Cloud brings enterprise technology capabilities to mid-market businesses. As such, mid-sized businesses are rapidly turning to cloud technology to gain a competitive edge.
According to Deloitte’s latest technology survey of mid-market executives, 48 percent are using cloud services and 36 percent have pilot projects underway or are investigating cloud. I believe cloud use to be much higher for mid-market organizations as we have seen that organizations are using 10-15 times more cloud services than they are aware of.
The growing use of known and unknown cloud services presents a new host of challenges for mid-market IT teams, including:
- Lack of cloud visibility as technology spend increasingly shifts to business leaders IT has little ability to identify, monitor, or manage cloud providers
- Cloud risk, security, and compliance concerns
- Rising cloud costs due to duplicate cloud providers
- Limited IT resources to meet increased demand from business groups and manage a mix of public, private and hybrid clouds Continue reading “Cisco Cloud Consumption as a Service Helps Cisco Partners Gain Ground in Cloud & Hybrid IT Conversations”

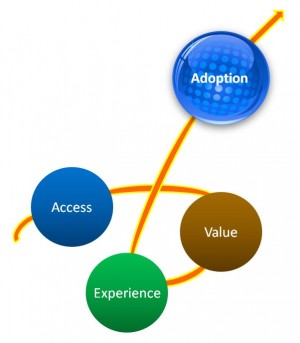 There are multiple factors that help the adoption curve to take off. The three key factors that are very important are:
There are multiple factors that help the adoption curve to take off. The three key factors that are very important are: