Explorations in the spam folder: A sum greater than the parts
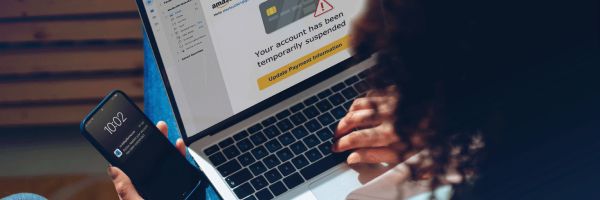
We all know to look out for phishing emails, but sometimes these scams can catch us off guard. Learn to identify minute details that, when brought together, shine light on a larger attack.