1. Introduction: The SOC at the Heart of Cisco Live
Every year, Cisco Live brings together thousands of technology professionals, engineers, and security practitioners under one roof. What many attendees may not realise is that, running silently in the background, a dedicated Security Operations Centre (SOC) is watching over every packet, every connection, and every endpoint on the conference network — in real time.
The Cisco Live SOC operates around three core pillars:
- Protect: Safeguarding the Cisco Live network from both internal and external threats.
- Educate: Engaging attendees through SOC tours, live demonstrations, and published blog content.
- Innovate: Continuously improving analyst workflows through new integrations, automations, and tooling that reduce repetitive tasks and shorten investigation times.

This blog is a first-hand account of a real investigation I conducted during Cisco Live Amsterdam 2026. It walks through the detection of a malicious file delivered via email, from the first alert in Cisco XDR all the way through to full packet-level analysis using Splunk to Wireshark and Endace. The aim is to provide a transparent, practitioner-level view of how modern SOC tooling — Cisco XDR, Splunk Attack Analyzer (SAA), Cisco Secure Malware Analytics (SMA), and Endace — works together to uncover a threat in a live, high-pressure environment.
2. The Incident: First Contact in Cisco XDR
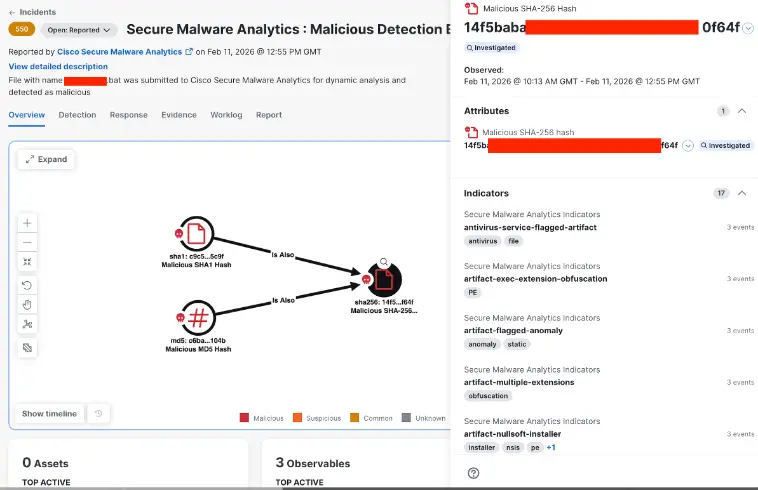
The investigation began with an incident surfacing in the Cisco XDR user interface. The alert was clear: a file had been submitted to Cisco Secure Malware Analytics and flagged as malicious. The incident priority was scored at 550, and the report came in on 11 February 2026 at 12:55 PM GMT.
The key detail in the incident description captured my attention immediately.
File with name xxxxxxxxxx.bat was submitted to Cisco Secure Malware Analytics for dynamic analysis and detected as malicious
The file name itself was a signal worth noting. A .bat (batch) extension is a classic vehicle for executing commands on Windows hosts. The naming convention — while not technically obfuscated — had a deliberate quality to it that warranted immediate investigation.
The XDR incident graph confirmed three critical artefact hash links.
All three hashes cross-referenced to the same underlying malicious artefact, connected via a relationship chain in the XDR correlation graph as you see below. The Attributes panel surfaced various distinct indicators, which are covered in depth later in this analysis.
3. Triage in Splunk Attack Analyser
With the initial alert confirmed in XDR, the next step was to pivot into Splunk Attack Analyzer (SAA) to gather context around the file’s submission and deepen the artefact investigation.
3.1 Locating the File Submission
As part of the tooling for the SOC, I used the SAA, an automated malware and threat analysis platform that provides SOC analysts with rapid, multi-engine inspection of suspicious files and URLs. When a file is flagged (in this case a RAR archive submitted directly via API integration with Endace), SAA orchestrates a coordinated analysis across multiple detection engines simultaneously, including Cisco Secure Malware Analytics, Web Analyzer, Static File Analysis,
Static Document Analysis, Archive Extraction, YARA rule matching, URL Reputation, Email Analyzer, and an AV engine.
