In cybersecurity, we often talk about “drinking from the firehose” — that relentless, high-velocity stream of telemetry, alerts, and emerging threats that can overwhelm even the most seasoned professional. At Cisco, we counter that with another philosophy: “drinking our own champagne.”
We don’t just build security tools; we live in them, stress-test them in hostile environments, and validate their worth before they ever reach a customer’s dashboard.
For the last 2.5 years, my role as a Systems Engineer within the XDR (Extended Detection and Response) incubation team has been defined by these two concepts. It’s been a journey of rapid innovation and high-pressure deployments, requiring a constant balance between cutting-edge “new” telemetry and “tried-and-true” networking fundamentals.
The 48-Hour Challenge: Standing Up a SOC
Nothing tests your mettle quite like the “SOC-in-a-Box” experience. Imagine walking into an empty room and having exactly 48 hours to stand up a fully functional Security Operations Center (SOC) capable of protecting a network the size of a small city. This isn’t a simulation. Whether it’s for Cisco Live or a major industry event, we have a razor-thin window to deploy the stack, configure integrations, and begin active hunting. It is the ultimate “firehose” moment. You aren’t just installing hard- and software; you are orchestrating an ecosystem that must be bulletproof from the moment the first attendee connects.
The Delta Logic: Layered Defense in the Lowlands
Standing in Amsterdam for Cisco Live, the parallels between digital defense and the physical landscape of the Netherlands are striking. For centuries, the Dutch have battled a different kind of firehose: the North Sea. Following the devastating Watersnoodramp (flood) of 1953, the Dutch realized a single wall wasn’t enough. They built the Deltawerken (Delta Works)—the world’s most sophisticated flood defense. Its genius lies in its layered approach, a philosophy that mirrors a modern SOC.
- The Algerakering (Foundational Infrastructure): As the first component of the Delta Works, the bridge annex flood barrier was built to protect the densely populated hinterland. In our world, this is Cisco Secure Network Analytics (SNA) and NetFlow. It is the steady, reliable infrastructure that ensures the ground remains solid and the “water levels” (traffic) are constantly monitored.
- The Oosterscheldekering (The Dynamic Gatekeeper): This is our Cisco Firepower Threat Defense (FTD). The Oosterscheldekering is a unique storm surge barrier designed to stay open to allow the natural tide to flow, preserving the ecosystem. But the moment a storm surge is detected, its massive gates drop to protect the land. FTD operates on this exact principle: it allows the vital flow of business traffic at scale, but it has the intelligence to recognize a “storm” and instantly blocks malicious traffic, protecting the internal ecosystem without stifling it.
- The Maeslantkering (Intelligent Surge Barrier): These massive, automated gates close only during the most extreme conditions. This is our Cisco XDR and Splunk layer—providing high-level, intelligent orchestration that reacts to sophisticated, multi-vector attacks in real-time, closing the final gates before the network is flooded.
Just as the Dutch don’t rely on a single dike, we don’t rely on a single tool. We build layers: from the foundational “bridges” of NetFlow to the “dynamic gates” of FTD and the “intelligent surge barriers” of XDR and Splunk.
The New Guard: Splunk and Endace
Being an SE means being at the tip of the spear for Cisco’s strategic integrations. For me, this meant a deep dive into the Splunk ecosystem and Endace packet capture.
- Splunk & Splunk ES: Since the acquisition, the synergy between Cisco XDR and Splunk Enterprise Security (ES) has become our North Star. Pivoting from an XDR incident into a Splunk ES correlation search in real-time is like learning a new language while delivering a speech. It’s fast, powerful, and changes how we process data at scale.
- Endace: When “PCAP or it didn’t happen” is the mantra, Endace is our source of truth. Integrating always-on packet capture allows us to move from a high-level alert to the granular “ground truth” of a packet in seconds.
Falling Back on Experience: The Power of SNA Flowtables
When you are neck-deep in new telemetry and the firehose is at full blast, you need a tether to reality. For me, that tether is SNA Flowtables.
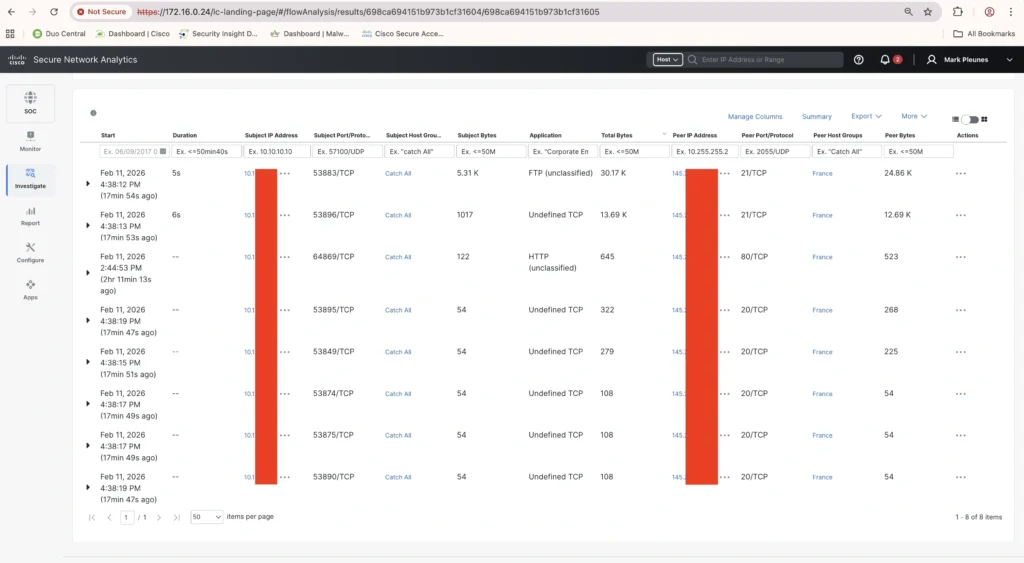
While XDR provides the broad strokes and Splunk provides deep analytics, digging into SNA Flowtables is like coming home. There is a “muscle memory” in analyzing NetFlow. When a lateral movement alert pops up in XDR and I’m still navigating a new Splunk dashboard, I can always fall back on the Flowtables to see exactly who talked to whom, when, and for how long. It’s a reminder that while tools evolve, the “Algerakering” of networking fundamentals remains essential.
The Anatomy of a Catch: From Alert to Ground Truth
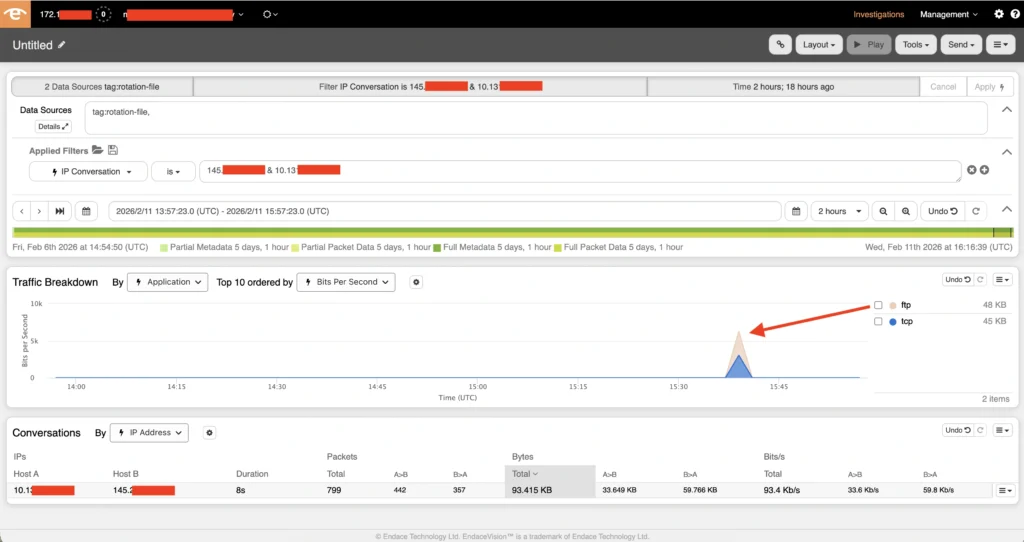
During a shift as a SOC Tier 1 analyst, the firehose delivered something curious: “FTP command anomalies by 145[.]x[.]x[.]x.” My immediate thought? It’s 2026—why are we seeing cleartext protocols heading to the open internet?
