Additional Contributor: Sumit Juyal
Working as a Threat Hunt Analyst with Splunk in the Security Operations Centre (SOC) at GovWare 2025 has proved to be both enjoyable and challenging. We frequently observed infected hosts connecting to the conference network and engaging in unauthorized activities. Our primary objective was to detect any such activities occurring across the network, report them, and implement preventive measures.
Overview
This writeup provides insights into one of the hunts conducted using Splunk to identify hosts that connected to the conference guest network and made a high number of suspicious network connections.
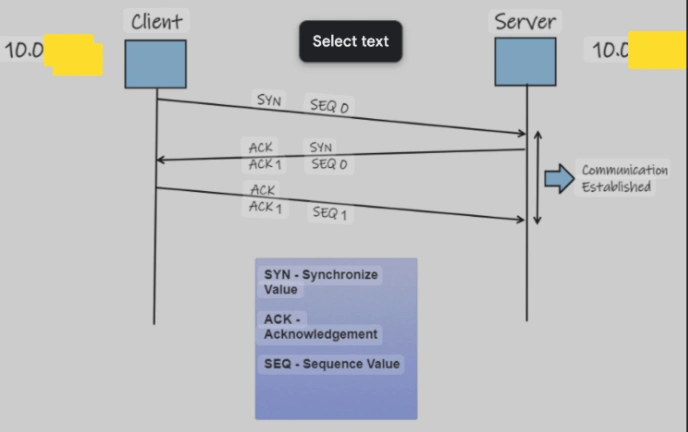
Before we embark on our investigation, let us first take a closer look at the characteristics of a standard TCP connection (this will be helpful for understanding the finding). In a typical TCP handshake, a client initiates the connection request by sending a SYN packet. The server then acknowledges this request by responding with a SYN + ACK packet. Upon receiving this acknowledgment, the client replies with an ACK packet.
Investigation
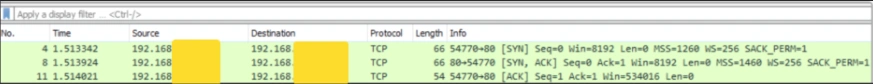
We began our search by identifying the internal IPs in the firewall logs; that were making many network connections; (e.g. generating greater than 5,000 events).
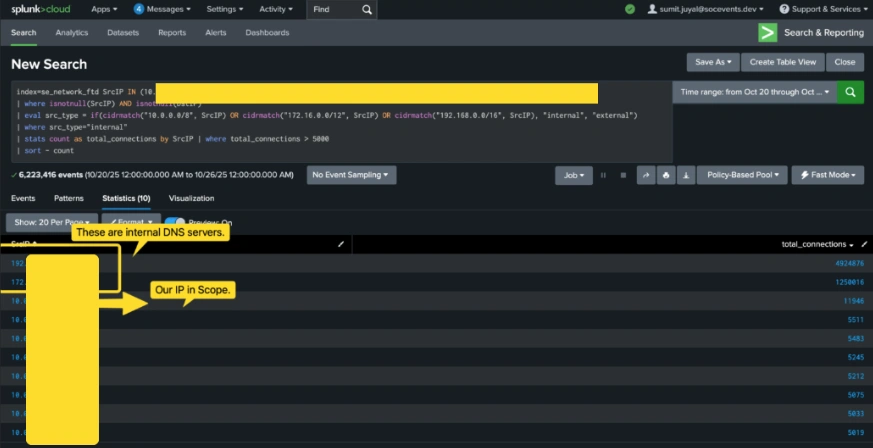
We scoped our hunt to the internal IP: 10.0.X.X, as the number of requests from this IP was significantly higher. We pivoted to the Splunk firewall logs to take a closer look at the external IPs and ports that it was connecting to… In the screenshot below, we can see that the host is establishing numerous outbound connections to external IP’s, mainly on port 443.