This multi-layered approach ensures that no single analysis technique is relied upon in isolation, dramatically increasing the probability of detection across different threat vectors. Crucially, SAA also performs archive extraction, automatically unpacking compressed files like the RAR archive shown here to reveal and analyze the nested content within. In this case exposing a malicious .bat script concealed inside.
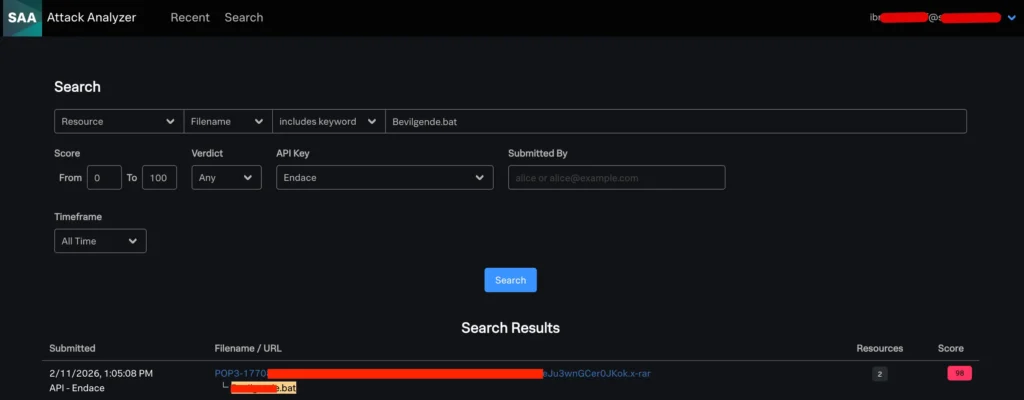
The platform records critical file metadata including SHA256 hash and file size, enabling analysts to cross-reference findings against external threat intelligence databases and preserve chain-of-custody evidence for incident documentation. By automating what would otherwise be a time-consuming, manual detonation and triage process, SAA dramatically accelerates the investigation workflow, allowing Tier 1 and Tier 2 analysts to move quickly from detection to a confident, evidence-backed escalation decision.
In Splunk, a score of 98 is essentially the ceiling of confidence for malicious classification within the SAA framework. This was not a borderline detection, but the system had high certainty.
The resources analyzed confirm the parent-child relationship too.
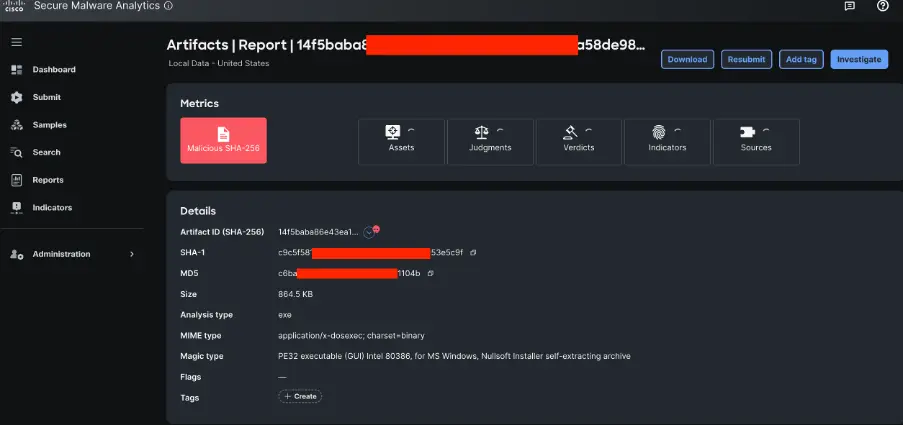
3.2 File Metadata Breakdown
Drilling into the full submission record revealed the following metadata:
Two points stand out:
- First, the file was delivered as a RAR archive (.x-rar), a compressed container, with the .bat file nested inside. This delivery technique allows the outer archive to bypass many email gateway filters that inspect only surface-level file extensions, while the inner payload carries the actual malicious logic.