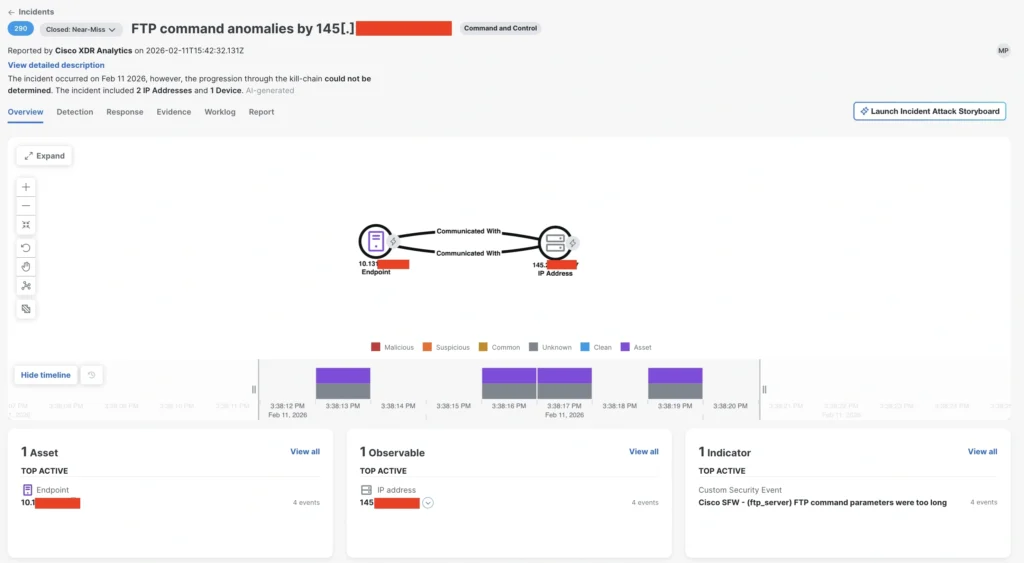
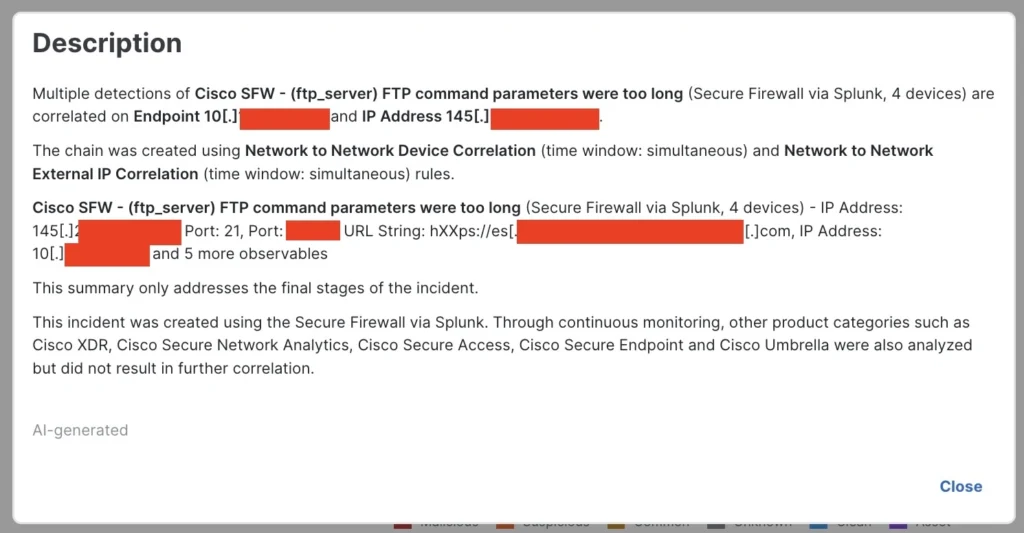
I began triage in Cisco XDR; it was an attendee’s machine that communicated with a European financial institution; the latter made this even more interesting.