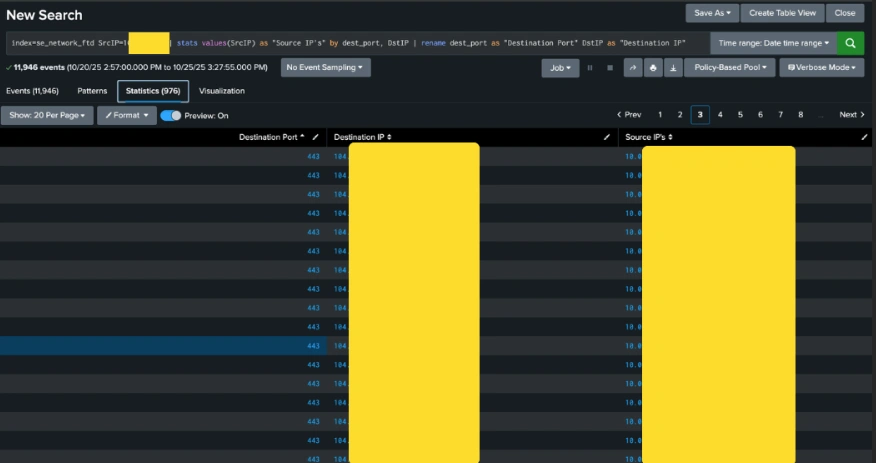
To gather more insights about these connections, we took a closer look at the traffic flowing into Endace, our full packet capture tool.
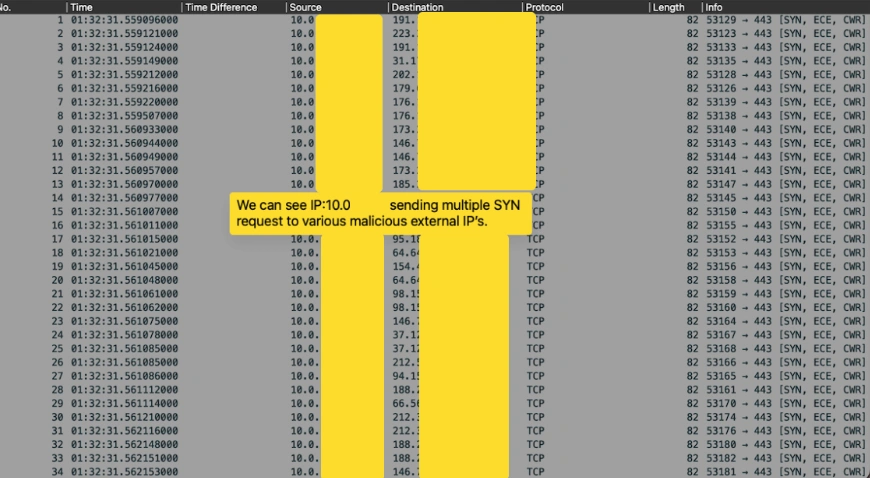
We can clearly observe that host 10.0.X.X is sending multiple TCP SYN packets on port 443, without waiting for a response from the server. This suggests that these are not your usual TCP handshake requests; instead, they appear to be crafted TCP requests originating from the infected host and targeting multiple external IPs.
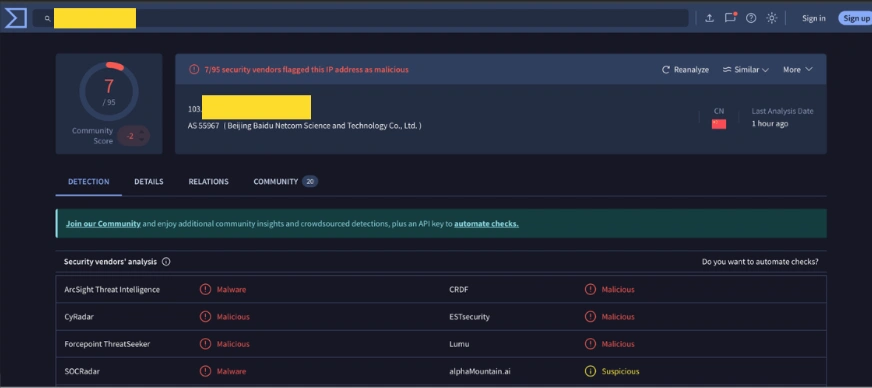
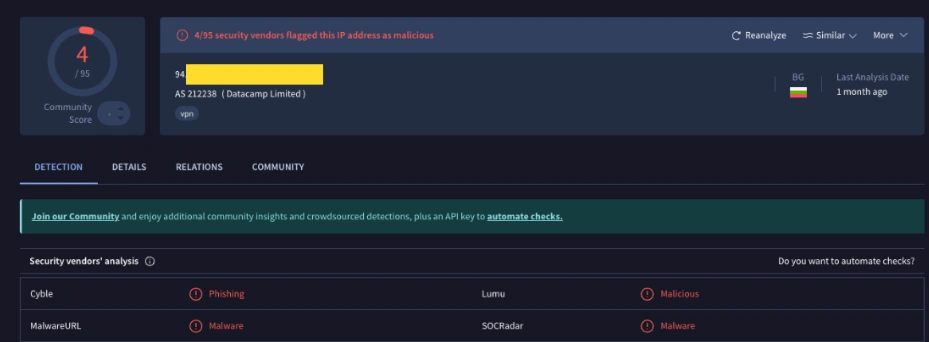
Below are the IP reputations of some of the external IPs from Virus Total (an OSINT tool we use) to gather more details about them. As we can see, most of the IPs have a bad reputation and are associated with abusive usage over the internet.