- Second, the analysis duration is notable. SMA spent approximately seven minutes on the full pipeline, but two minutes was boot time for the sandboxed environment. The effective analysis time was around three minutes, fast enough to inform a live SOC investigation without creating unacceptable triage delays.
4. Deep Dive: SMA Analysis
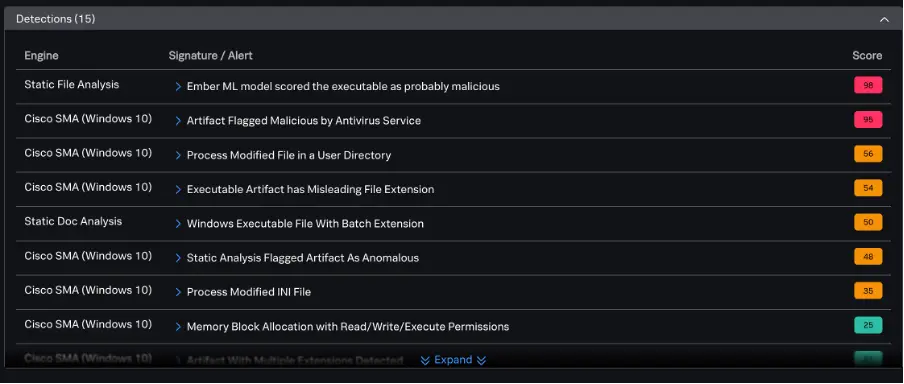
The 15 detections surfaced by SMA tell a rich story. Below is a breakdown of the key findings, split by analysis type and severity score.
What is SMA used for? Formerly known as Threat Grid, Cisco’s dedicated dynamic malware analysis platform (now Secure Malware Analysis).
When a suspicious file is submitted, (whether manually or automatically via API integrations with tools like Endace and SAA) SMA perform a static analysis of the suspicious first and then if further analysis is deemed necessary, it detonates it inside an isolated sandbox, observing real-time behaviors that static analysis alone would miss, such as suspicious process execution, network callouts, and file system changes. It then correlates findings against a global threat intelligence database, generating a threat score and detailed behavioral indicators to help analysts quickly determine severity and intent. Its tight integration with Cisco ecosystem, including XDR ensures findings feed directly into the broader incident timeline, enabling fast, evidence-backed escalation decisions.
4.1 Detection Summary
SMA did both static and dynamic analysis: A summary of the analysis carried out is shown below.
A standard Windows 10 environment (virtual machine or VM) ran the suspected samples. This was the ideal environment determined to test how the sample interacts with the system. SMA include anti-evasion techniques, we term this “outside look approach”. We give everything the sample
needs including exit nodes, mouse movement, Windows focus changes without letting the malware know it is running in a simulated environment.
4.2 What the Detections Tell Us
Static analysis was the first to fire, with the Ember ML model scoring the file at 98, the highest possible confidence from a machine learning perspective. Ember is a well-regarded ML framework for PE file classification, and a near-perfect score is a strong leading indicator of genuine malicious intent.
The ‘Executable Artifact has Misleading File Extension‘ and ‘Windows Executable File With Batch Extension‘ detections confirm what the metadata already hinted at: the file was masquerading as a .bat script while behaving like a Windows executable binary. This is a classic obfuscation technique used to confuse both automated filters and human analysts.
Dynamic analysis on the Windows 10 sandbox environment revealed active runtime behaviours:
- Process modification of files in a user directory: indicative of the malware writing or altering persistence mechanisms.
- Process modification of an .ini file: a technique sometimes used to hijack application configuration or establish environment variables for subsequent payload stages.
- Memory block allocation with Read/Write/Execute permissions: a hallmark of shellcode injection, where an attacker allocates memory with all three permissions to write and immediately run malicious code without touching disk.