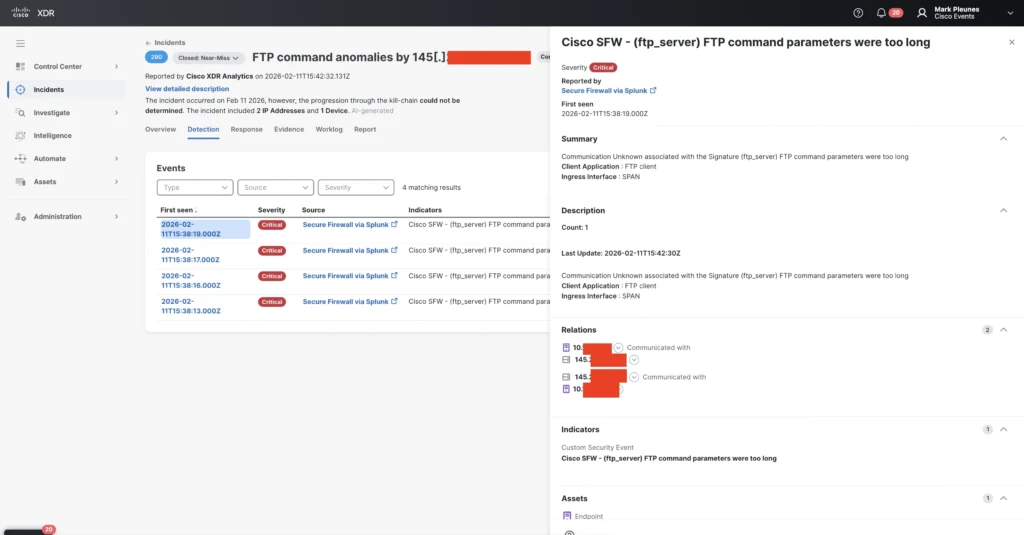
Since we lack insights into attendee endpoints; we do not deploy tools like Cisco Secure Endpoint, the Network Visibility Module, or XDR Forensics on these machines, it was a bit harder to get to the bottom of this. However, I was determined to see how far I could push our integrated “champagne” stack before escalating, using the following steps:
- Verification: I used SNA Flowtables to verify the traffic and timeframe. I set the timeframe intentionally quite broad to see if we have seen any other traffic to and/or from this destination IP address.
- Querying: I turned to CircuIT—Cisco’s AI assistant—to help bridge the gap, asking it to draft the specific Splunk SPL query needed to investigate the traffic further.
