, brainstorm solutions, and effectively communicate a solution in a pitch format.
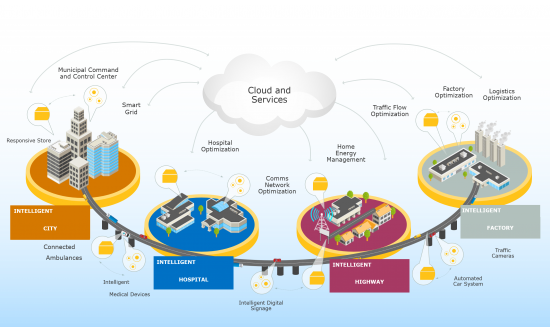
The goal is to positively impact the community by leveraging IoT technology, while allowing students to come out of the traditional classroom setting and asking them to solve real-world scenarios.
With 125 seventh graders from Bay Point Middle School’s Center for Advancement of the Sciences and Technology in Florida participating in the two-day event, sixteen teams were formed. The teams were thoughtfully composed based on test scores, cultural diversity, gender and complimentary skills. And the results were awesome.
The students addressed social conscious and conservation issues with their ideas. Among the problems addressed, which were identified by the students, were proper nutrition for children, feeding the homeless, the opportunity automation is creating for re-skilling the workforce and affordable transportation.
Ten mentors from Cisco, including myself, were on hand to get the creative juices flowing and to foster a problem-solving environment during the event.
The two-day event culminated in an evening award ceremony where the top four groups pitched their problem and solution to a group of their peers, faculty, staff, district administration and family.

After much deliberation, the judging panel chose the winning group, which developed a program around proper nutrition, integrating a wearable component to scan and track food intake and nutrition information. There was also a gaming component included to incentivize kids to use the device for fun and for educational purposes.
The winning team won $250 for their school to either donate to the community charity of their choice or to use to further advance the winning team’s concept.
![IMG_8849[3]](https://blogs.cisco.com/gcs/ciscoblogs/1/IMG_88493.jpg)
The value of learning through real-world experience is invaluable. This is Cisco’s SIEC’s second educational “Innovate Together” event and the reception at each of the schools by faculty, staff, administration and parents has been tremendous. We hope to continue spreading the program across the country.