From a combined static and dynamic perspective, this file exhibits the profile of a multi-stage dropper or loader: it arrived compressed in a .RAR archive, uses a misleading extension to evade
surface-level filtering, and at runtime performs memory manipulation and file system modifications consistent with persistence or secondary payload delivery.
5. Following the Trail: Splunk and the Email Delivery Chain
With the artefact characterised, the natural next question was: how did this file get onto the network? This is where Splunk search capabilities became essential.
5.1 Uncovering the POP3 Communication
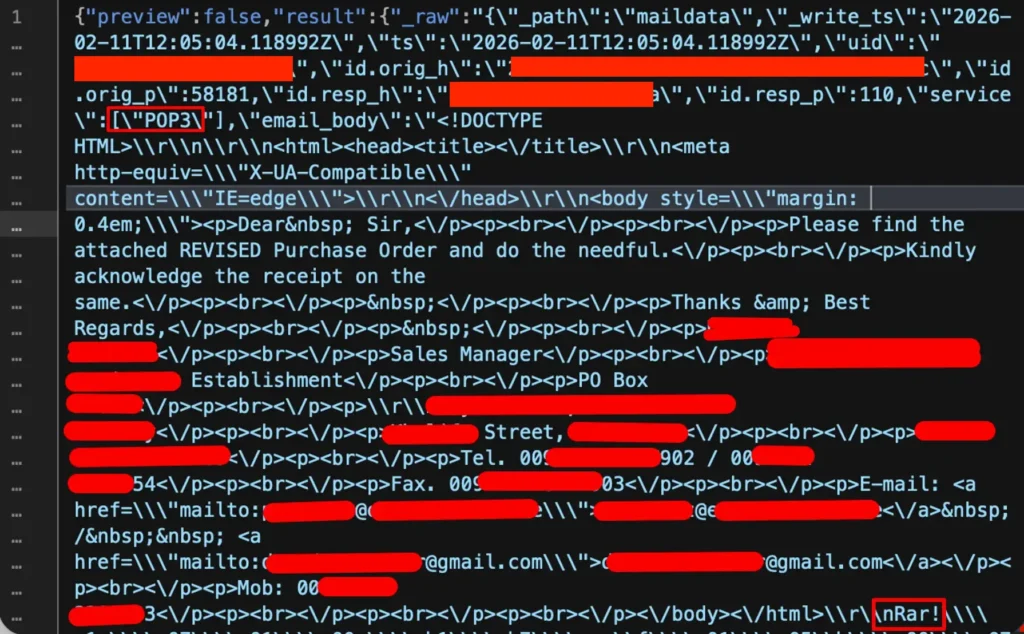
A targeted Splunk search against mail data logs revealed the delivery mechanism clearly. The logs showed a POP3 communication event timestamped 11 February 2026 at 12:05 PM, which contained the full email body in plain text.
This is an important finding in its own right. POP3, unlike IMAP over TLS or modern secure email protocols, frequently transmits mail in cleartext. This means the entire email, including attachments and credentials, can be intercepted and read on the wire. In a conference environment where potentially thousands of devices connect to shared infrastructure, this represents a significant exposure.
The email body was a classic Business Email Compromise (BEC) lure: a ‘Dear Sir’ message requesting the recipient to ‘find the attached REVISED Purchase Order and do the needful,’ signed off by a ‘Sales Manager’ with a legitimate-looking business address.
This social engineering hook was designed to create urgency around a financial document, a proven technique to prompt recipients to open attachments without scrutiny. For privacy reasons I redacted the personally identifiable details which included names, email address, phone number and physical address which in this case happen to be somewhere in the Middle East.
5.2 Splunk Sample Upload Watcher Log
Cross-referencing with the sample uploader log on host Endace provided the operational link between the network capture and the SMA submission.
