This was my first time undertaking SOC duties, eating our own dogfood and drinking our own champaign. 100% worth the time, it was productive, it was challenging, and it was fun! I will definitely do it again!
Instant Attack Verification
In the past few months, I have been involved in the development of the Instant Attack Verification initiative, an Agentic AI framework that aspires to boost SOC analyst productivity by automaticing intelligently lots of the tasks a Tier 1 / Tier 2 analyst does in their day-to-day as they analyze incidents:
- Collect threat intelligence
- Collect logs from various sources
- Analyze the detections in the incident
- Analyze the assets actions in the incident
- Classify the incident: push to Tier 3 for further investigation or close
All these actions take a lot of time, especially when the analyst needs to switch to several products to collect all that information, which heavily add up if we take into consideration the volume of detections produced and seek analyst’s attention. So, the mean time to respond is driven mostly by the time needed to collect information rather than actually analyze.
Agentic AI comes to analyst’s rescue here as most of these mundane tasks can be automated with some Generative AI creativity.
How did Instant Attack Verification do at Cisco Live EMEA 2026?
| Classification | Count |
|---|---|
| Decisive False Positive | 174 |
| Likely False Positive | 2 |
| Likely True Positive | 2 |
| Decisive True Positive | 1 |
During the week of the event (2026-02-07 to 2026-02-13), we generated 179 reports, with the vast majority (97%) of them classified as false positives. This is not surprising: the network monitored is primarily an unmanaged one – Wi-Fi users, venue and exhibitors’ infrastructure. So, mainly, the visibility for Cisco XDR comes from NDR products (Secure Access, Secure Network Analytics, and Secure Firewall data). These detection sources bring in relatively weak signals, leading thus to a high number of low-fidelity incidents. Thus, the rate of FPs is high.
Oh, it’s the cameras! (again…)
Let’s focus on the True Positives though.
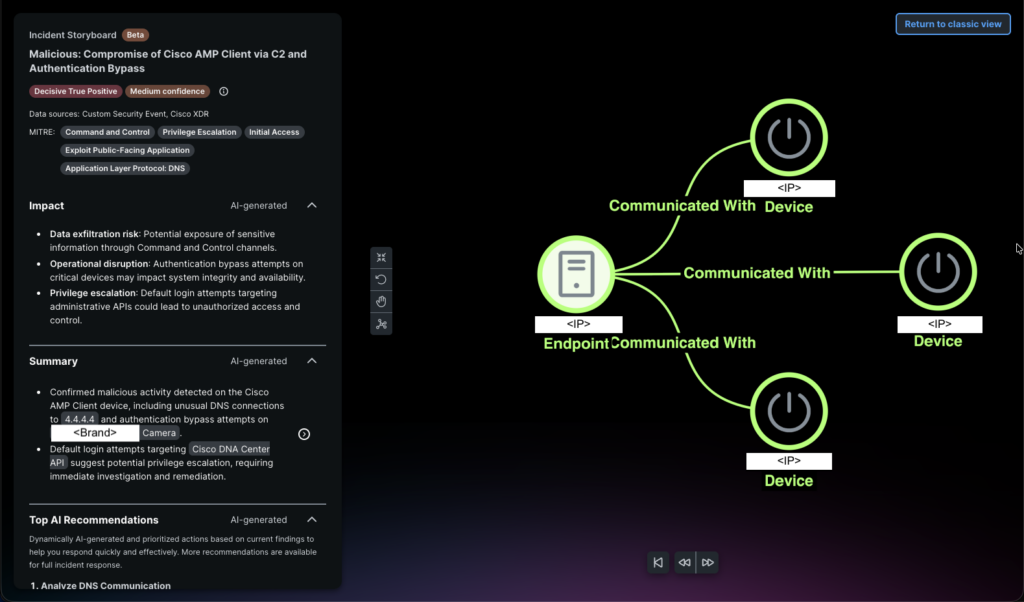
This incident involves 338 detections spanning three distinct activity types from a single source IP:
- repeated authentication bypass attempts against the cameras on multiple targets,
- default credential login attempts against a Cisco DNA Center API,
- and unusual DNS connections to 4.4.4.4.
The combination of tactics — Initial Access (T1190), Privilege Escalation, and Command & Control via DNS — paints a picture of an attacker scanning the internal network for vulnerable IoT devices and management interfaces while maintaining a C2 channel. The sheer volume of attempts from a single source strongly suggests automated exploitation tooling rather than legitimate access.