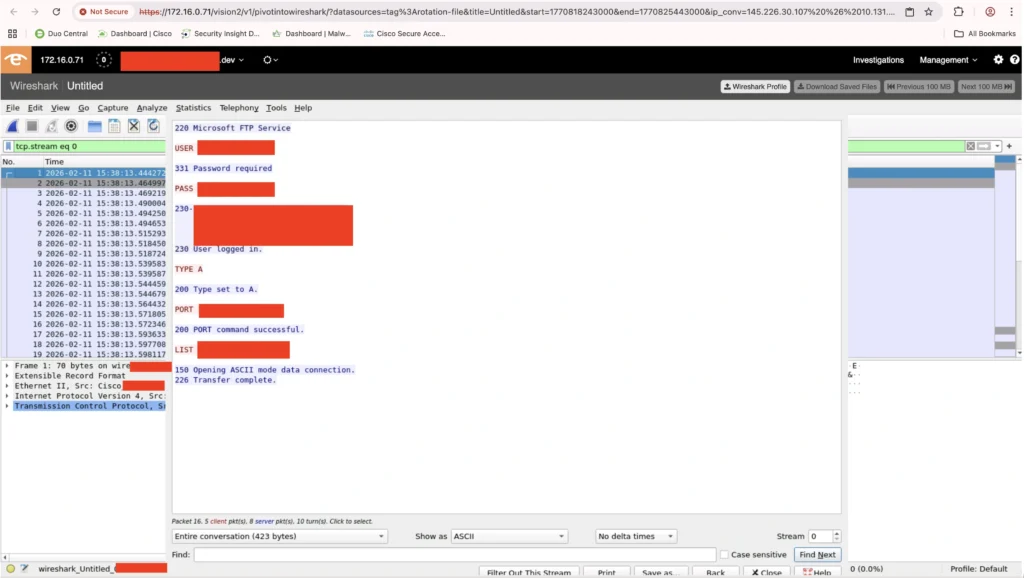
- Ground Truth: I moved to Endace to pull the raw packets. The evidence was undeniable: data was being exchanged via cleartext FTP.
Based on my findings, I suspected the server was hosting an update service for a security tool, but to be certain, I engaged a Tier 3 analyst, by escalating the XDR Incident to Splunk ES.
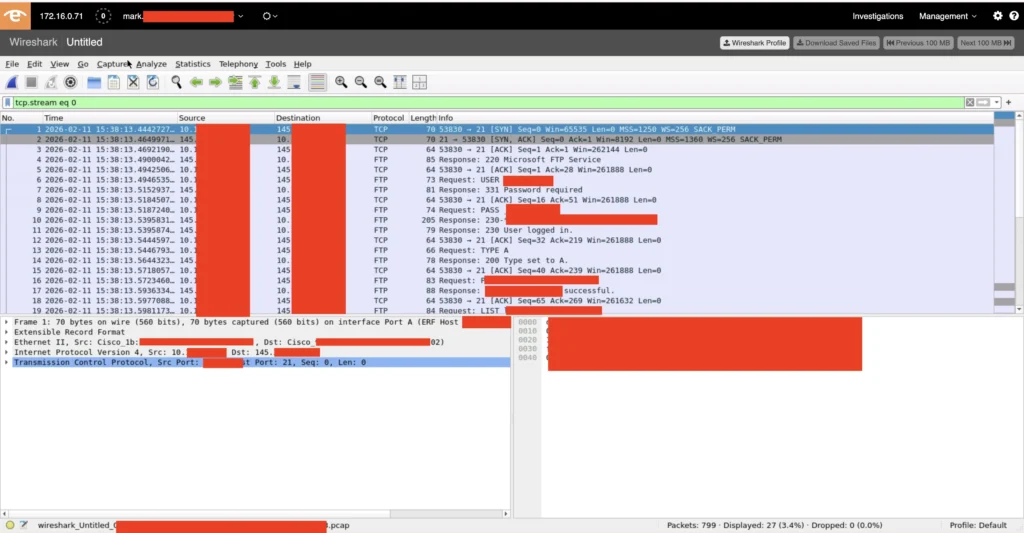
We extracted the ZIP file from the Endace packets and analyzed its contents.
After comparing file hashes against the Cisco Talos database and third-party feeds, the result was clear: the content of the ZIP file was benign.