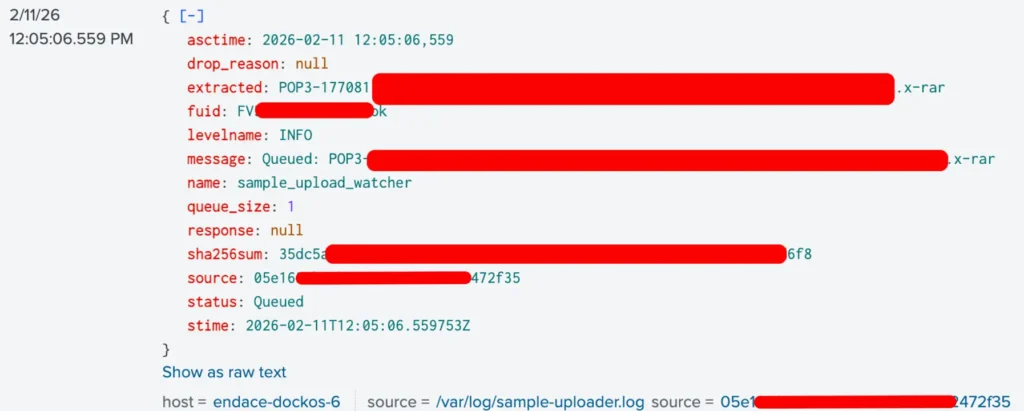
This log entry confirms that Endace, operating as a network packet capture and traffic intelligence platform, automatically extracted the RAR attachment from the POP3 stream and queued it for analysis via the SAA API. The automation pipeline worked exactly as designed: no manual analyst intervention was required to pull the file.
6. Packet-Level Confirmation: Wireshark via Endace
To fully corroborate the findings and obtain ground-truth evidence of what traversed the wire, Wireshark was launched through the Endace UI; a workflow that allows analysts to pivot from Endace’s traffic intelligence layer directly into full packet inspection without leaving the investigation environment.
6.1 The Raw Traffic
Examining the raw traffic content in Splunk confirmed this was someone sending an email to another party with a malicious attachment. The JSON-encoded mail data exposed the full POP3 service indicator and the complete HTML email body, including the social engineering content and the embedded RAR attachment bytes at the end of the stream.
6.2 What the PCAP Revealed
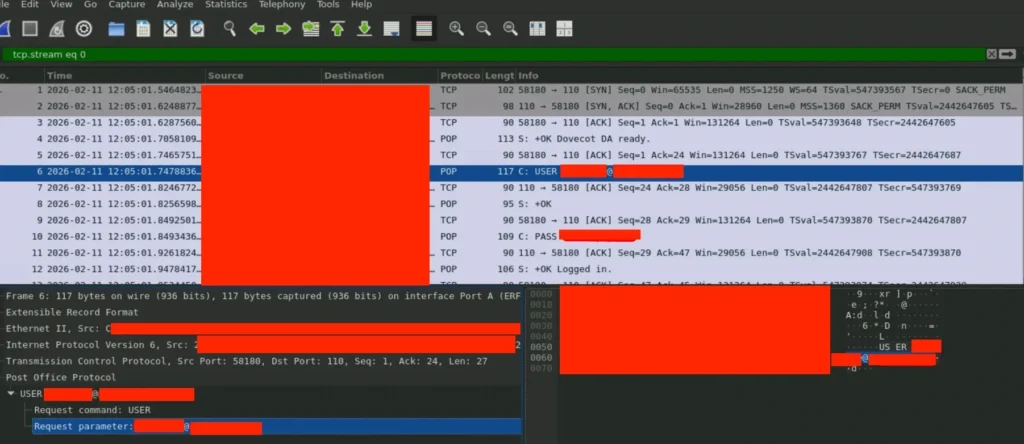
The TCP stream in Wireshark confirmed a POP3 session between two endpoints, with the full email transmitted in cleartext. The stream established with a standard POP3 handshake.
The USER command was captured in full, including the plaintext email address used for authentication. Subsequent frames revealed the password being transmitted equally unencrypted, a stark demonstration of the risks of unencrypted POP3 in any environment.