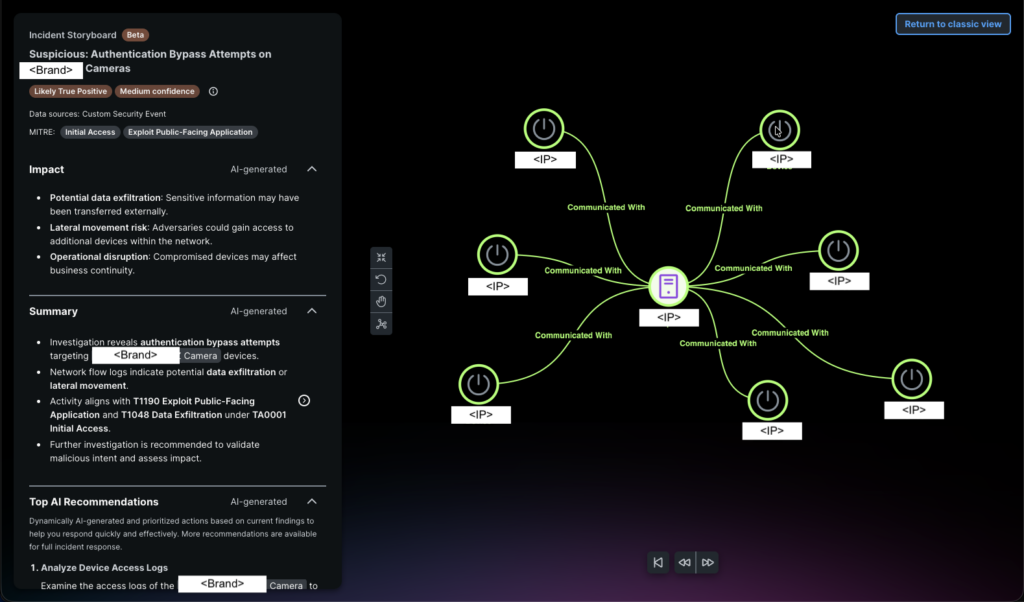
This is essentially a subset of the same activity pattern seen in the prior Incident , with 117 detections — all camera authentication bypass attempts split roughly 55%/45% between LIKELY_TRUE_POSITIVE and LIKELY_FALSE_POSITIVE at the individual detection level. The same source IP is again targeting the same camera endpoints on port 80. The report mentions potential data exfiltration and lateral movement in the summary, but the actual detection data shows only the T1190 exploitation attempts with no corroborating endpoint telemetry or confirmed post-exploitation.
Both incidents stem from the same source IP scanning internal surveillance cameras and (in the first case) Cisco DNA Center. The activity is genuinely suspicious and warrants investigation, but neither report demonstrates confirmed compromise.
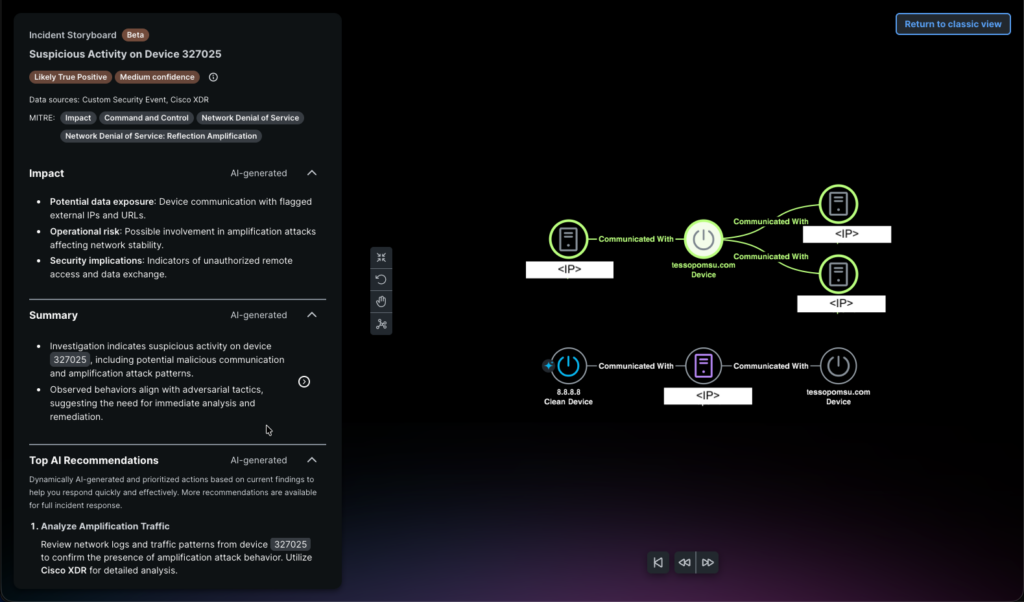
This incident is different from the other two. Device 327025 triggered 10 detections across three distinct categories:
- connections to the malicious URL https[:]//tessopomsu[.]com (flagged by Cisco Talos) hitting two IPs,
- one v4 and another v6,
- ICMP flood alerts exceeding policy thresholds involving 8.8.8.8,
- and a traffic amplification detection suggesting possible botnet participation.
The tactics map to Command & Control (the Talos-flagged URL) and Impact/DoS (the ICMP floods and amplification). The timeline spans Feb 11–12, 2026, with the amplification alert firing first, followed by the malicious URL connections and ICMP floods over the next day.
Concluding
Instant Attack Verification proved its value during the week at Cisco Live EMEA 2026. In an environment where NDR-heavy detection sources generated 179 incidents — the vast majority low-fidelity — the agent autonomously triaged every single one, correctly dismissing 176 as false positives while surfacing three genuinely suspicious incidents for analyst review.
Without this automation, a human analyst would have needed to manually investigate each of those 179 incidents: pulling logs, enriching entities, cross-referencing threat intelligence, and building context. Instead, Instant Attack Verification did that work in minutes per incident, producing structured reports with MITRE ATT&CK mappings, confidence scores, and prioritized recommendations. The time saved is substantial — what would have consumed the better part of a SOC analyst’s week was reduced to reviewing three pre-analyzed reports and validating the agent’s reasoning.
More importantly, this exercise highlighted both the strengths and the honest limitations of the approach. The agent correctly identified the camera exploitation campaign and the Talos-flagged C2 activity as threats worth escalating, demonstrating that it can separate signal from noise even in a challenging, unmanaged network environment. At the same time, the medium confidence scores and occasional narrative inflation remind us that Instant Attack Verification is a force multiplier for analysts, not a replacement — the human still makes the final call. That is exactly the workflow we are building toward: let the agent handle the time-consuming collection and initial analysis, and let the analyst focus on what they do best — making judgment calls on the cases that matter.
Check out the other blogs from our SOC team in Amsterdam 2026.
We’d love to hear what you think! Ask a question and stay connected with Cisco Security on social media.
Cisco Security Social Media