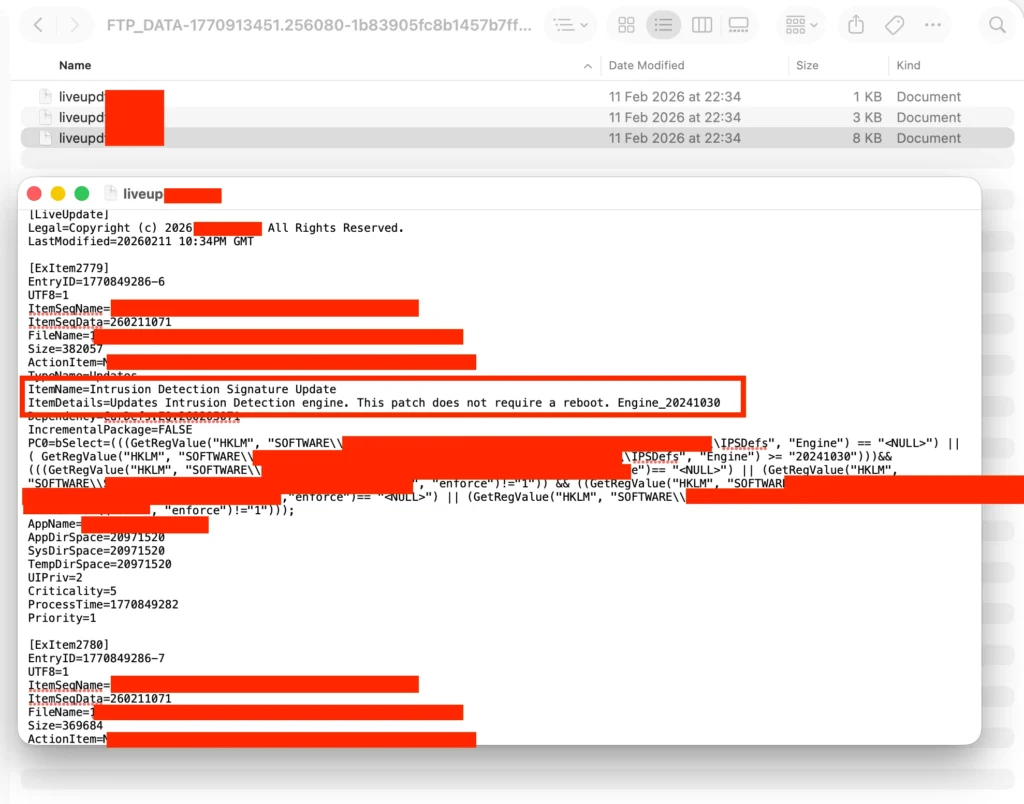
The irony was stark: a security product was reaching out to its update server over an unencrypted channel. Given the current climate of supply chain attacks, it was a reminder that even the tools we trust must be scrutinized. Watching the Tier 3 analyst reverse-engineer the detection was a masterclass in methodology. For me, it was like learning from a sommelier—uncorking the data, tasting the nuances of the traffic, and explaining the “notes” of a complex investigation.
The Champagne Taste
“Drinking our own champagne” means working in a fast-changing world where the products are not always glamorous. Sometimes the champagne is still fermenting, and you find the bubbles—or the bugs—before anyone else does. But that’s the point.
However, as any connoisseur will tell you, the best champagne is always shared with friends. In the high-pressure environment of an event like Cisco Live, those friends are the engineers and analysts from the Cisco Security, Splunk, and Endace teams. We aren’t just “drinking” the tech in isolation; we are collaborating in real-time, sharing insights across different platforms, and refining the vintage together. It’s this collective expertise—the “sommeliers” of the SOC—that turns a collection of disparate tools into a unified, battle-hardened shield.
By pushing technology like XDR, Splunk, and Endace to their limits alongside the best in the business, we ensure that when our customers use these tools, they aren’t just surviving the firehose—they’re mastering it. After 2.5 years of incubating the future of XDR, I’ve learned that the best way to stay ahead of the threat is to never stop learning the new, never forget the power of the foundations, and always ensure you’re surrounded by a world-class team.
Check out the other blogs from our SOC team in Amsterdam 2026.
We’d love to hear what you think! Ask a question and stay connected with Cisco Security on social media.
Cisco Security Social Media