Within the body of the retrieved email, the RAR attachment was embedded and visible in raw form, with the Rar! magic bytes identifiable at the tail of the email body. This confirmed the presence of the RAR archive and its delivery via this unencrypted channel.
The Wireshark capture validated every element of the investigation chain:
- Email delivered via POP3, cleartext, no encryption
- Malicious RAR attachment present and extractable from the email stream
- Sender and recipient email credentials exposed in transit
- Endace correctly extracted and queued the attachment for SMA analysis
7. XDR Indicators: The Full Picture
Returning to the XDR UI, multiple Indicators surfaced against the malicious SHA-256 hash can now be fully contextualised against the investigation findings.
The artifact-exec-extension-obfuscation behavioral indicator is particularly telling; as this is precisely what it is designed to surface when a file uses a misleading extension. The artifact-multiple-extensions behavioral indicator reinforces the RAR-within-BAT delivery structure observed at the file metadata level.
8. Tools Used in This Investigation
| Tool | Role in Investigation |
| Cisco XDR | Incident aggregation, artefact correlation, and initial triage |
| Cisco Secure Malware Analytics (SMA) | Dynamic and static file analysis, sandbox detonation |
| Splunk Attack Analyzer (SAA) | File submission tracking, risk scoring, resource analysis |
| Splunk Cloud | Log search, POP3 communication reconstruction, mail data correlation |
| Endace | Full packet capture, traffic intelligence, automated file extraction, Wireshark integration |
| Endace (Wireshark) | Deep packet inspection, TCP stream analysis, credential and attachment extraction |
9. Key Takeaways for the SOC Community
This investigation, while contained and resolved, surfaces several important lessons for SOC practitioners operating in dynamic, high-density network environments:
- POP3 is a Liability. Unencrypted POP3 exposed both email credentials and the malicious attachment in full on the wire. In any environment, conference, coffee shop, hotel or corporate network, email traffic should be enforced over TLS.
- Archive Containers Remain an Effective Evasion Technique. Wrapping malicious payloads inside RAR archives continues to succeed at bypassing perimeter controls. Email gateways should perform recursive archive inspection, and sandboxing solutions should be configured to extract and analyse nested files.
- Extension Obfuscation is Low-Effort, High-Impact. Renaming a Windows PE (.exe – portable executable) file with a .bat extension costs an attacker nothing but can defeat rule-based detection relying on extension matching. Detection must be grounded in file magic bytes and binary analysis, not extension alone.
- Integrated Tooling Accelerates Triage Dramatically. The Endace → SAA → SMA pipeline reduced the time from packet capture to confirmed malicious classification to minutes. This level of automation is what allows a small SOC team to cover the breadth of a large network effectively, such as the Cisco Live conference.
- BEC Lures Continue to Work. A fake purchase order from a ‘Sales Manager’ is not sophisticated, but it does not need to be. User awareness and endpoint controls remain the last line of defence when delivery succeeds.
10. Conclusion
In the span of a few minutes, a malicious RAR file, (delivered via an unencrypted POP3 email session) was detected, extracted, sandboxed, scored at 98/100 for maliciousness, and fully investigated down to the raw packet level. No significant analyst dwell time. No manual handoff between tools. Just a tightly integrated pipeline doing exactly what it was designed to do.
The Cisco Live SOC exists not just to protect the conference network, but to demonstrate in a live environment that the vision of a modern, automated SOC is not aspirational; it is operational today. This investigation is one small example of that reality in action.
If you would like to learn more about the tools and integrations used here, visit the Cisco Events SOC page and read the white paper.
Check out the other blogs from our SOC team in Amsterdam 2026.
Finally, listen to my weekly podcast, YusufOnSecurity through apple podcast, Spotify or wherever you get your podcast.
We’d love to hear what you think! Ask a question and stay connected with Cisco Security on social media.
Cisco Security Social Media