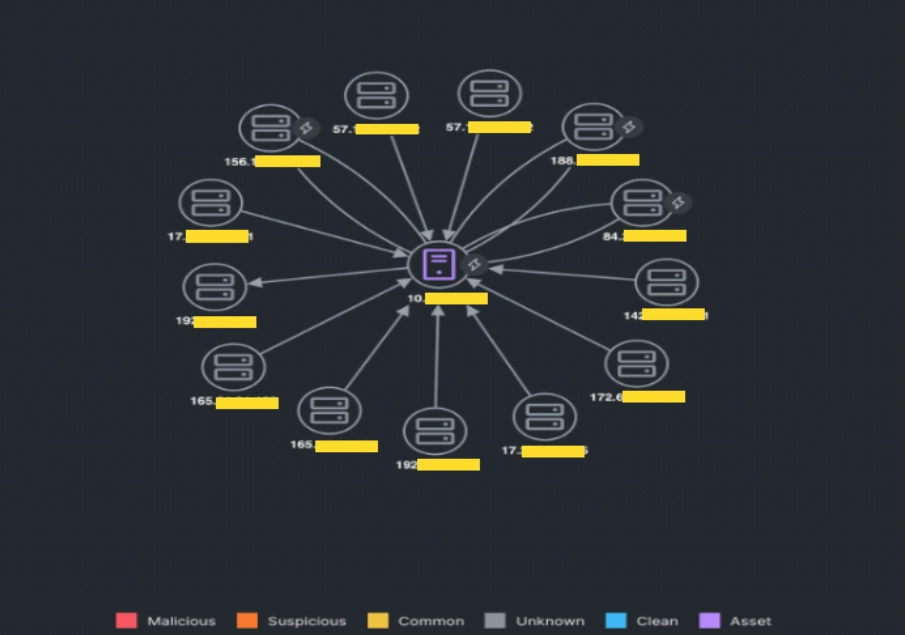
Later, we received an alert from Cisco XDR for the same host. The depiction from XDR shows the same hypothesis we had from our hunt.
We reported the incident to GovWare management and successfully blocked the inbound malicious traffic aimed at all hosts connected to the guest network. It’s quite common at security conferences to see endpoints scanning and connecting to malicious domains/IPs, especially as attendees link a variety of personal devices to the network. However, we’re always on the lookout for such attempts and have preventive network measures in place to make it tough for attackers to exploit the conference network for any malicious activities.
Check out the other blogs by my colleagues in the GovWare SOC.
About GovWare
GovWare Conference and Exhibition is the region’s premier cyber information and connectivity platform, offering multi-channel touchpoints to drive community intel sharing, training, and strategic collaborations.
A trusted nexus for over three decades, GovWare unites policymakers, tech innovators, and end-users across Asia and beyond, driving pertinent dialogues on the latest trends and critical information flow. It empowers growth and innovation through collective insights and partnerships.
Its success lies in the trust and support from the cybersecurity and broader cyber community that it has had the privilege to serve over the years, as well as organisational partners who share the same values and mission to enrich the cyber ecosystem.
We’d love to hear what you think! Ask a question and stay connected with Cisco Security on social media.
Cisco Security Social Media





